Недавние обновления
Страна
Страна
Saint Kitts and Nevis
Palau
Pakistan
Oman
Norway
Northern Mariana Islands
Norfolk Island
Niue
Nigeria
Niger
Nicaragua
New Zealand
New Caledonia
Netherlands Antilles
Palestine
Panama
Rwanda
Russian Federation
Romania
Reunion
Qatar
Puerto Rico
Portugal
Poland
Pitcairn
Philippines
Peru
Paraguay
Papua New Guinea
Netherlands
Nepal
Nauru
Marshall Islands
Malta
Mali
Maldives
Malaysia
Malawi
Madagascar
Macedonia
Macau
Luxembourg
Lithuania
Liechtenstein
Libyan Arab Jamahiriya
Martinique
Mauritania
Namibia
Myanmar
Mozambique
Morocco
Montserrat
Montenegro
Mongolia
Monaco
Moldova, Republic of
Micronesia, Federated States of
Mexico
Mayotte
Mauritius
Liberia
Zimbabwe
United Kingdom
United Arab Emirates
Ukraine
Uganda
Tuvalu
Turks and Caicos Islands
Turkmenistan
Turkey
Tunisia
Trinidad and Tobago
Tonga
Tokelau
Togo
United States
United States minor outlying islands
Zambia
Zaire
Yemen
Western Sahara
Wallis and Futuna Islands
Virgin Islands (U.S.)
Virgin Islands (British)
Vietnam
Venezuela
Vatican City State
Vanuatu
Uzbekistan
Uruguay
Thailand
Tanzania, United Republic of
Tajikistan
Solomon Islands
Slovenia
Slovakia
Singapore
Sierra Leone
Seychelles
Serbia
Senegal
Saudi Arabia
Sao Tome and Principe
San Marino
Samoa
Saint Vincent and the Grenadines
Somalia
South Africa
Taiwan
Syrian Arab Republic
Switzerland
Sweden
Swaziland
Svalbard and Jan Mayen Islands
Suriname
Sudan
St. Pierre and Miquelon
St. Helena
Sri Lanka
Spain
South Georgia South Sandwich Islands
Saint Lucia
Lesotho
Ecuador
Christmas Island
China
Chile
Chad
Central African Republic
Cayman Islands
Cape Verde
Canada
Cameroon
Cambodia
Burundi
Burkina Faso
Bulgaria
Cocos (Keeling) Islands
Colombia
East Timor
Dominican Republic
Dominica
Djibouti
Denmark
Czech Republic
Cyprus
Cuba
Croatia (Hrvatska)
Costa Rica
Cook Islands
Congo
Comoros
Brunei Darussalam
British Indian Ocean Territory
Brazil
Austria
Australia
Aruba
Armenia
Argentina
Antigua and Barbuda
Antarctica
Anguilla
Angola
Andorra
American Samoa
Algeria
Albania
Azerbaijan
Bahamas
Bouvet Island
Botswana
Bosnia and Herzegovina
Bolivia
Bhutan
Bermuda
Benin
Belize
Belgium
Belarus
Barbados
Bangladesh
Bahrain
Afghanistan
Lebanon
Italy
Israel
Ireland
Iraq
Iran (Islamic Republic of)
Indonesia
Isle of Man
India
Iceland
Hungary
Hong Kong
Honduras
Heard and Mc Donald Islands
Ivory Coast
Jersey
Latvia
Lao People's Democratic Republic
Kyrgyzstan
Kuwait
Kosovo
Korea, Republic of
Korea, Democratic People's Republic of
Kiribati
Kenya
Kazakhstan
Jordan
Japan
Jamaica
Haiti
Guyana
Guinea-Bissau
French Polynesia
French Guiana
France, Metropolitan
France
Finland
Fiji
Faroe Islands
Falkland Islands (Malvinas)
Ethiopia
Estonia
Eritrea
Equatorial Guinea
El Salvador
French Southern Territories
Gabon
Guinea
Guatemala
Guam
Guadeloupe
Grenada
Greenland
Greece
Guernsey
Gibraltar
Ghana
Germany
Georgia
Gambia
Egypt
- 𝐃𝐚𝐭𝐚 𝐏𝐫𝐢𝐯𝐚𝐜𝐲 𝐚𝐧𝐝 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲: 𝐓𝐨𝐝𝐚𝐲'𝐬 𝐁𝐮𝐬𝐢𝐧𝐞𝐬𝐬 𝐃𝐞𝐦𝐚𝐧𝐝𝐬!
