𝐀𝐈 𝐆𝐨𝐯𝐞𝐫𝐧𝐚𝐧𝐜𝐞: 𝐓𝐡𝐞 𝐍𝐞𝐰 𝐌𝐮𝐬𝐭-𝐇𝐚𝐯𝐞 𝐒𝐤𝐢𝐥𝐥 𝐟𝐨𝐫 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐫𝐨𝐟𝐞𝐬𝐬𝐢𝐨𝐧𝐚𝐥𝐬
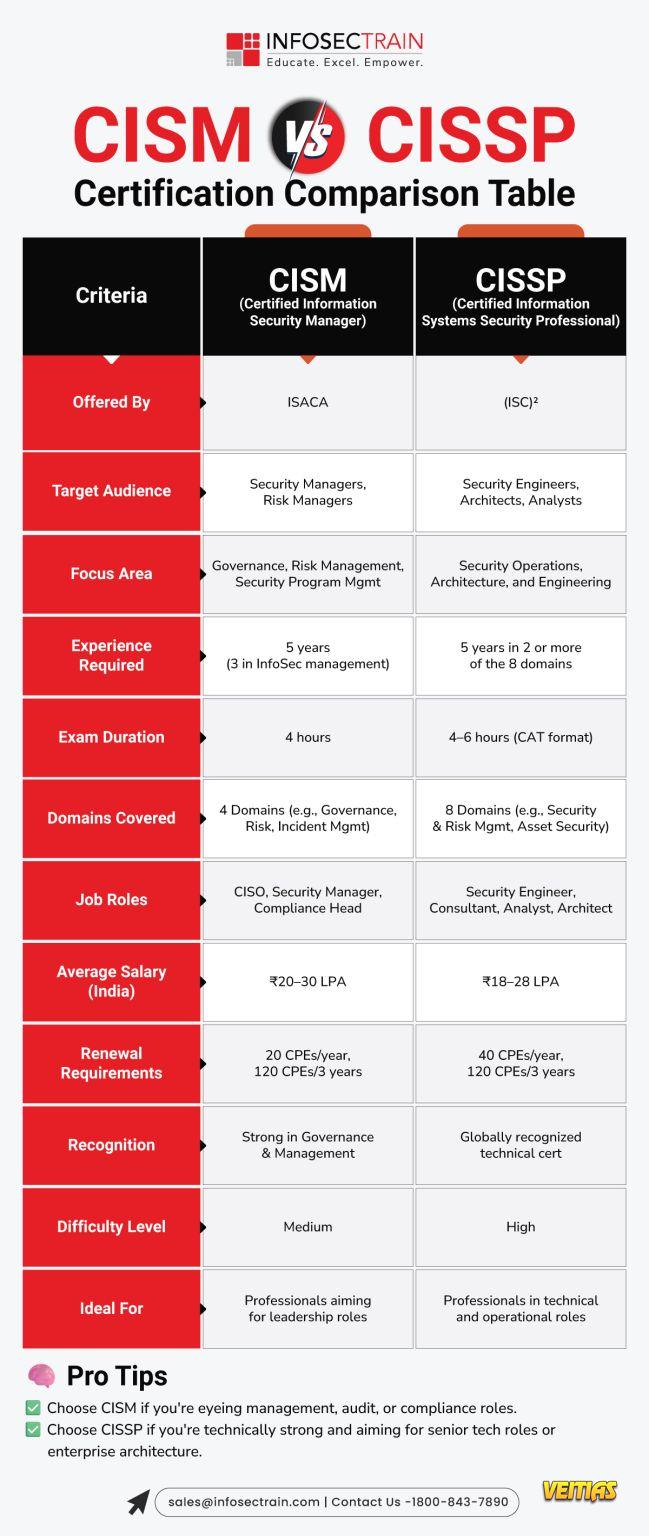
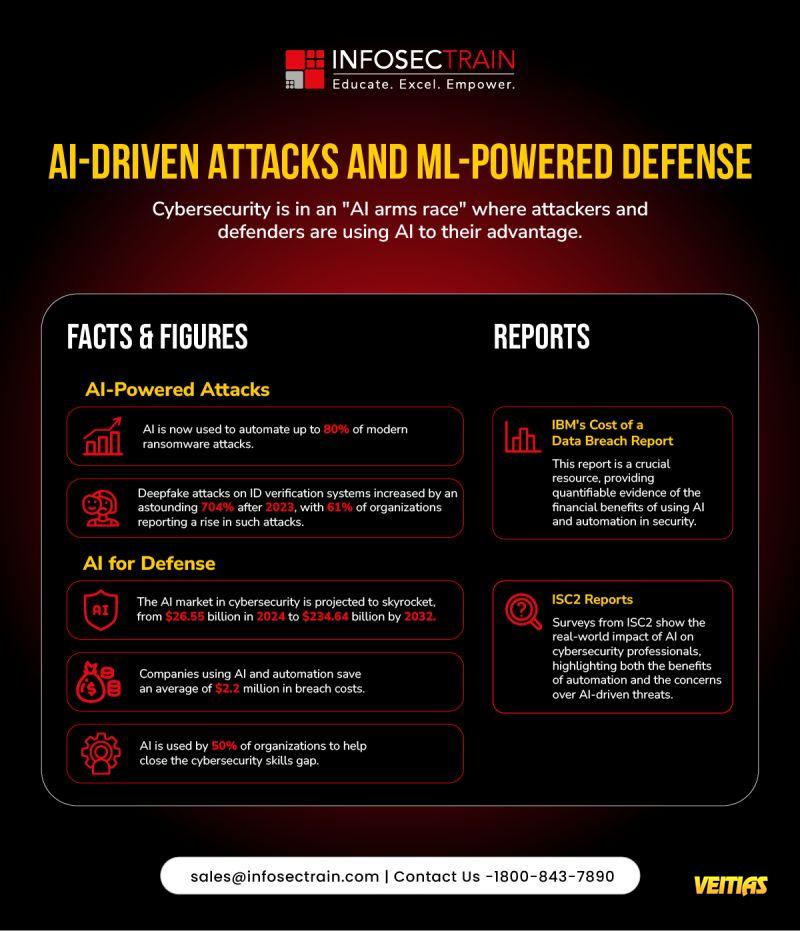
AI isn’t just transforming technology, it’s reshaping 𝐫𝐢𝐬𝐤, 𝐜𝐨𝐦𝐩𝐥𝐢𝐚𝐧𝐜𝐞, 𝐚𝐧𝐝 𝐞𝐧𝐭𝐞𝐫𝐩𝐫𝐢𝐬𝐞 𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲. For CISSP and CISM-certified pros, understanding AI governance is no longer optional; it’s critical.
𝐖𝐡𝐲 𝐢𝐭 𝐦𝐚𝐭𝐭𝐞𝐫𝐬:
• Adversarial attacks, model bias & fines up to $35M
• Legal & regulatory compliance is now your responsibility
• Elevate security from a cost center to a strategic business partner
• Poor AI governance = financial loss + reputation risk
𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/why-is-ai-governance-a-crucial-skill-for-information-security-professionals
AI governance isn’t a checkbox it’s your pathway to strategic cybersecurity leadership.
#CyberSecurity #AI #AIGovernance #CISSP #CISM #InfosecTrain #CyberLeadership #AICompliance #EnterpriseSecurity #CyberSkills #AdvancedSecurity
AI isn’t just transforming technology, it’s reshaping 𝐫𝐢𝐬𝐤, 𝐜𝐨𝐦𝐩𝐥𝐢𝐚𝐧𝐜𝐞, 𝐚𝐧𝐝 𝐞𝐧𝐭𝐞𝐫𝐩𝐫𝐢𝐬𝐞 𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲. For CISSP and CISM-certified pros, understanding AI governance is no longer optional; it’s critical.
𝐖𝐡𝐲 𝐢𝐭 𝐦𝐚𝐭𝐭𝐞𝐫𝐬:
• Adversarial attacks, model bias & fines up to $35M
• Legal & regulatory compliance is now your responsibility
• Elevate security from a cost center to a strategic business partner
