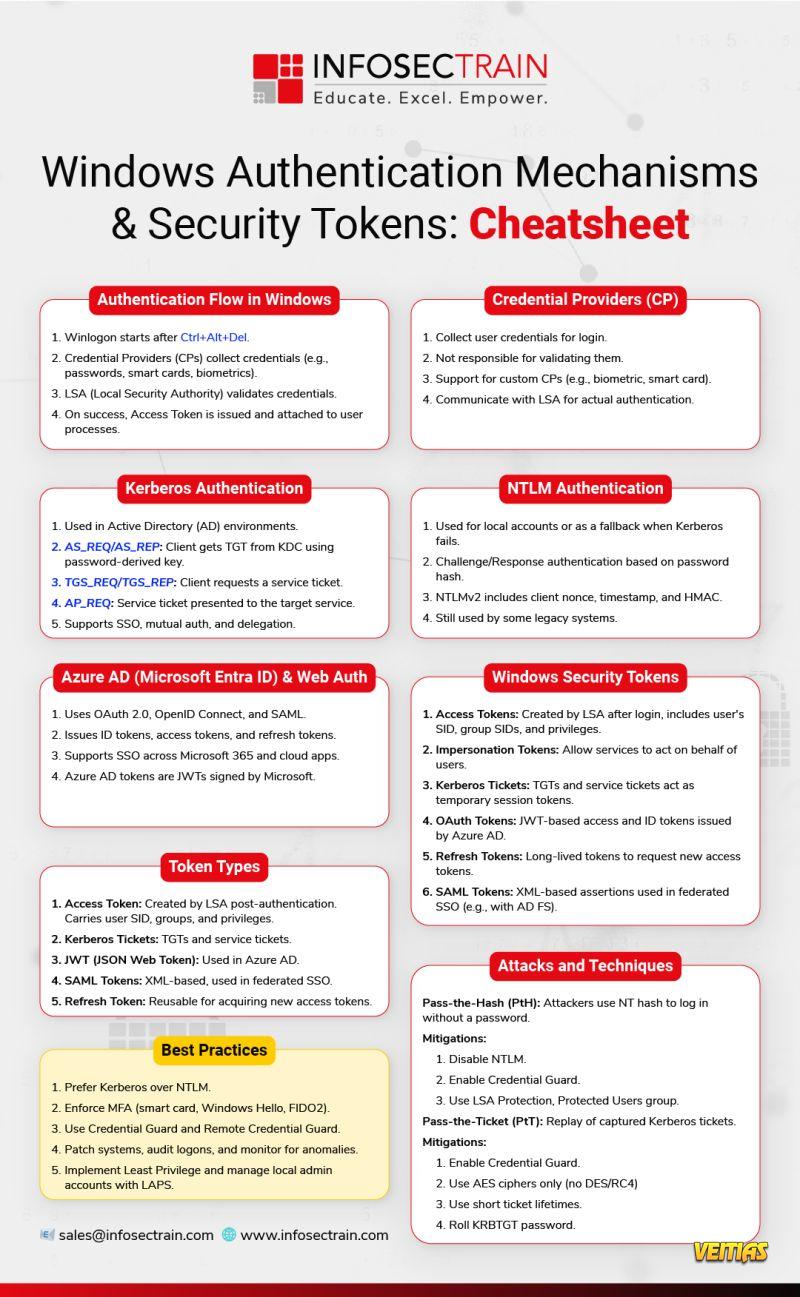
Struggling to remember Windows Authentication flows, token types, or best practices?
We’ve got you covered with this all-in-one Cheatsheet for Windows Authentication Mechanisms & Security Tokens!
What’s inside:
Windows login flow & Credential Providers
Kerberos vs. NTLM authentication
Azure AD & Web Auth simplified
Token types: Access, JWT, SAML, Refresh
Security tokens & attack mitigations
Pro tips & best practices
Download the Cheatsheet & Strengthen Your Windows Security Game!
#WindowsSecurity #Authentication #Kerberos #NTLM #Cybersecurity #SecurityTokens #AzureAD #InfoSecTrain #WindowsAuth #ITSecurity #SysAdminTools #CyberEssentials #SecurityCheatsheet #AccessTokens
We’ve got you covered with this all-in-one Cheatsheet for Windows Authentication Mechanisms & Security Tokens!
What’s inside:
Windows login flow & Credential Providers
Kerberos vs. NTLM authentication
Azure AD & Web Auth simplified
Token types: Access, JWT, SAML, Refresh
Security tokens & attack mitigations
Pro tips & best practices
Download the Cheatsheet & Strengthen Your Windows Security Game!
#WindowsSecurity #Authentication #Kerberos #NTLM #Cybersecurity #SecurityTokens #AzureAD #InfoSecTrain #WindowsAuth #ITSecurity #SysAdminTools #CyberEssentials #SecurityCheatsheet #AccessTokens
Struggling to remember Windows Authentication flows, token types, or best practices?
We’ve got you covered with this all-in-one Cheatsheet for Windows Authentication Mechanisms & Security Tokens!
📌 What’s inside:
✅ Windows login flow & Credential Providers
✅ Kerberos vs. NTLM authentication
✅ Azure AD & Web Auth simplified
✅ Token types: Access, JWT, SAML, Refresh
✅ Security tokens & attack mitigations
✅ Pro tips & best practices
📥 Download the Cheatsheet & Strengthen Your Windows Security Game!
#WindowsSecurity #Authentication #Kerberos #NTLM #Cybersecurity #SecurityTokens #AzureAD #InfoSecTrain #WindowsAuth #ITSecurity #SysAdminTools #CyberEssentials #SecurityCheatsheet #AccessTokens
0 Comentários
0 Compartilhamentos
4121 Visualizações
0 Anterior