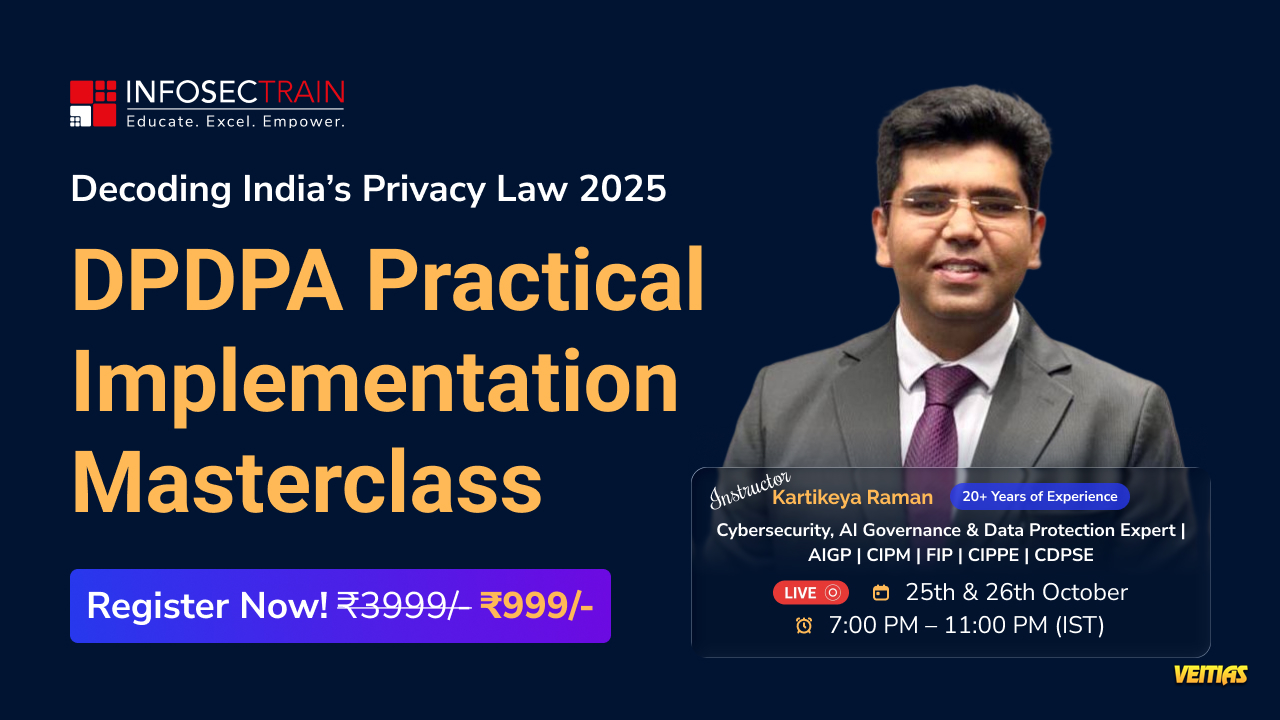
FREE Masterclass Alert!
From Law to Practice: Implementing the 2025 DPDPA Rules in Your Business
India’s Data Protection landscape is entering a new era is your organization ready to comply? Join our live masterclass and learn how to transform the 2025 DPDPA requirements into real, actionable business practices that strengthen compliance and build customer trust.
Date: 13 Dec (Saturday)
Time: 11 AM – 1 PM (IST)
🎙 Speaker: Vasanth Kumar
Free Registration: https://www.infosectrain.com/events/from-law-to-practice-implementing-the-2025-dpdpa-rules-in-your-business/
What You’ll Learn (Agenda Highlights)
✔ Understanding DPDPA Scope & Key Roles
✔ Lawful Bases & Transparent Notices
✔ End-to-End Consent Lifecycle Management
✔ Security Controls & Data Breach Handling
✔ Data Subject Rights, Retention & Deletion
✔ Cross-Border Data Transfers Rules
✔ Responsibilities of Significant Data Fiduciaries (SDFs)
✔ Live Industry Q&A — Practical Insights!
