Free Webinar Alert!
SOC Masterclass: Skills Every Analyst Needs in 2026
Get ready to sharpen your cybersecurity edge and step inside the world of Security Operations Centers (SOC)!
Date: 05–06 Nov (Wed–Thu)
Time: 8 PM – 10 PM (IST)
Format: Free Masterclass + Live Q&A
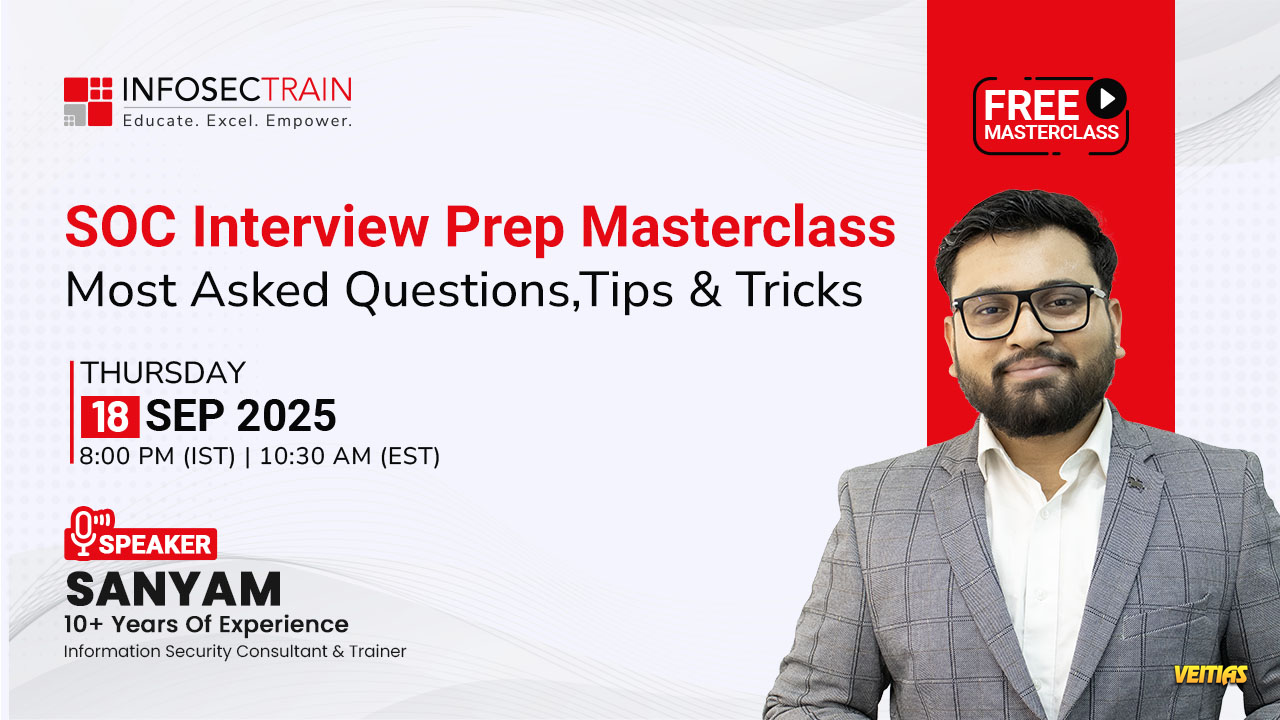
Speaker: Sanyam
Agenda Highlights
DAY 1: Inside the SOC
Information Security & SOC Fundamentals
Log Analysis: “Find the Anomaly”
Threat Intelligence Essentials
SOC Workflow & Incident Lifecycle
DAY 2: The Hunt, The Breach & The Response
Threat Hunting Fundamentals
Network Traffic Analysis
Phishing Investigation
Incident Response Lifecycle
Career Roadmap for SOC Analysts
Why You Should Attend
Earn a CPE Certificate
Get FREE Career Guidance & Mentorship
Learn from Industry Experts
Stay Ahead with 2026-Ready SOC Skills
🎟 Seats are limited—register FREE now!
https://www.infosectrain.com/events/soc-masterclass-skills-every-analyst-needs-in-2026/
#CyberSecurity #SOCAnalyst #SOCTraining #InfoSecTrain #CyberAwareness #ThreatHunting #FreeWebinar #CyberSkills #LearnCyberSecurity #SecurityOperations #CyberJobs #BlueTeam
SOC Masterclass: Skills Every Analyst Needs in 2026
Get ready to sharpen your cybersecurity edge and step inside the world of Security Operations Centers (SOC)!
Date: 05–06 Nov (Wed–Thu)
Time: 8 PM – 10 PM (IST)
Format: Free Masterclass + Live Q&A
Speaker: Sanyam
Agenda Highlights
DAY 1: Inside the SOC
Information Security & SOC Fundamentals
Log Analysis: “Find the Anomaly”
Threat Intelligence Essentials
SOC Workflow & Incident Lifecycle
DAY 2: The Hunt, The Breach & The Response
Threat Hunting Fundamentals
Network Traffic Analysis
Phishing Investigation
Incident Response Lifecycle
Career Roadmap for SOC Analysts
Why You Should Attend
Earn a CPE Certificate
Get FREE Career Guidance & Mentorship
Learn from Industry Experts
Stay Ahead with 2026-Ready SOC Skills
🎟 Seats are limited—register FREE now!
https://www.infosectrain.com/events/soc-masterclass-skills-every-analyst-needs-in-2026/
#CyberSecurity #SOCAnalyst #SOCTraining #InfoSecTrain #CyberAwareness #ThreatHunting #FreeWebinar #CyberSkills #LearnCyberSecurity #SecurityOperations #CyberJobs #BlueTeam
🚨 Free Webinar Alert! 🚨
🎯 SOC Masterclass: Skills Every Analyst Needs in 2026
Get ready to sharpen your cybersecurity edge and step inside the world of Security Operations Centers (SOC)!
📅 Date: 05–06 Nov (Wed–Thu)
🕗 Time: 8 PM – 10 PM (IST)
🎓 Format: Free Masterclass + Live Q&A
🎤 Speaker: Sanyam
💡 Agenda Highlights
DAY 1: Inside the SOC
🔹 Information Security & SOC Fundamentals
🔹 Log Analysis: “Find the Anomaly”
🔹 Threat Intelligence Essentials
🔹 SOC Workflow & Incident Lifecycle
DAY 2: The Hunt, The Breach & The Response
🔹 Threat Hunting Fundamentals
🔹 Network Traffic Analysis
🔹 Phishing Investigation
🔹 Incident Response Lifecycle
🔹 Career Roadmap for SOC Analysts
🚀 Why You Should Attend
✅ Earn a CPE Certificate
✅ Get FREE Career Guidance & Mentorship
✅ Learn from Industry Experts
✅ Stay Ahead with 2026-Ready SOC Skills
🎟 Seats are limited—register FREE now!
👉 https://www.infosectrain.com/events/soc-masterclass-skills-every-analyst-needs-in-2026/
#CyberSecurity #SOCAnalyst #SOCTraining #InfoSecTrain #CyberAwareness #ThreatHunting #FreeWebinar #CyberSkills #LearnCyberSecurity #SecurityOperations #CyberJobs #BlueTeam
0 Comments
0 Shares
6103 Views
0 Reviews