In a data-driven world, privacy and security are not optional, they are mandatory. Organizations are under immense pressure to get ahead of the curve or face the risk of huge fines, or worse, data breaches, as a result of an increasing number of cyber threats and stringent regulations such as 𝐆𝐃𝐏𝐑 𝐚𝐧𝐝 𝐂𝐂𝐏𝐀.
Whether you need to prepare for an interview or simply want to enhance your data protection skillset, this resource has everything you need to master the tension between data privacy and security.
𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/data-privacy-and-security-interview-questions-and-answers/
Advance your career with 𝐈𝐧𝐟𝐨𝐬𝐞𝐜 𝐓𝐫𝐚𝐢𝐧 𝐜𝐞𝐫𝐭𝐢𝐟𝐢𝐜𝐚𝐭𝐢𝐨𝐧 𝐜𝐨𝐮𝐫𝐬𝐞𝐬 and established yourself as a dependable specialist in data compliance and protection.
#DataPrivacy #CyberSecurity #InfoSecTrain #DataProtection #GDPR #CCPA #PrivacyByDesign #CyberAwareness #SecurityCompliance🔒 𝐃𝐚𝐭𝐚 𝐏𝐫𝐢𝐯𝐚𝐜𝐲 𝐚𝐧𝐝 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲: 𝐓𝐨𝐝𝐚𝐲'𝐬 𝐁𝐮𝐬𝐢𝐧𝐞𝐬𝐬 𝐃𝐞𝐦𝐚𝐧𝐝𝐬! In a data-driven world, privacy and security are not optional, they are mandatory. Organizations are under immense pressure to get ahead of the curve or face the risk of huge fines, or worse, data breaches, as a result of an increasing number of cyber threats and stringent regulations such as 𝐆𝐃𝐏𝐑 𝐚𝐧𝐝 𝐂𝐂𝐏𝐀. Whether you need to prepare for an interview or simply want to enhance your data protection skillset, this resource has everything you need to master the tension between data privacy and security. 👉𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/data-privacy-and-security-interview-questions-and-answers/ 👉 Advance your career with 𝐈𝐧𝐟𝐨𝐬𝐞𝐜 𝐓𝐫𝐚𝐢𝐧 𝐜𝐞𝐫𝐭𝐢𝐟𝐢𝐜𝐚𝐭𝐢𝐨𝐧 𝐜𝐨𝐮𝐫𝐬𝐞𝐬 and established yourself as a dependable specialist in data compliance and protection. #DataPrivacy #CyberSecurity #InfoSecTrain #DataProtection #GDPR #CCPA #PrivacyByDesign #CyberAwareness #SecurityComplianceWWW.INFOSECTRAIN.COMData Privacy and Security Interview Questions and AnswersData Privacy and Security Interview Questions and Answers to help you crack cybersecurity, GDPR, and ISO 27001 job roles with expert guidance.0 Комментарии 0 Поделились 1108 Просмотры 0 предпросмотрВойдите, чтобы отмечать, делиться и комментировать! - Crack Your SOC Interview | Top Questions & Expert Tips
This masterclass is your ultimate guide to acing SOC interviews with confidence. We cover the most frequently asked SOC interview questions, provide expert tips & tricks, and share real-world strategies to help you stand out.
