FREE Masterclass on CompTIA Security+ | Exam Practice Session
Planning to crack the CompTIA Security+ exam? Don’t miss this expert-led, hands-on practice session designed to boost your confidence and exam readiness!
Date: 17 Jan (Saturday)
Time: 8 – 10 PM (IST)
Speaker: Ashish Rawat (Industry Expert)
What You’ll Learn in This Masterclass:
Core Security Concepts Review
Threats, Risks & Attack Vectors
Cryptography Essentials
Identity & Access Management (IAM)
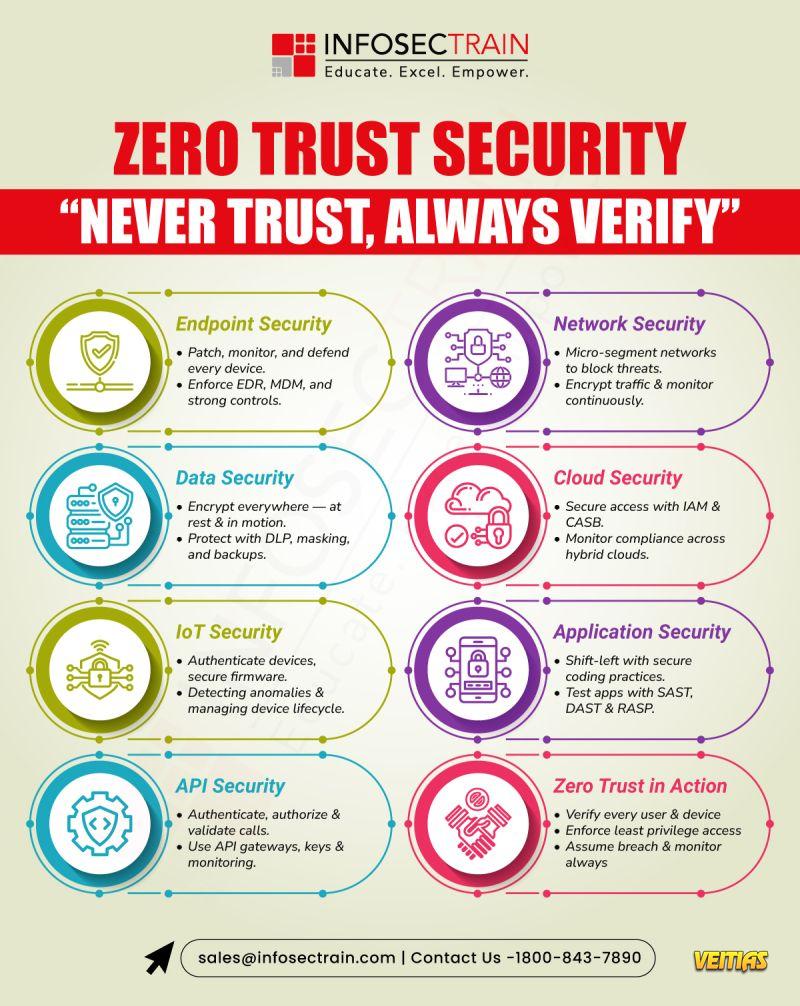
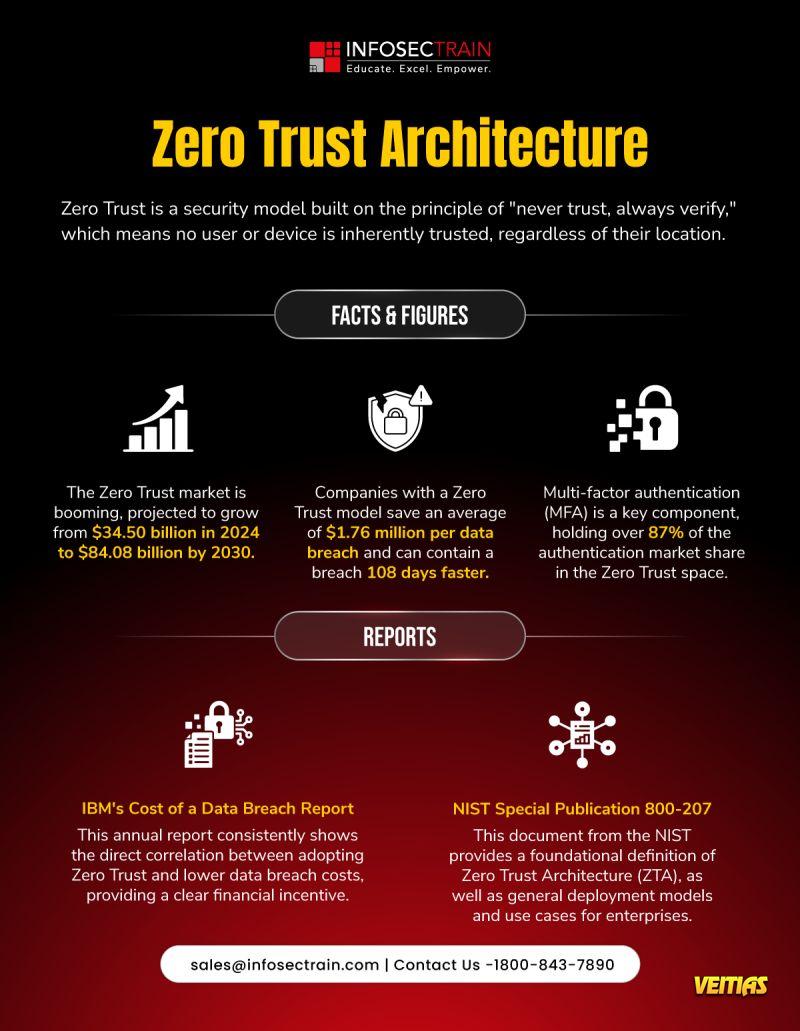
Enterprise Network Security
Cloud Security Fundamentals
Answer Review & Proven Exam Strategies
Why You Should Attend:
Get a CPE Certificate
FREE Career Guidance & Mentorship
Learn directly from industry experts
Improve accuracy with real exam-style questions
Register FREE Now https://www.infosectrain.com/events/comptia-security-exam-practice-session
#CompTIASecurityPlus #CyberSecurity #SecurityPlus #FreeWebinar #CyberCareers #ITSecurity #InfosecTraining #ExamPreparation #CloudSecurity #IAM #NetworkSecurity #CyberLearning
Planning to crack the CompTIA Security+ exam? Don’t miss this expert-led, hands-on practice session designed to boost your confidence and exam readiness!
