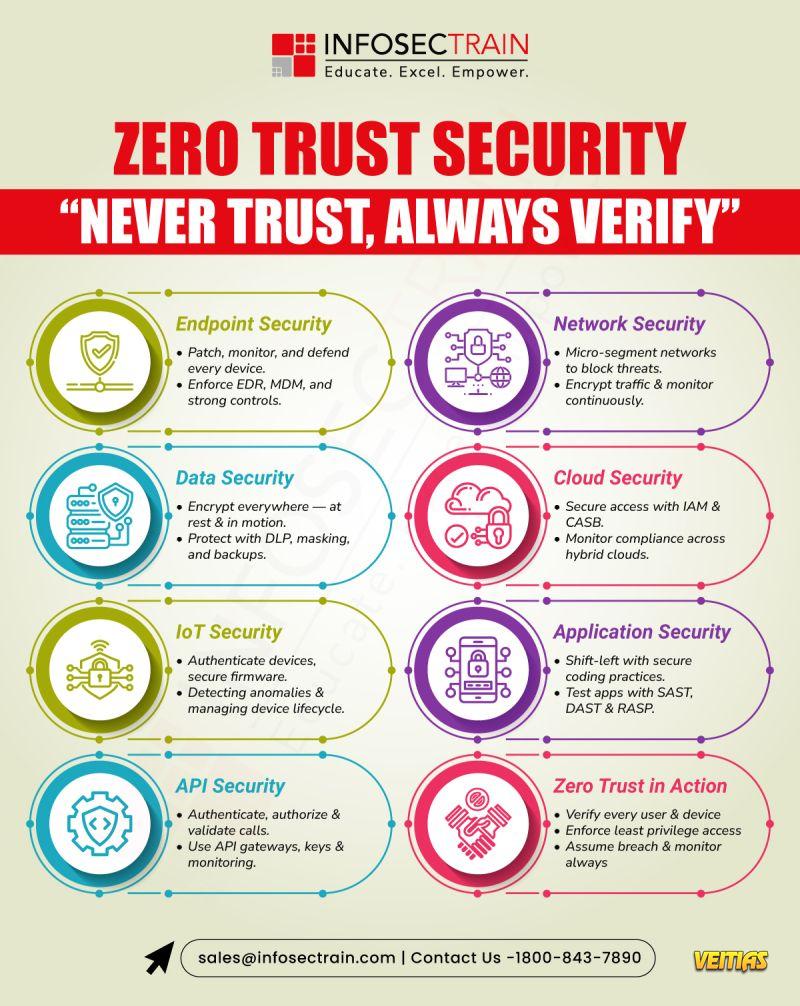
Perimeter defenses are no longer enough.
Zero Trust protects every layer — 𝐮𝐬𝐞𝐫𝐬, 𝐝𝐞𝐯𝐢𝐜𝐞𝐬, 𝐝𝐚𝐭𝐚, 𝐚𝐧𝐝 𝐚𝐩𝐩𝐬 — through continuous verification and least privilege access.
𝐄𝐧𝐝𝐩𝐨𝐢𝐧𝐭𝐬: Patch, monitor, defend with EDR & MDM
𝐍𝐞𝐭𝐰𝐨𝐫𝐤: Micro-segment & encrypt traffic
𝐃𝐚𝐭𝐚: Encrypt, back up, and apply DLP
𝐂𝐥𝐨𝐮𝐝: Control access with IAM & CASB
𝐀𝐩𝐩𝐬 & 𝐀𝐏𝐈𝐬: Secure code, test, and validate every call
Assume breach. Verify everything. Trust nothing.
Zero Trust protects every layer — 𝐮𝐬𝐞𝐫𝐬, 𝐝𝐞𝐯𝐢𝐜𝐞𝐬, 𝐝𝐚𝐭𝐚, 𝐚𝐧𝐝 𝐚𝐩𝐩𝐬 — through continuous verification and least privilege access.
𝐄𝐧𝐝𝐩𝐨𝐢𝐧𝐭𝐬: Patch, monitor, defend with EDR & MDM
𝐍𝐞𝐭𝐰𝐨𝐫𝐤: Micro-segment & encrypt traffic
𝐃𝐚𝐭𝐚: Encrypt, back up, and apply DLP
𝐂𝐥𝐨𝐮𝐝: Control access with IAM & CASB
𝐀𝐩𝐩𝐬 & 𝐀𝐏𝐈𝐬: Secure code, test, and validate every call
Assume breach. Verify everything. Trust nothing.
Perimeter defenses are no longer enough.
Zero Trust protects every layer — 𝐮𝐬𝐞𝐫𝐬, 𝐝𝐞𝐯𝐢𝐜𝐞𝐬, 𝐝𝐚𝐭𝐚, 𝐚𝐧𝐝 𝐚𝐩𝐩𝐬 — through continuous verification and least privilege access.
💻 𝐄𝐧𝐝𝐩𝐨𝐢𝐧𝐭𝐬: Patch, monitor, defend with EDR & MDM
🌐 𝐍𝐞𝐭𝐰𝐨𝐫𝐤: Micro-segment & encrypt traffic
🧩 𝐃𝐚𝐭𝐚: Encrypt, back up, and apply DLP
☁️ 𝐂𝐥𝐨𝐮𝐝: Control access with IAM & CASB
🧱 𝐀𝐩𝐩𝐬 & 𝐀𝐏𝐈𝐬: Secure code, test, and validate every call
Assume breach. Verify everything. Trust nothing.
0 Комментарии
0 Поделились
2841 Просмотры
0 предпросмотр