𝐌𝐚𝐬𝐭𝐞𝐫𝐢𝐧𝐠 𝐃𝐨𝐦𝐚𝐢𝐧 𝟓 𝐨𝐟 𝐈𝐒𝐂𝟐 𝐂𝐂: 𝐄𝐬𝐬𝐞𝐧𝐭𝐢𝐚𝐥 𝐒𝐤𝐢𝐥𝐥𝐬 𝐢𝐧 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧𝐬, 𝐃𝐚𝐭𝐚 𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧, 𝐚𝐧𝐝 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧 𝐓𝐞𝐜𝐡𝐧𝐢𝐪𝐮𝐞𝐬
𝐖𝐡𝐚𝐭 𝐘𝐨𝐮’𝐥𝐥 𝐋𝐞𝐚𝐫𝐧:
𝐃𝐚𝐭𝐚 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 & 𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧: Understand how to safeguard sensitive information against threats.
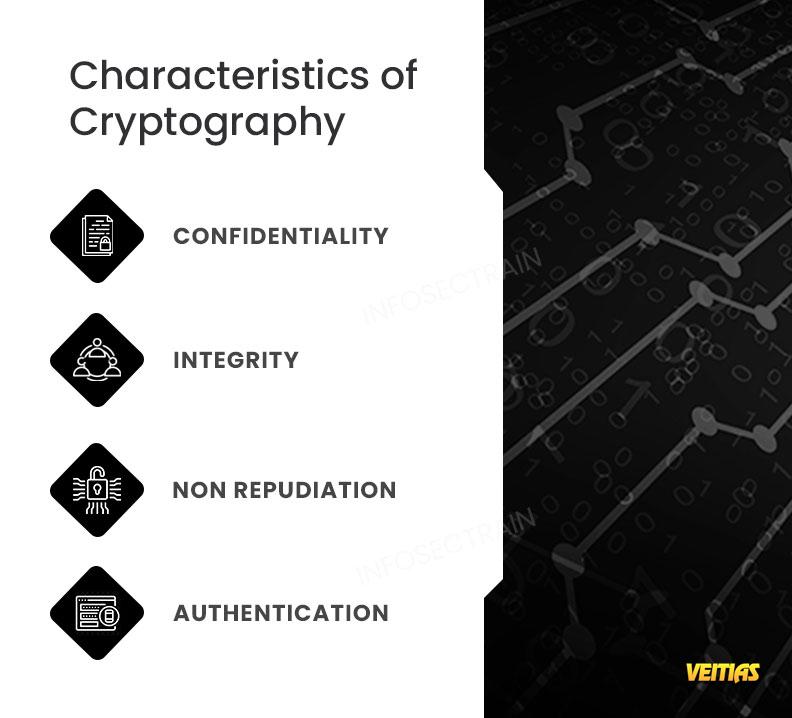
🛡 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧 & 𝐇𝐚𝐬𝐡𝐢𝐧𝐠:
Encryption transforms data into unreadable formats, ensuring confidentiality.
Hashing verifies data integrity, detecting tampering or unauthorized changes.
𝐓𝐲𝐩𝐞𝐬 𝐨𝐟 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧:
𝐒𝐲𝐦𝐦𝐞𝐭𝐫𝐢𝐜 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧: Uses a single key for both encryption and decryption. Ideal for high-speed data transfer and storage.
𝐀𝐬𝐲𝐦𝐦𝐞𝐭𝐫𝐢𝐜 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧: Utilizes a key pair (public/private) for secure exchanges perfect for secure communications, digital signatures, and key exchange.
𝐁𝐞𝐬𝐭 𝐏𝐫𝐚𝐜𝐭𝐢𝐜𝐞𝐬 𝐟𝐨𝐫 𝐈𝐦𝐩𝐥𝐞𝐦𝐞𝐧𝐭𝐢𝐧𝐠 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧:
Proper key management
Regular updates and patches
Using strong algorithms and protocols
Layering security measures for comprehensive protection
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/isc2-cc-domain-5-security-operations/
#Cybersecurity #ISC2CC #SecurityOperations #DataProtection #Encryption #Hashing #InfoSec #ProfessionalDevelopment #CybersecurityTraining #infosectrain
𝐖𝐡𝐚𝐭 𝐘𝐨𝐮’𝐥𝐥 𝐋𝐞𝐚𝐫𝐧:
𝐃𝐚𝐭𝐚 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 & 𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧: Understand how to safeguard sensitive information against threats.
