Cybersecurity isn’t just firewalls and passwords — it’s an ecosystem.
Every domain plays a role in protecting data, systems, and trust.
Here’s what modern cybersecurity mastery really looks like
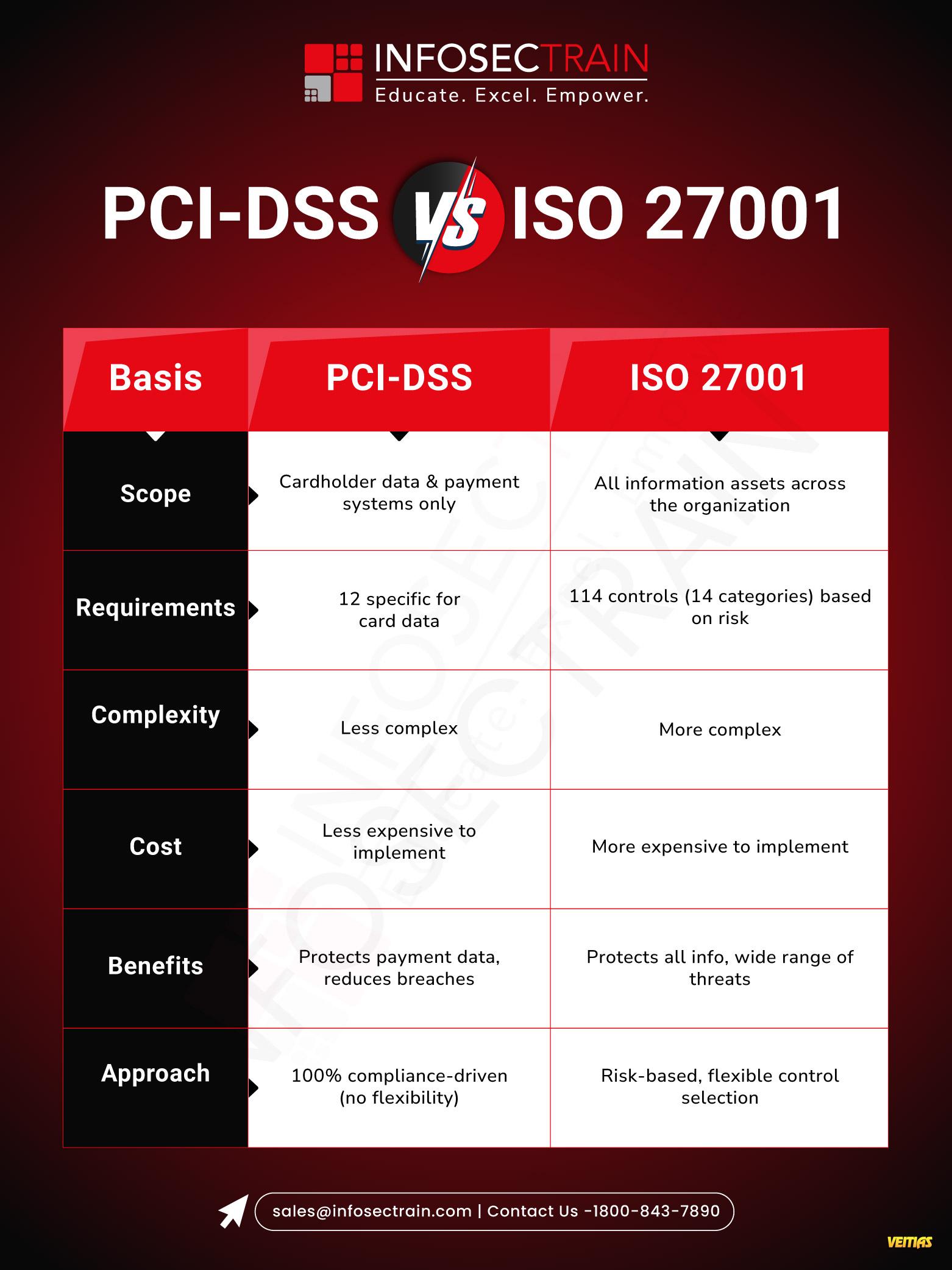
𝟏. 𝐆𝐨𝐯𝐞𝐫𝐧𝐚𝐧𝐜𝐞, 𝐑𝐢𝐬𝐤 & 𝐏𝐫𝐢𝐯𝐚𝐜𝐲
Frameworks that define trust — ISO 27001, NIST CSF, GDPR, DPDPA, HIPAA.
Risk assessments, vendor risks, and data protection aren’t checkboxes — they’re business enablers.
𝟐. 𝐓𝐞𝐜𝐡𝐧𝐢𝐜𝐚𝐥 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲
From firewalls to Zero Trust, EDR to CNAPP, and OWASP to DevSecOps — defense starts with layered protection across networks, endpoints, cloud, and code.
