Recent Updates
All Countries
All Countries
Saint Kitts and Nevis
Palau
Pakistan
Oman
Norway
Northern Mariana Islands
Norfolk Island
Niue
Nigeria
Niger
Nicaragua
New Zealand
New Caledonia
Netherlands Antilles
Palestine
Panama
Rwanda
Russian Federation
Romania
Reunion
Qatar
Puerto Rico
Portugal
Poland
Pitcairn
Philippines
Peru
Paraguay
Papua New Guinea
Netherlands
Nepal
Nauru
Marshall Islands
Malta
Mali
Maldives
Malaysia
Malawi
Madagascar
Macedonia
Macau
Luxembourg
Lithuania
Liechtenstein
Libyan Arab Jamahiriya
Martinique
Mauritania
Namibia
Myanmar
Mozambique
Morocco
Montserrat
Montenegro
Mongolia
Monaco
Moldova, Republic of
Micronesia, Federated States of
Mexico
Mayotte
Mauritius
Liberia
Zimbabwe
United Kingdom
United Arab Emirates
Ukraine
Uganda
Tuvalu
Turks and Caicos Islands
Turkmenistan
Turkey
Tunisia
Trinidad and Tobago
Tonga
Tokelau
Togo
United States
United States minor outlying islands
Zambia
Zaire
Yemen
Western Sahara
Wallis and Futuna Islands
Virgin Islands (U.S.)
Virgin Islands (British)
Vietnam
Venezuela
Vatican City State
Vanuatu
Uzbekistan
Uruguay
Thailand
Tanzania, United Republic of
Tajikistan
Solomon Islands
Slovenia
Slovakia
Singapore
Sierra Leone
Seychelles
Serbia
Senegal
Saudi Arabia
Sao Tome and Principe
San Marino
Samoa
Saint Vincent and the Grenadines
Somalia
South Africa
Taiwan
Syrian Arab Republic
Switzerland
Sweden
Swaziland
Svalbard and Jan Mayen Islands
Suriname
Sudan
St. Pierre and Miquelon
St. Helena
Sri Lanka
Spain
South Georgia South Sandwich Islands
Saint Lucia
Lesotho
Ecuador
Christmas Island
China
Chile
Chad
Central African Republic
Cayman Islands
Cape Verde
Canada
Cameroon
Cambodia
Burundi
Burkina Faso
Bulgaria
Cocos (Keeling) Islands
Colombia
East Timor
Dominican Republic
Dominica
Djibouti
Denmark
Czech Republic
Cyprus
Cuba
Croatia (Hrvatska)
Costa Rica
Cook Islands
Congo
Comoros
Brunei Darussalam
British Indian Ocean Territory
Brazil
Austria
Australia
Aruba
Armenia
Argentina
Antigua and Barbuda
Antarctica
Anguilla
Angola
Andorra
American Samoa
Algeria
Albania
Azerbaijan
Bahamas
Bouvet Island
Botswana
Bosnia and Herzegovina
Bolivia
Bhutan
Bermuda
Benin
Belize
Belgium
Belarus
Barbados
Bangladesh
Bahrain
Afghanistan
Lebanon
Italy
Israel
Ireland
Iraq
Iran (Islamic Republic of)
Indonesia
Isle of Man
India
Iceland
Hungary
Hong Kong
Honduras
Heard and Mc Donald Islands
Ivory Coast
Jersey
Latvia
Lao People's Democratic Republic
Kyrgyzstan
Kuwait
Kosovo
Korea, Republic of
Korea, Democratic People's Republic of
Kiribati
Kenya
Kazakhstan
Jordan
Japan
Jamaica
Haiti
Guyana
Guinea-Bissau
French Polynesia
French Guiana
France, Metropolitan
France
Finland
Fiji
Faroe Islands
Falkland Islands (Malvinas)
Ethiopia
Estonia
Eritrea
Equatorial Guinea
El Salvador
French Southern Territories
Gabon
Guinea
Guatemala
Guam
Guadeloupe
Grenada
Greenland
Greece
Guernsey
Gibraltar
Ghana
Germany
Georgia
Gambia
Egypt
- Free Webinar Alert!
AI-Powered Spreadsheet Skills: Get Smarter with Data
Date: 08 Nov (Sat) Time: 7 – 8 PM (IST) Speaker: Anas Hamid
Format: Free Masterclass + Live Q&A
Register FREE Now:
https://www.infosectrain.com/events/ai-powered-spreadsheet-skills-get-smarter-with-data/
What You’ll Learn:
Explore the spreadsheet workspace — from cells to columns.
Master essential formulas & functions for smarter work.
Organize and structure data like a pro.
Meet your AI assistant — discover AI tools built right into Excel & Google Sheets.
Use plain English to create formulas, clean messy data, and generate instant charts.
Learn how AI recognizes patterns and simplifies your workflow.
End with an engaging interactive Q&A session!
Why Attend?
Earn a CPE Certificate
Get FREE Career Guidance & Mentorship
Learn directly from industry experts
Don’t miss this power-packed learning session that transforms how you work with data!