What you’ll learn in this session:
Introduction to SOC
Access & Authentication Scenarios
Phishing Scenarios
Network Scenarios
Rapid-Fire Mini Scenarios
How to Tackle Scenario Questions
Watch Here: https://youtu.be/2KlGzKZQA2I?si=qDbfzUBQOSuhyVdK
#SOCInterview #SOCAnalyst #CybersecurityJobs #SOCInterviewPrep #SOCInterviewQuestions #SOCInterviewTips #CybersecurityCareers #SIEM #ThreatIntelligence #IncidentResponseCrack Your SOC Interview | Top Questions & Expert Tips This masterclass is your ultimate guide to acing SOC interviews with confidence. We cover the most frequently asked SOC interview questions, provide expert tips & tricks, and share real-world strategies to help you stand out. 🔥 What you’ll learn in this session: ✅ Introduction to SOC ✅ Access & Authentication Scenarios ✅ Phishing Scenarios ✅ Network Scenarios ✅ Rapid-Fire Mini Scenarios ✅ How to Tackle Scenario Questions Watch Here: https://youtu.be/2KlGzKZQA2I?si=qDbfzUBQOSuhyVdK #SOCInterview #SOCAnalyst #CybersecurityJobs #SOCInterviewPrep #SOCInterviewQuestions #SOCInterviewTips #CybersecurityCareers #SIEM #ThreatIntelligence #IncidentResponse 0 Комментарии 0 Поделились 1057 Просмотры 0 предпросмотр
0 Комментарии 0 Поделились 1057 Просмотры 0 предпросмотр - Supply Chain Security & Automation in 2025
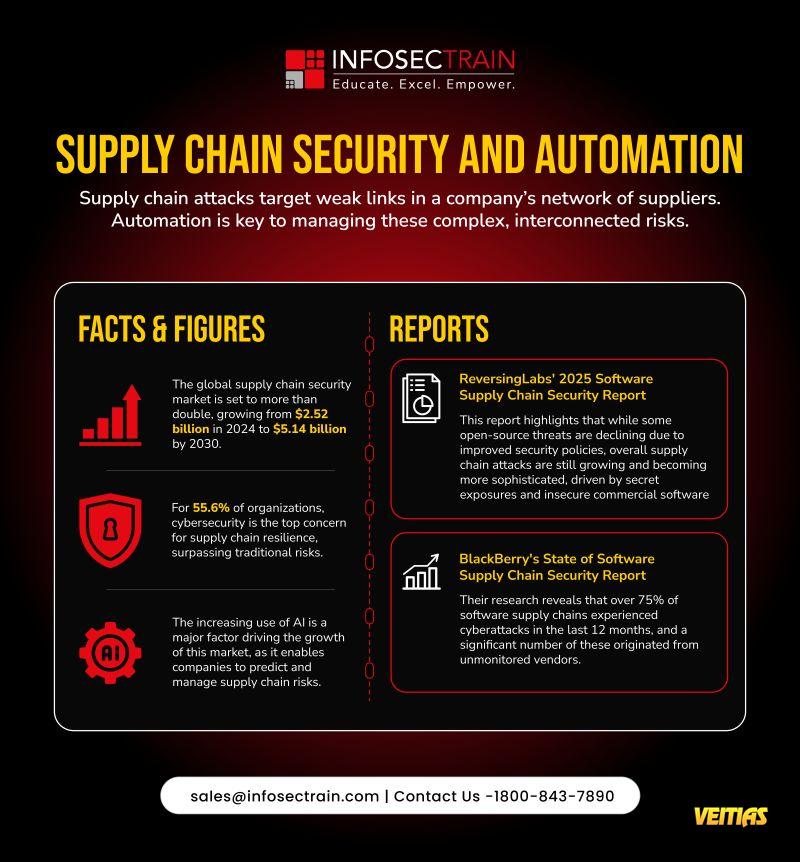
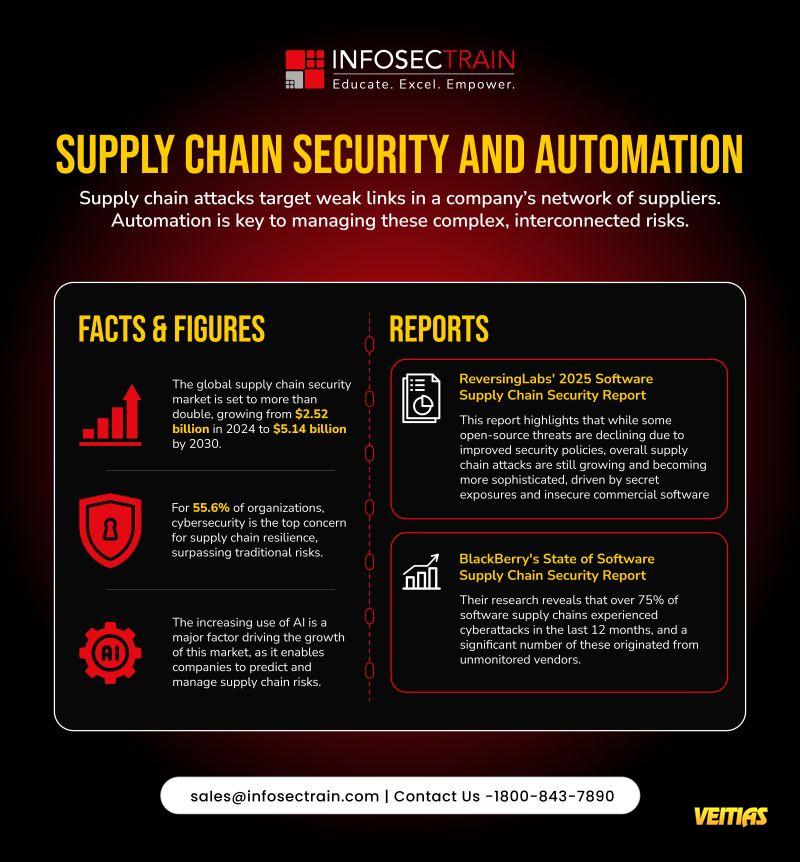
As global supply chains become increasingly interconnected, cyber attackers are exploiting the weakest links — often through unsecured or unmonitored vendors.
Automation and AI are no longer optional — they’re essential to managing complex, evolving risks across supplier networks.
Key Insights:
• The supply chain security market is projected to grow from $2.52B (2024) to $5.14B (2030).
• 55.6% of organizations now rank cybersecurity as their top concern for supply chain resilience.