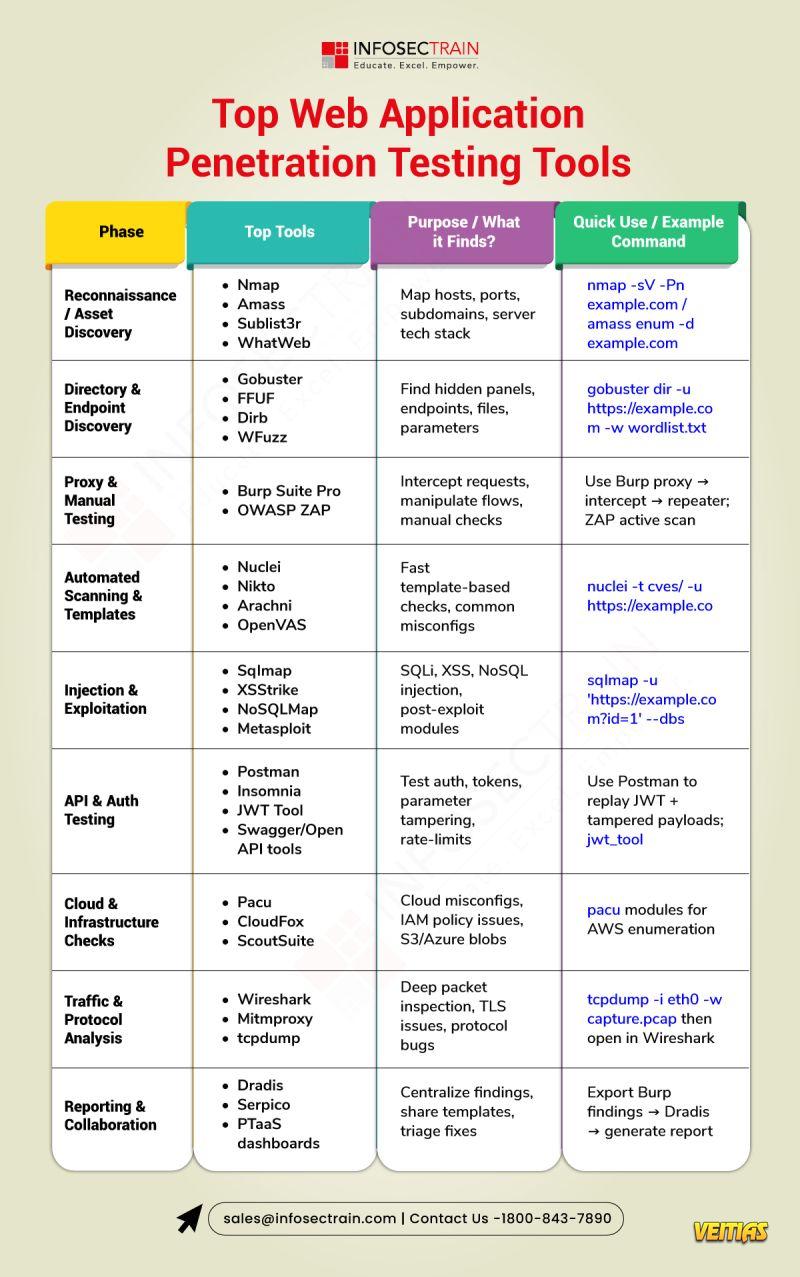
3. 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧𝐬
SOC, SIEM, and SOAR keep the pulse.
Incident response, pen testing, and threat intel turn data into action.
