𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐨𝐧 & 𝐎𝐫𝐜𝐡𝐞𝐬𝐭𝐫𝐚𝐭𝐢𝐨𝐧: 𝐓𝐡𝐞 𝐅𝐮𝐭𝐮𝐫𝐞 𝐨𝐟 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐃𝐞𝐟𝐞𝐧𝐬𝐞
Do you ever feel as if cybersecurity threats are advancing faster than we can respond? This is where automation and orchestration come in.
𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐨𝐧 does the repetitive security tasks automatically and accurately.
𝐎𝐫𝐜𝐡𝐞𝐬𝐭𝐫𝐚𝐭𝐢𝐨𝐧 connects all your tools and processes so they can work together.
Together they:
Streamline IT processes
Improve efficiency
Improve threat detection & response
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐛𝐥𝐨𝐠 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/importance-of-automation-and-orchestration/
Learn. Grow. Lead. Explore Infosec Train’s 𝐟𝐫𝐞𝐞 𝐰𝐞𝐛𝐢𝐧𝐚𝐫𝐬 𝐭𝐨𝐝𝐚𝐲 https://www.infosectrain.com/events/
#CyberSecurity #CompTIASecurityPlus #Automation #Orchestration #ThreatDetection #SY0701 #InfosecTrain #CyberDefense #ITSecurity
Do you ever feel as if cybersecurity threats are advancing faster than we can respond? This is where automation and orchestration come in.
𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐨𝐧 does the repetitive security tasks automatically and accurately.
𝐎𝐫𝐜𝐡𝐞𝐬𝐭𝐫𝐚𝐭𝐢𝐨𝐧 connects all your tools and processes so they can work together.
Together they:
Streamline IT processes
Improve efficiency
Improve threat detection & response
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐛𝐥𝐨𝐠 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/importance-of-automation-and-orchestration/
Learn. Grow. Lead. Explore Infosec Train’s 𝐟𝐫𝐞𝐞 𝐰𝐞𝐛𝐢𝐧𝐚𝐫𝐬 𝐭𝐨𝐝𝐚𝐲 https://www.infosectrain.com/events/
#CyberSecurity #CompTIASecurityPlus #Automation #Orchestration #ThreatDetection #SY0701 #InfosecTrain #CyberDefense #ITSecurity
𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐨𝐧 & 𝐎𝐫𝐜𝐡𝐞𝐬𝐭𝐫𝐚𝐭𝐢𝐨𝐧: 𝐓𝐡𝐞 𝐅𝐮𝐭𝐮𝐫𝐞 𝐨𝐟 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐃𝐞𝐟𝐞𝐧𝐬𝐞
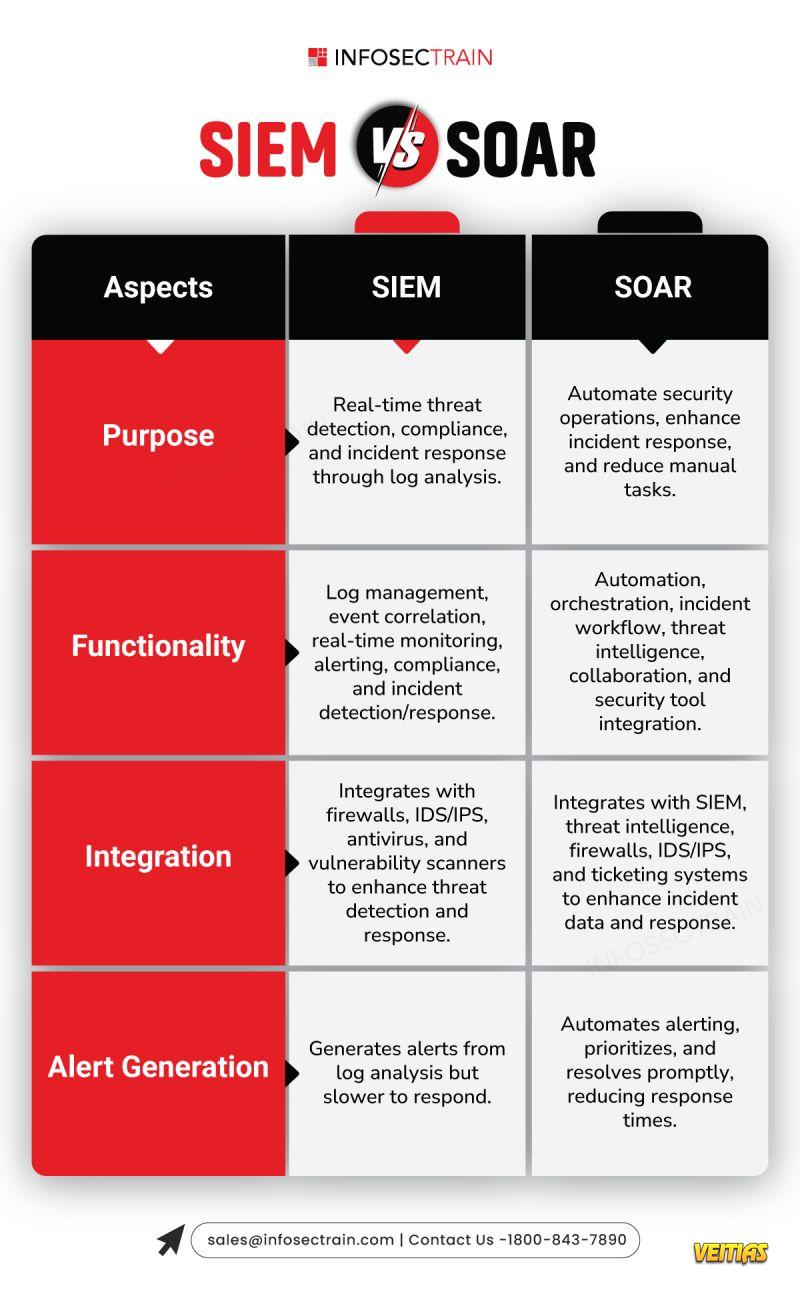
Do you ever feel as if cybersecurity threats are advancing faster than we can respond? This is where automation and orchestration come in.
🔹 𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐨𝐧 does the repetitive security tasks automatically and accurately.
🔹 𝐎𝐫𝐜𝐡𝐞𝐬𝐭𝐫𝐚𝐭𝐢𝐨𝐧 connects all your tools and processes so they can work together.
Together they:
✅ Streamline IT processes
✅ Improve efficiency
✅ Improve threat detection & response
👉 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐛𝐥𝐨𝐠 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/importance-of-automation-and-orchestration/
Learn. Grow. Lead. Explore Infosec Train’s 𝐟𝐫𝐞𝐞 𝐰𝐞𝐛𝐢𝐧𝐚𝐫𝐬 𝐭𝐨𝐝𝐚𝐲 👉 https://www.infosectrain.com/events/
#CyberSecurity #CompTIASecurityPlus #Automation #Orchestration #ThreatDetection #SY0701 #InfosecTrain #CyberDefense #ITSecurity
0 Σχόλια
0 Μοιράστηκε
3800 Views
0 Προεπισκόπηση