• AI adoption is transforming risk prediction and response.
Recent Reports:
Reversing Labs 2025 Report: Supply chain attacks are growing more sophisticated despite improved open-source security.
BlackBerry Report: Over 75% of software supply chains faced cyberattacks in the past year — many from unmonitored vendors.
This #CybersecurityAwarenessMonth2025, remember — a chain is only as strong as its most secure link.
Check out: https://www.infosectrain.com/events/
#CyberSecurity #SupplyChainSecurity #Automation #AI #InfoSecTrain #DataProtection #ThreatIntelligence #RiskManagement #CyberDefense🔒 Supply Chain Security & Automation in 2025 As global supply chains become increasingly interconnected, cyber attackers are exploiting the weakest links — often through unsecured or unmonitored vendors. 💡 Automation and AI are no longer optional — they’re essential to managing complex, evolving risks across supplier networks. 📊 Key Insights: • The supply chain security market is projected to grow from $2.52B (2024) to $5.14B (2030). • 55.6% of organizations now rank cybersecurity as their top concern for supply chain resilience. • AI adoption is transforming risk prediction and response. 📘 Recent Reports: Reversing Labs 2025 Report: Supply chain attacks are growing more sophisticated despite improved open-source security. BlackBerry Report: Over 75% of software supply chains faced cyberattacks in the past year — many from unmonitored vendors. 🔗 This #CybersecurityAwarenessMonth2025, remember — a chain is only as strong as its most secure link. Check out: https://www.infosectrain.com/events/ #CyberSecurity #SupplyChainSecurity #Automation #AI #InfoSecTrain #DataProtection #ThreatIntelligence #RiskManagement #CyberDefense0 Комментарии 0 Поделились 1217 Просмотры 0 предпросмотр - IPv4 vs. IPv6: The Evolution of Internet Addressing!