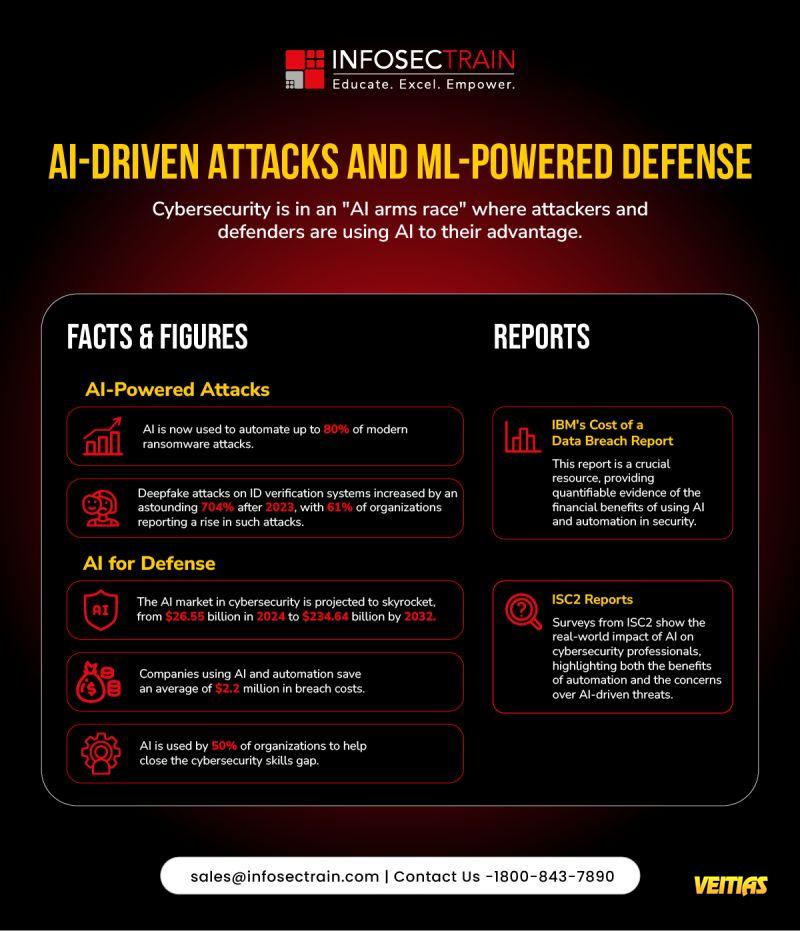
𝟒. 𝐀𝐫𝐜𝐡𝐢𝐭𝐞𝐜𝐭𝐮𝐫𝐞 & 𝐄𝐦𝐞𝐫𝐠𝐢𝐧𝐠 𝐓𝐞𝐜𝐡
Design with security at the core: Zero Trust, AI governance (ISO 42001, EU AI Act), and resilient architectures for cloud and enterprise systems.
Every domain plays a role in protecting data, systems, and trust.
Here’s what modern cybersecurity mastery really looks like
𝟏. 𝐆𝐨𝐯𝐞𝐫𝐧𝐚𝐧𝐜𝐞, 𝐑𝐢𝐬𝐤 & 𝐏𝐫𝐢𝐯𝐚𝐜𝐲
Frameworks that define trust — ISO 27001, NIST CSF, GDPR, DPDPA, HIPAA.
Risk assessments, vendor risks, and data protection aren’t checkboxes — they’re business enablers.
𝟐. 𝐓𝐞𝐜𝐡𝐧𝐢𝐜𝐚𝐥 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲
From firewalls to Zero Trust, EDR to CNAPP, and OWASP to DevSecOps — defense starts with layered protection across networks, endpoints, cloud, and code.
3. 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧𝐬
SOC, SIEM, and SOAR keep the pulse.
Incident response, pen testing, and threat intel turn data into action.
𝟒. 𝐀𝐫𝐜𝐡𝐢𝐭𝐞𝐜𝐭𝐮𝐫𝐞 & 𝐄𝐦𝐞𝐫𝐠𝐢𝐧𝐠 𝐓𝐞𝐜𝐡
Design with security at the core: Zero Trust, AI governance (ISO 42001, EU AI Act), and resilient architectures for cloud and enterprise systems.
Cybersecurity isn’t just firewalls and passwords — it’s an ecosystem.
Every domain plays a role in protecting data, systems, and trust.
Here’s what modern cybersecurity mastery really looks like 👇
🔐 𝟏. 𝐆𝐨𝐯𝐞𝐫𝐧𝐚𝐧𝐜𝐞, 𝐑𝐢𝐬𝐤 & 𝐏𝐫𝐢𝐯𝐚𝐜𝐲
Frameworks that define trust — ISO 27001, NIST CSF, GDPR, DPDPA, HIPAA.
Risk assessments, vendor risks, and data protection aren’t checkboxes — they’re business enablers.
🛡️ 𝟐. 𝐓𝐞𝐜𝐡𝐧𝐢𝐜𝐚𝐥 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲
From firewalls to Zero Trust, EDR to CNAPP, and OWASP to DevSecOps — defense starts with layered protection across networks, endpoints, cloud, and code.
🧠 3. 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧𝐬
SOC, SIEM, and SOAR keep the pulse.
Incident response, pen testing, and threat intel turn data into action.
🏗️ 𝟒. 𝐀𝐫𝐜𝐡𝐢𝐭𝐞𝐜𝐭𝐮𝐫𝐞 & 𝐄𝐦𝐞𝐫𝐠𝐢𝐧𝐠 𝐓𝐞𝐜𝐡
Design with security at the core: Zero Trust, AI governance (ISO 42001, EU AI Act), and resilient architectures for cloud and enterprise systems.
0 Comments
0 Shares
1096 Views
0 Reviews