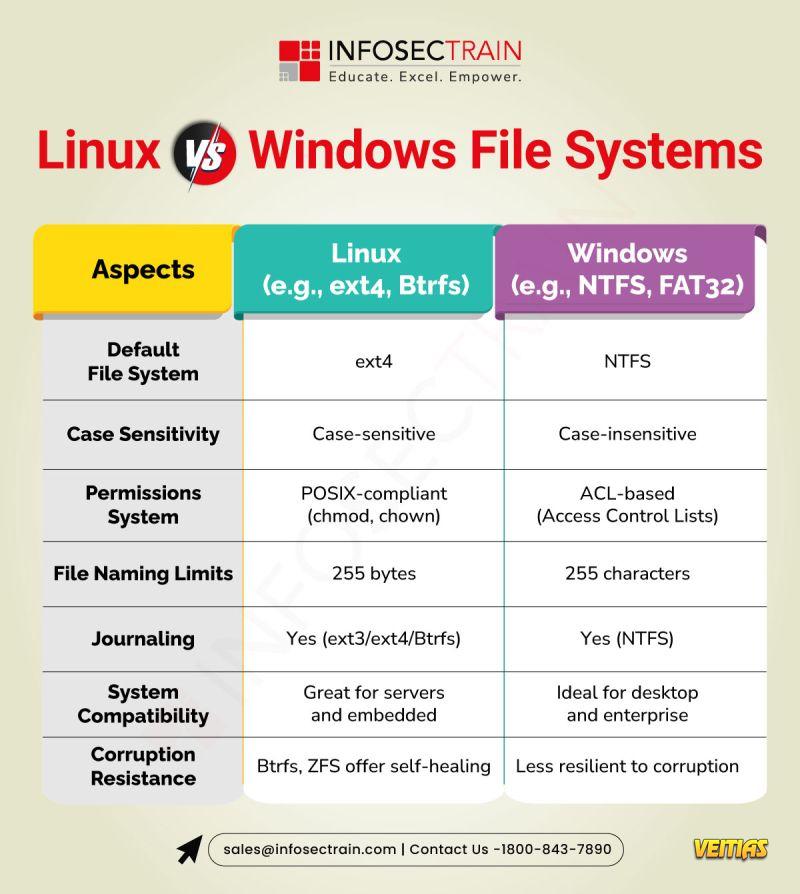
Understanding Linux vs Windows File Systems
Linux uses a unified, tree-structured file system starting at the root (“/”), while Windows manages files across lettered drives like C: and D. In Linux, files are case-sensitive and devices are treated as files. Windows is case-insensitive and classifies devices separately.
Knowing these differences is crucial for sysadmins, developers, and security pros working in multi-OS environments.
Don’t miss out! Enroll here to join InfosecTrain Free Webinar and unlock expert insights. https://www.infosectrain.com/events/
#Linux #Windows #FileSystem #SysAdmin #InfosecTrain
Linux uses a unified, tree-structured file system starting at the root (“/”), while Windows manages files across lettered drives like C: and D. In Linux, files are case-sensitive and devices are treated as files. Windows is case-insensitive and classifies devices separately.
Knowing these differences is crucial for sysadmins, developers, and security pros working in multi-OS environments.
Don’t miss out! Enroll here to join InfosecTrain Free Webinar and unlock expert insights. https://www.infosectrain.com/events/
#Linux #Windows #FileSystem #SysAdmin #InfosecTrain
Understanding Linux vs Windows File Systems
Linux uses a unified, tree-structured file system starting at the root (“/”), while Windows manages files across lettered drives like C: and D. In Linux, files are case-sensitive and devices are treated as files. Windows is case-insensitive and classifies devices separately.
Knowing these differences is crucial for sysadmins, developers, and security pros working in multi-OS environments.
Don’t miss out! Enroll here to join InfosecTrain Free Webinar and unlock expert insights. 👉 https://www.infosectrain.com/events/
#Linux #Windows #FileSystem #SysAdmin #InfosecTrain
0 Reacties
0 aandelen
1167 Views
0 voorbeeld