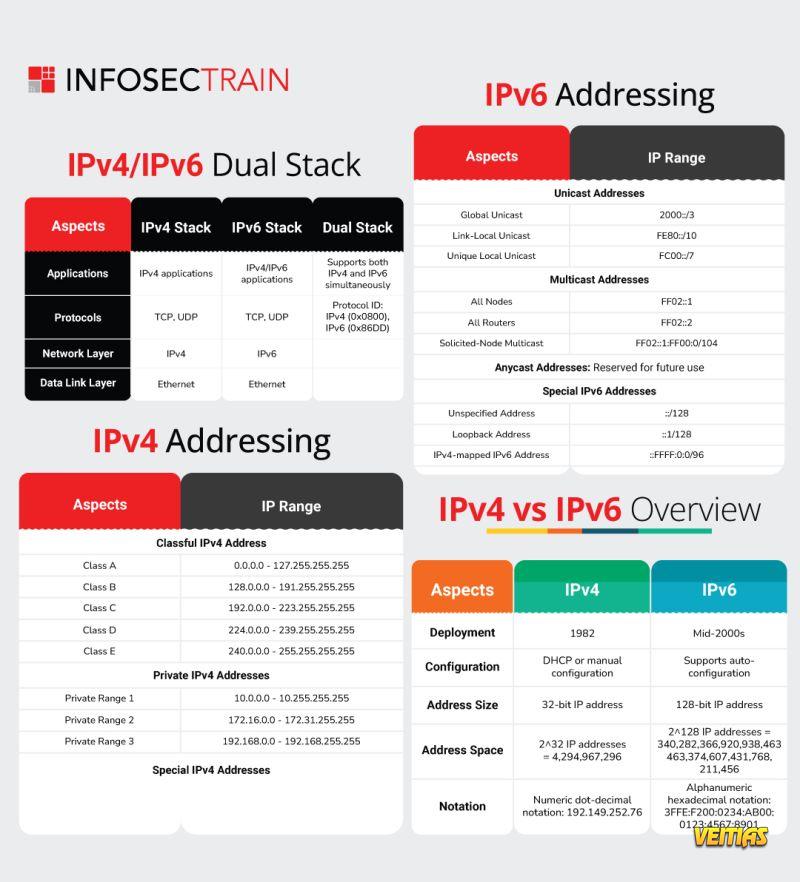
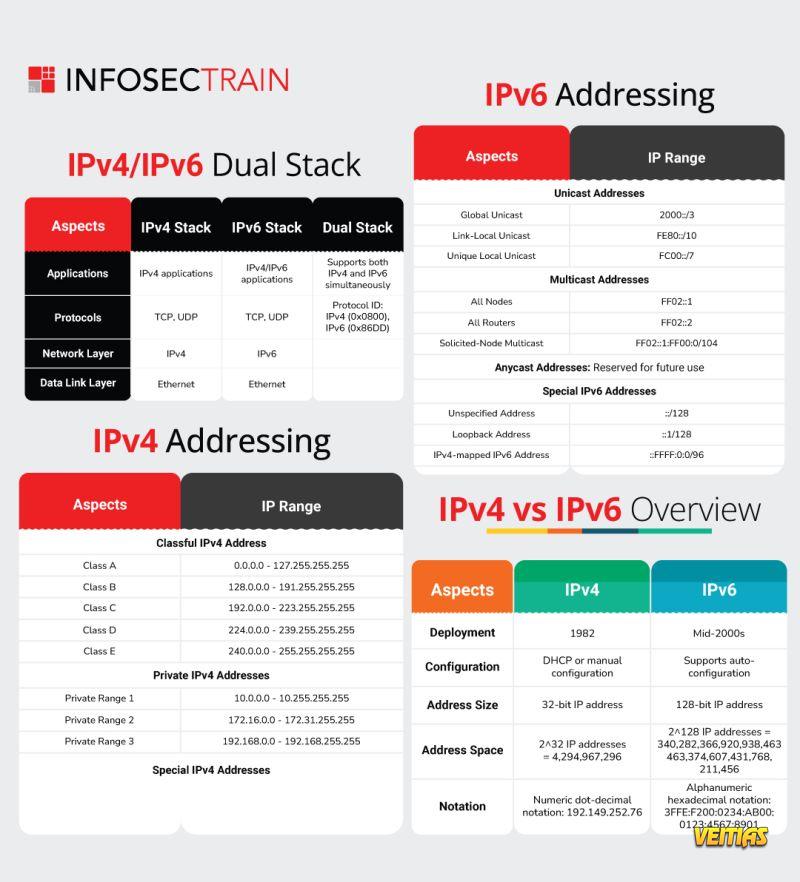
Key Highlights:
IPv4 uses 32-bit addresses (≈ 4.3 billion)
IPv6 uses 128-bit addresses (≈ 340 undecillion!)