Why You Should Attend
Earn a CPE Certificate
Get Free Career Mentorship from industry experts
Learn proven implementation strategies — beyond the legal text
Stay ahead of regulatory changes before they become mandatory
#DPDPA #DataProtectionIndia #PrivacyCompliance #DataGovernance #CyberLaw #InfoSecTrain #FreeWebinar #ComplianceProfessionals #DataSecurity #DPO #DigitalPrivacy #RegTech #CareerGrowth #CPECredits
From Law to Practice: Implementing the 2025 DPDPA Rules in Your Business
India’s Data Protection landscape is entering a new era is your organization ready to comply? Join our live masterclass and learn how to transform the 2025 DPDPA requirements into real, actionable business practices that strengthen compliance and build customer trust.
Date: 13 Dec (Saturday)
Time: 11 AM – 1 PM (IST)
🎙 Speaker: Vasanth Kumar
Free Registration: https://www.infosectrain.com/events/from-law-to-practice-implementing-the-2025-dpdpa-rules-in-your-business/
What You’ll Learn (Agenda Highlights)
✔ Understanding DPDPA Scope & Key Roles
✔ Lawful Bases & Transparent Notices
✔ End-to-End Consent Lifecycle Management
✔ Security Controls & Data Breach Handling
✔ Data Subject Rights, Retention & Deletion
✔ Cross-Border Data Transfers Rules
✔ Responsibilities of Significant Data Fiduciaries (SDFs)
✔ Live Industry Q&A — Practical Insights!
Why You Should Attend
Earn a CPE Certificate
Get Free Career Mentorship from industry experts
Learn proven implementation strategies — beyond the legal text
Stay ahead of regulatory changes before they become mandatory
#DPDPA #DataProtectionIndia #PrivacyCompliance #DataGovernance #CyberLaw #InfoSecTrain #FreeWebinar #ComplianceProfessionals #DataSecurity #DPO #DigitalPrivacy #RegTech #CareerGrowth #CPECredits
📢 FREE Masterclass Alert!
From Law to Practice: Implementing the 2025 DPDPA Rules in Your Business
India’s Data Protection landscape is entering a new era is your organization ready to comply? Join our live masterclass and learn how to transform the 2025 DPDPA requirements into real, actionable business practices that strengthen compliance and build customer trust.
📅 Date: 13 Dec (Saturday)
🕚 Time: 11 AM – 1 PM (IST)
🎙 Speaker: Vasanth Kumar
🔗 Free Registration: https://www.infosectrain.com/events/from-law-to-practice-implementing-the-2025-dpdpa-rules-in-your-business/
💡 What You’ll Learn (Agenda Highlights)
✔ Understanding DPDPA Scope & Key Roles
✔ Lawful Bases & Transparent Notices
✔ End-to-End Consent Lifecycle Management
✔ Security Controls & Data Breach Handling
✔ Data Subject Rights, Retention & Deletion
✔ Cross-Border Data Transfers Rules
✔ Responsibilities of Significant Data Fiduciaries (SDFs)
✔ Live Industry Q&A — Practical Insights!
🎯 Why You Should Attend
👉 Earn a CPE Certificate 🏅
👉 Get Free Career Mentorship from industry experts
👉 Learn proven implementation strategies — beyond the legal text
👉 Stay ahead of regulatory changes before they become mandatory
#DPDPA #DataProtectionIndia #PrivacyCompliance #DataGovernance #CyberLaw #InfoSecTrain #FreeWebinar #ComplianceProfessionals #DataSecurity #DPO #DigitalPrivacy #RegTech #CareerGrowth #CPECredits
0 Commenti
0 condivisioni
4500 Views
0 Anteprima