Date: 17 Jan (Saturday)
Time: 8 – 10 PM (IST)
Speaker: Ashish Rawat (Industry Expert)
What You’ll Learn in This Masterclass:
Core Security Concepts Review
Threats, Risks & Attack Vectors
Cryptography Essentials
Identity & Access Management (IAM)
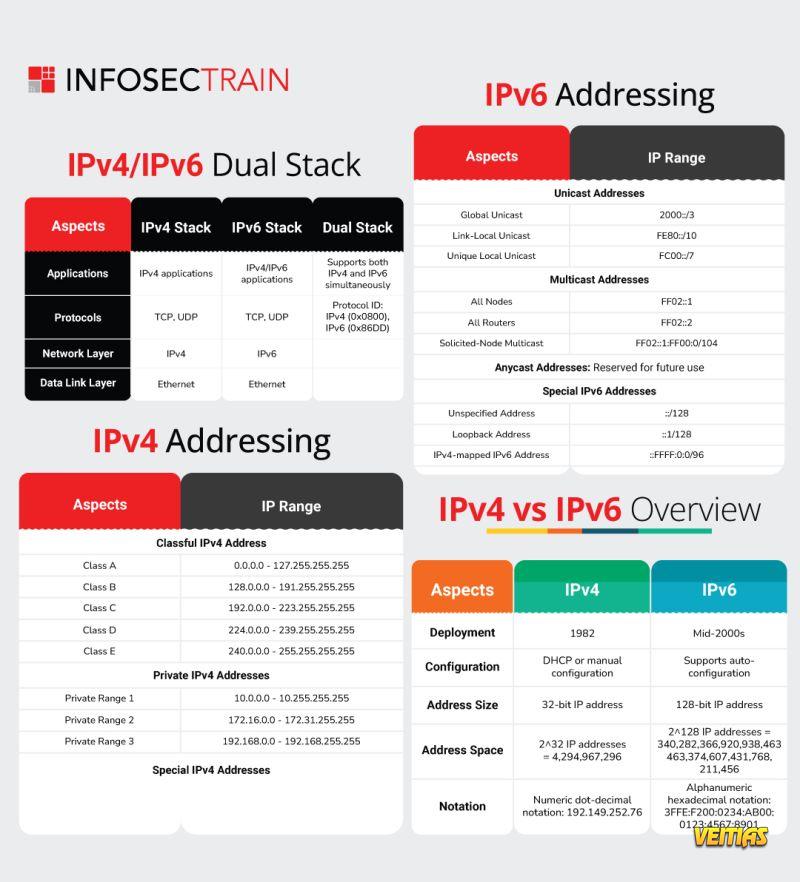
Enterprise Network Security
Cloud Security Fundamentals
Answer Review & Proven Exam Strategies
Why You Should Attend:
Get a CPE Certificate
FREE Career Guidance & Mentorship
Learn directly from industry experts
Improve accuracy with real exam-style questions
Register FREE Now https://www.infosectrain.com/events/comptia-security-exam-practice-session
#CompTIASecurityPlus #CyberSecurity #SecurityPlus #FreeWebinar #CyberCareers #ITSecurity #InfosecTraining #ExamPreparation #CloudSecurity #IAM #NetworkSecurity #CyberLearning
FREE Masterclass on CompTIA Security+ | Exam Practice Session
Planning to crack the CompTIA Security+ exam? Don’t miss this expert-led, hands-on practice session designed to boost your confidence and exam readiness!
📅 Date: 17 Jan (Saturday)
⏰ Time: 8 – 10 PM (IST)
🎤 Speaker: Ashish Rawat (Industry Expert)
🎯 What You’ll Learn in This Masterclass:
✅ Core Security Concepts Review
✅ Threats, Risks & Attack Vectors
✅ Cryptography Essentials
✅ Identity & Access Management (IAM)
✅ Enterprise Network Security
✅ Cloud Security Fundamentals
✅ Answer Review & Proven Exam Strategies
🚀 Why You Should Attend:
🎓 Get a CPE Certificate
🧭 FREE Career Guidance & Mentorship
👨🏫 Learn directly from industry experts
📘 Improve accuracy with real exam-style questions
👉 Register FREE Now🔗 https://www.infosectrain.com/events/comptia-security-exam-practice-session
#CompTIASecurityPlus #CyberSecurity #SecurityPlus #FreeWebinar #CyberCareers #ITSecurity #InfosecTraining #ExamPreparation #CloudSecurity #IAM #NetworkSecurity #CyberLearning
0 Комментарии
0 Поделились
1306 Просмотры
0 предпросмотр