IPv6 offers better efficiency, scalability & performance
Dual Stack systems support both IPv4 and IPv6 together
Learn more about IPv4, IPv6, and Dual Stack addressing with InfosecTrain’s expert-led network security training!
#IPv6 #Networking #CyberSecurity #IPv4 #InfoSecTrain #NetworkSecurity #ITTraining #TechLearning #CyberAwarenessIPv4 vs. IPv6: The Evolution of Internet Addressing! Key Highlights: ✅ IPv4 uses 32-bit addresses (≈ 4.3 billion) ✅ IPv6 uses 128-bit addresses (≈ 340 undecillion!) ✅ IPv6 offers better efficiency, scalability & performance ✅ Dual Stack systems support both IPv4 and IPv6 together 📘 Learn more about IPv4, IPv6, and Dual Stack addressing with InfosecTrain’s expert-led network security training! #IPv6 #Networking #CyberSecurity #IPv4 #InfoSecTrain #NetworkSecurity #ITTraining #TechLearning #CyberAwareness0 Комментарии 0 Поделились 1118 Просмотры 0 предпросмотр - Supply Chain Security & Automation in 2025
As global supply chains grow more interconnected, cyber threats are targeting the weakest links, often through unmonitored or unsecured vendors.
Visit Our Site - https://www.infosectrain.com/
Build resilience. Automate defenses. Stay vigilant.
#SupplyChainSecurity #CyberResilience #Automation #AlinSecurity #ThreatIntelligence #CyberAwareness #DigitalTrust #VendorRiskManagement #infosectrain #learntoriseSupply Chain Security & Automation in 2025 As global supply chains grow more interconnected, cyber threats are targeting the weakest links, often through unmonitored or unsecured vendors. Visit Our Site - https://www.infosectrain.com/ Build resilience. Automate defenses. Stay vigilant. #SupplyChainSecurity #CyberResilience #Automation #AlinSecurity #ThreatIntelligence #CyberAwareness #DigitalTrust #VendorRiskManagement #infosectrain #learntorise0 Комментарии 0 Поделились 1198 Просмотры 0 предпросмотр - Master AI Audit with ISACA’s AAIA | Complete Certification Guide
In this session, we’ll cover:
AAIA Certification Overview
Exam Overview
Exam Prep plan
Certification Benefits
Watch here: https://youtu.be/tZu14fpiA70?si=4Qb5MRt2332j8lX2
#ISACAAAIA #AIAudit #ISACACertifications #AIAssurance #ResponsibleAI #AIGovernance #AISecurity #AIAuditCertification #CybersecurityCareers #AIComplianceMaster AI Audit with ISACA’s AAIA | Complete Certification Guide 🔥 In this session, we’ll cover: 👉 AAIA Certification Overview 👉Exam Overview 👉Exam Prep plan 👉Certification Benefits Watch here: https://youtu.be/tZu14fpiA70?si=4Qb5MRt2332j8lX2 #ISACAAAIA #AIAudit #ISACACertifications #AIAssurance #ResponsibleAI #AIGovernance #AISecurity #AIAuditCertification #CybersecurityCareers #AICompliance 0 Комментарии 0 Поделились 1819 Просмотры 0 предпросмотр
0 Комментарии 0 Поделились 1819 Просмотры 0 предпросмотр - 𝐂𝐨𝐥𝐥𝐞𝐜𝐭 𝐞𝐦𝐚𝐢𝐥𝐬 𝐭𝐡𝐞 𝐬𝐚𝐟𝐞 𝐚𝐧𝐝 𝐢𝐧𝐭𝐞𝐥𝐥𝐢𝐠𝐞𝐧𝐭 𝐰𝐚𝐲!