🛡 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧 & 𝐇𝐚𝐬𝐡𝐢𝐧𝐠:
Encryption transforms data into unreadable formats, ensuring confidentiality.
Hashing verifies data integrity, detecting tampering or unauthorized changes.
𝐓𝐲𝐩𝐞𝐬 𝐨𝐟 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧:
𝐒𝐲𝐦𝐦𝐞𝐭𝐫𝐢𝐜 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧: Uses a single key for both encryption and decryption. Ideal for high-speed data transfer and storage.
𝐀𝐬𝐲𝐦𝐦𝐞𝐭𝐫𝐢𝐜 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧: Utilizes a key pair (public/private) for secure exchanges perfect for secure communications, digital signatures, and key exchange.
𝐁𝐞𝐬𝐭 𝐏𝐫𝐚𝐜𝐭𝐢𝐜𝐞𝐬 𝐟𝐨𝐫 𝐈𝐦𝐩𝐥𝐞𝐦𝐞𝐧𝐭𝐢𝐧𝐠 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧:
Proper key management
Regular updates and patches
Using strong algorithms and protocols
Layering security measures for comprehensive protection
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/isc2-cc-domain-5-security-operations/
#Cybersecurity #ISC2CC #SecurityOperations #DataProtection #Encryption #Hashing #InfoSec #ProfessionalDevelopment #CybersecurityTraining #infosectrain
𝐌𝐚𝐬𝐭𝐞𝐫𝐢𝐧𝐠 𝐃𝐨𝐦𝐚𝐢𝐧 𝟓 𝐨𝐟 𝐈𝐒𝐂𝟐 𝐂𝐂: 𝐄𝐬𝐬𝐞𝐧𝐭𝐢𝐚𝐥 𝐒𝐤𝐢𝐥𝐥𝐬 𝐢𝐧 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧𝐬, 𝐃𝐚𝐭𝐚 𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧, 𝐚𝐧𝐝 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧 𝐓𝐞𝐜𝐡𝐧𝐢𝐪𝐮𝐞𝐬
👉 𝐖𝐡𝐚𝐭 𝐘𝐨𝐮’𝐥𝐥 𝐋𝐞𝐚𝐫𝐧:
🔒 𝐃𝐚𝐭𝐚 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 & 𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧: Understand how to safeguard sensitive information against threats.
🛡 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧 & 𝐇𝐚𝐬𝐡𝐢𝐧𝐠:
Encryption transforms data into unreadable formats, ensuring confidentiality.
Hashing verifies data integrity, detecting tampering or unauthorized changes.
🔑 𝐓𝐲𝐩𝐞𝐬 𝐨𝐟 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧:
🔹 𝐒𝐲𝐦𝐦𝐞𝐭𝐫𝐢𝐜 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧: Uses a single key for both encryption and decryption. Ideal for high-speed data transfer and storage.
🔹𝐀𝐬𝐲𝐦𝐦𝐞𝐭𝐫𝐢𝐜 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧: Utilizes a key pair (public/private) for secure exchanges perfect for secure communications, digital signatures, and key exchange.
𝐁𝐞𝐬𝐭 𝐏𝐫𝐚𝐜𝐭𝐢𝐜𝐞𝐬 𝐟𝐨𝐫 𝐈𝐦𝐩𝐥𝐞𝐦𝐞𝐧𝐭𝐢𝐧𝐠 𝐄𝐧𝐜𝐫𝐲𝐩𝐭𝐢𝐨𝐧:
🔸 Proper key management
🔸Regular updates and patches
🔸Using strong algorithms and protocols
🔸Layering security measures for comprehensive protection
👉 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/isc2-cc-domain-5-security-operations/
#Cybersecurity #ISC2CC #SecurityOperations #DataProtection #Encryption #Hashing #InfoSec #ProfessionalDevelopment #CybersecurityTraining #infosectrain
0 Commentarii
0 Distribuiri
4612 Views
0 previzualizare