• Poor AI governance = financial loss + reputation risk
𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/why-is-ai-governance-a-crucial-skill-for-information-security-professionals
AI governance isn’t a checkbox it’s your pathway to strategic cybersecurity leadership.
#CyberSecurity #AI #AIGovernance #CISSP #CISM #InfosecTrain #CyberLeadership #AICompliance #EnterpriseSecurity #CyberSkills #AdvancedSecurity
𝐀𝐈 𝐆𝐨𝐯𝐞𝐫𝐧𝐚𝐧𝐜𝐞: 𝐓𝐡𝐞 𝐍𝐞𝐰 𝐌𝐮𝐬𝐭-𝐇𝐚𝐯𝐞 𝐒𝐤𝐢𝐥𝐥 𝐟𝐨𝐫 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐫𝐨𝐟𝐞𝐬𝐬𝐢𝐨𝐧𝐚𝐥𝐬
AI isn’t just transforming technology, it’s reshaping 𝐫𝐢𝐬𝐤, 𝐜𝐨𝐦𝐩𝐥𝐢𝐚𝐧𝐜𝐞, 𝐚𝐧𝐝 𝐞𝐧𝐭𝐞𝐫𝐩𝐫𝐢𝐬𝐞 𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲. For CISSP and CISM-certified pros, understanding AI governance is no longer optional; it’s critical.
✅ 𝐖𝐡𝐲 𝐢𝐭 𝐦𝐚𝐭𝐭𝐞𝐫𝐬:
• Adversarial attacks, model bias & fines up to $35M
• Legal & regulatory compliance is now your responsibility
• Elevate security from a cost center to a strategic business partner
• Poor AI governance = financial loss + reputation risk
👉 𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/why-is-ai-governance-a-crucial-skill-for-information-security-professionals
✅ AI governance isn’t a checkbox ➡️ it’s your pathway to strategic cybersecurity leadership.
#CyberSecurity #AI #AIGovernance #CISSP #CISM #InfosecTrain #CyberLeadership #AICompliance #EnterpriseSecurity #CyberSkills #AdvancedSecurity
0 Commenti
0 condivisioni
5140 Views
0 Anteprima