Have you ever been curious about how the guys in cyber security gather and validate lists of emails without running afoul of the ethics police?
Experience the potential of 𝐒𝐧𝐨𝐯.𝐢𝐨, a popular ethical hacker tool and OSINT solution to easily gather, verify the accuracy of, and organize email information in bulk, safely and securely.
Here’s what you need to know:
Get emails from domains and LinkedIn – safe and legit
Use bulk verification to keep bounces to a minimum and increase deliverability
Connect to your existing workflows with API & tools
Why verified lists are critical to phishing simulations & intel gathering
𝐕𝐞𝐫𝐢𝐟𝐢𝐞𝐝 𝐝𝐚𝐭𝐚 = 𝐁𝐞𝐭𝐭𝐞𝐫 𝐬𝐢𝐦𝐮𝐥𝐚𝐭𝐢𝐨𝐧𝐬. 𝐒𝐭𝐫𝐨𝐧𝐠𝐞𝐫 𝐝𝐞𝐟𝐞𝐧𝐬𝐞𝐬.
Read more: https://www.infosectrain.com/blog/how-to-collect-and-verify-emails-at-scale-using-snov-io/
Be compliant, be accurate, be efficient with every click!
#CyberSecurity #OSINT #EmailSecurity #EthicalHacking #InfoSecTrain #PhishingSimulation #ThreatIntelligence #DataProtection𝐂𝐨𝐥𝐥𝐞𝐜𝐭 𝐞𝐦𝐚𝐢𝐥𝐬 𝐭𝐡𝐞 𝐬𝐚𝐟𝐞 𝐚𝐧𝐝 𝐢𝐧𝐭𝐞𝐥𝐥𝐢𝐠𝐞𝐧𝐭 𝐰𝐚𝐲! Have you ever been curious about how the guys in cyber security gather and validate lists of emails without running afoul of the ethics police? Experience the potential of 𝐒𝐧𝐨𝐯.𝐢𝐨, a popular ethical hacker tool and OSINT solution to easily gather, verify the accuracy of, and organize email information in bulk, safely and securely. Here’s what you need to know: ✅ Get emails from domains and LinkedIn – safe and legit ✅ Use bulk verification to keep bounces to a minimum and increase deliverability ✅ Connect to your existing workflows with API & tools ➡️ Why verified lists are critical to phishing simulations & intel gathering ➡️𝐕𝐞𝐫𝐢𝐟𝐢𝐞𝐝 𝐝𝐚𝐭𝐚 = 𝐁𝐞𝐭𝐭𝐞𝐫 𝐬𝐢𝐦𝐮𝐥𝐚𝐭𝐢𝐨𝐧𝐬. 𝐒𝐭𝐫𝐨𝐧𝐠𝐞𝐫 𝐝𝐞𝐟𝐞𝐧𝐬𝐞𝐬. 👉 Read more: https://www.infosectrain.com/blog/how-to-collect-and-verify-emails-at-scale-using-snov-io/ ✅ Be compliant, be accurate, be efficient with every click! #CyberSecurity #OSINT #EmailSecurity #EthicalHacking #InfoSecTrain #PhishingSimulation #ThreatIntelligence #DataProtectionWWW.INFOSECTRAIN.COMHow to Collect and Verify Emails at Scale Using Snov.io?Learn how to collect and verify emails at scale using Snov.io. Discover step-by-step strategies, automation tips, and best practices to improve outreach and boost email deliverability.0 Комментарии 0 Поделились 1943 Просмотры 0 предпросмотр - IPv4 vs. IPv6 represents the evolution of internet addressing. IPv4 (Internet Protocol version 4) uses a 32-bit address system, allowing around 4.3 billion unique addresses, which are now nearly exhausted due to the rapid growth of internet-connected devices. IPv6 (Internet Protocol version 6), on the other hand, uses a 128-bit address system, providing an almost limitless number of unique IP addresses. Besides expanded address space, IPv6 offers improved security, faster routing, and more efficient network management, making it the future standard for global internet communication.IPv4 vs. IPv6 represents the evolution of internet addressing. IPv4 (Internet Protocol version 4) uses a 32-bit address system, allowing around 4.3 billion unique addresses, which are now nearly exhausted due to the rapid growth of internet-connected devices. IPv6 (Internet Protocol version 6), on the other hand, uses a 128-bit address system, providing an almost limitless number of unique IP addresses. Besides expanded address space, IPv6 offers improved security, faster routing, and more efficient network management, making it the future standard for global internet communication.0 Комментарии 0 Поделились 2289 Просмотры 0 предпросмотр
- 0 Комментарии 0 Поделились 2852 Просмотры 0 предпросмотр
- Free Webinar Alert!
