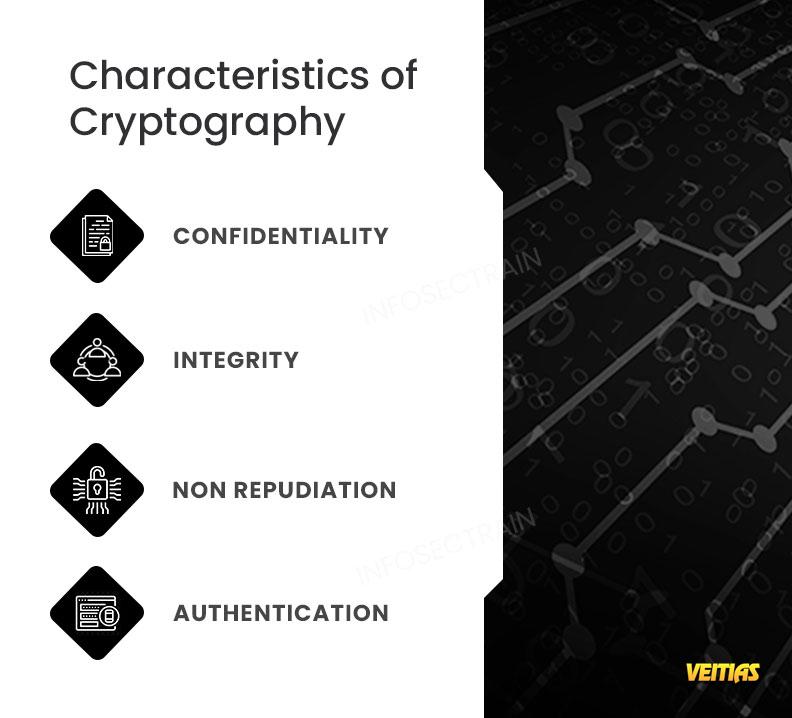
Characteristics of cryptography
Cryptography is a combination of keys (factors) and algorithms (logic) used for data security. It includes different methods and technologies to secure data, such as encryption, decryption, hashing, digital signature, etc. In cryptography, we use two types of encryption techniques: Symmetric and Asymmetric. In the Symmetric technique, both sender and receiver use the same key for encryption and decryption, but in asymmetric, both use different keys.
To learn the basic concept of cryptography, refer to our CEH v12 Certification Training course https://www.infosectrain.com/courses/certified-ethical-hacker-ceh-training/
#CryptoCharacteristics #EncryptionEssentials #SecurityAlgorithms #DataProtection #Confidentiality #IntegrityVerification #AuthenticationSecurity #CryptographyPrinciples #SecureCommunication #InfoSecBasics #infosectrain #learntorise
Cryptography is a combination of keys (factors) and algorithms (logic) used for data security. It includes different methods and technologies to secure data, such as encryption, decryption, hashing, digital signature, etc. In cryptography, we use two types of encryption techniques: Symmetric and Asymmetric. In the Symmetric technique, both sender and receiver use the same key for encryption and decryption, but in asymmetric, both use different keys.
To learn the basic concept of cryptography, refer to our CEH v12 Certification Training course https://www.infosectrain.com/courses/certified-ethical-hacker-ceh-training/
#CryptoCharacteristics #EncryptionEssentials #SecurityAlgorithms #DataProtection #Confidentiality #IntegrityVerification #AuthenticationSecurity #CryptographyPrinciples #SecureCommunication #InfoSecBasics #infosectrain #learntorise
Characteristics of cryptography
Cryptography is a combination of keys (factors) and algorithms (logic) used for data security. It includes different methods and technologies to secure data, such as encryption, decryption, hashing, digital signature, etc. In cryptography, we use two types of encryption techniques: Symmetric and Asymmetric. In the Symmetric technique, both sender and receiver use the same key for encryption and decryption, but in asymmetric, both use different keys.
To learn the basic concept of cryptography, refer to our CEH v12 Certification Training course 👉 https://www.infosectrain.com/courses/certified-ethical-hacker-ceh-training/
#CryptoCharacteristics #EncryptionEssentials #SecurityAlgorithms #DataProtection #Confidentiality #IntegrityVerification #AuthenticationSecurity #CryptographyPrinciples #SecureCommunication #InfoSecBasics #infosectrain #learntorise
0 Комментарии
0 Поделились
5086 Просмотры
0 предпросмотр