SOC Masterclass: Skills Every Analyst Needs in 2026
Get ready to sharpen your cybersecurity edge and step inside the world of Security Operations Centers (SOC)!
Date: 05–06 Nov (Wed–Thu)
Time: 8 PM – 10 PM (IST)
Format: Free Masterclass + Live Q&A
Speaker: Sanyam
Agenda Highlights
DAY 1: Inside the SOC
Information Security & SOC Fundamentals
Log Analysis: “Find the Anomaly”
Threat Intelligence Essentials
SOC Workflow & Incident Lifecycle
DAY 2: The Hunt, The Breach & The Response
Threat Hunting Fundamentals
Network Traffic Analysis
Phishing Investigation
Incident Response Lifecycle
Career Roadmap for SOC Analysts
Why You Should Attend
Earn a CPE Certificate
Get FREE Career Guidance & Mentorship
Learn from Industry Experts
Stay Ahead with 2026-Ready SOC Skills
🎟 Seats are limited—register FREE now!
https://www.infosectrain.com/events/soc-masterclass-skills-every-analyst-needs-in-2026/
#CyberSecurity #SOCAnalyst #SOCTraining #InfoSecTrain #CyberAwareness #ThreatHunting #FreeWebinar #CyberSkills #LearnCyberSecurity #SecurityOperations #CyberJobs #BlueTeam🚨 Free Webinar Alert! 🚨 🎯 SOC Masterclass: Skills Every Analyst Needs in 2026 Get ready to sharpen your cybersecurity edge and step inside the world of Security Operations Centers (SOC)! 📅 Date: 05–06 Nov (Wed–Thu) 🕗 Time: 8 PM – 10 PM (IST) 🎓 Format: Free Masterclass + Live Q&A 🎤 Speaker: Sanyam 💡 Agenda Highlights DAY 1: Inside the SOC 🔹 Information Security & SOC Fundamentals 🔹 Log Analysis: “Find the Anomaly” 🔹 Threat Intelligence Essentials 🔹 SOC Workflow & Incident Lifecycle DAY 2: The Hunt, The Breach & The Response 🔹 Threat Hunting Fundamentals 🔹 Network Traffic Analysis 🔹 Phishing Investigation 🔹 Incident Response Lifecycle 🔹 Career Roadmap for SOC Analysts 🚀 Why You Should Attend ✅ Earn a CPE Certificate ✅ Get FREE Career Guidance & Mentorship ✅ Learn from Industry Experts ✅ Stay Ahead with 2026-Ready SOC Skills 🎟 Seats are limited—register FREE now! 👉 https://www.infosectrain.com/events/soc-masterclass-skills-every-analyst-needs-in-2026/ #CyberSecurity #SOCAnalyst #SOCTraining #InfoSecTrain #CyberAwareness #ThreatHunting #FreeWebinar #CyberSkills #LearnCyberSecurity #SecurityOperations #CyberJobs #BlueTeamWWW.INFOSECTRAIN.COMSOC Masterclass: Skills Every Analyst Needs in 2026Educate. Excel. Empower.0 Комментарии 0 Поделились 4421 Просмотры 0 предпросмотр
Больше