#AI #Spreadsheets #ExcelTips #GoogleSheets #AIMasterclass #DataAnalysis #InfosecTrain #FreeWebinar #LearnWithExperts #CPE #CareerGrowth🚀 Free Webinar Alert! AI-Powered Spreadsheet Skills: Get Smarter with Data 📊🤖 📅 Date: 08 Nov (Sat) 🕖 Time: 7 – 8 PM (IST) 🎤 Speaker: Anas Hamid 🎓 Format: Free Masterclass + Live Q&A 🔗 Register FREE Now: 👉 https://www.infosectrain.com/events/ai-powered-spreadsheet-skills-get-smarter-with-data/ 💡 What You’ll Learn: ✅ Explore the spreadsheet workspace — from cells to columns. ✅ Master essential formulas & functions for smarter work. ✅ Organize and structure data like a pro. ✅ Meet your AI assistant — discover AI tools built right into Excel & Google Sheets. ✅ Use plain English to create formulas, clean messy data, and generate instant charts. ✅ Learn how AI recognizes patterns and simplifies your workflow. ✅ End with an engaging interactive Q&A session! 🌟 Why Attend? ✨ Earn a CPE Certificate ✨ Get FREE Career Guidance & Mentorship ✨ Learn directly from industry experts 🎯 Don’t miss this power-packed learning session that transforms how you work with data! #AI #Spreadsheets #ExcelTips #GoogleSheets #AIMasterclass #DataAnalysis #InfosecTrain #FreeWebinar #LearnWithExperts #CPE #CareerGrowthWWW.INFOSECTRAIN.COMAI-Powered Spreadsheet Skills: Get Smarter with DataEducate. Excel. Empower.0 Comments 0 Shares 31 Views 0 ReviewsPlease log in to like, share and comment! - 𝐀𝐫𝐭𝐢𝐟𝐢𝐜𝐢𝐚𝐥 𝐈𝐧𝐭𝐞𝐥𝐥𝐢𝐠𝐞𝐧𝐜𝐞: 𝐈𝐧𝐧𝐨𝐯𝐚𝐭𝐢𝐨𝐧 𝐨𝐫 𝐑𝐢𝐬𝐤?
AI is changing the way we work, make things, and connect with the world surrounding us but with these changes come additional challenges we have to address and be responsible for.
This is what we are up against
Model BiasBiased results by poorly trained models.
Privacy BreachesData from users is gathered and abused without their consent.
Cyber Threats Controlled by AIAttacks on autopilot that are more intelligent than traditional defenses.
Oppague “Black box” systems with limited accountability.
Energy Consumption: Significant energy required for AI computation.
Misinformation & Deepfakesfabricate content that influence our opinions and politics.
Ethical Abuse The misuse of technology even if it is cutting ethical boundaries.
𝐑𝐞𝐚𝐥-𝐰𝐨𝐫𝐥𝐝 𝐬𝐜𝐞𝐧𝐚𝐫𝐢𝐨𝐬 𝐢𝐧𝐜𝐥𝐮𝐝𝐢𝐧𝐠 𝐀𝐈-𝐩𝐨𝐰𝐞𝐫𝐞𝐝 𝐡𝐢𝐫𝐢𝐧𝐠 𝐝𝐢𝐬𝐜𝐫𝐢𝐦𝐢𝐧𝐚𝐭𝐢𝐨𝐧 𝐭𝐨 𝐝𝐞𝐞𝐩𝐟𝐚𝐤𝐞 𝐩𝐨𝐥𝐢𝐭𝐢𝐜𝐚𝐥 𝐜𝐚𝐦𝐩𝐚𝐢𝐠𝐧𝐬 𝐬𝐞𝐫𝐯𝐞 𝐚𝐬 𝐚 𝐫𝐞𝐦𝐢𝐧𝐝𝐞𝐫 𝐭𝐡𝐚𝐭 𝐡𝐮𝐦𝐚𝐧 𝐨𝐯𝐞𝐫𝐬𝐢𝐠𝐡𝐭 𝐚𝐧𝐝 𝐫𝐞𝐠𝐮𝐥𝐚𝐭𝐢𝐨𝐧 𝐚𝐫𝐞 𝐧𝐨 𝐥𝐨𝐧𝐠𝐞𝐫 𝐨𝐩𝐭𝐢𝐨𝐧𝐚𝐥; 𝐭𝐡𝐞𝐲 𝐚𝐫𝐞 𝐞𝐬𝐬𝐞𝐧𝐭𝐢𝐚𝐥.
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/ai-associated-risks-and-how-to-mitigate-them/
Infosec Train AI and Cybersecurity Course empowers individuals to better comprehend the threats, develop ethical AI guidelines, and combat emerging digital threats leading to a safe and responsible AI-empowered future.
#ArtificialIntelligence #CyberSecurity #ResponsibleAI #AIethics #AIrisks #DataPrivacy #Deepfakes #TechResponsibility #EthicalAI #AIawareness #DigitalSafety #RiskManagement #Governance #AItraining #InfoSecTrain𝐀𝐫𝐭𝐢𝐟𝐢𝐜𝐢𝐚𝐥 𝐈𝐧𝐭𝐞𝐥𝐥𝐢𝐠𝐞𝐧𝐜𝐞: 𝐈𝐧𝐧𝐨𝐯𝐚𝐭𝐢𝐨𝐧 𝐨𝐫 𝐑𝐢𝐬𝐤? AI is changing the way we work, make things, and connect with the world surrounding us but with these changes come additional challenges we have to address and be responsible for. ☑️ This is what we are up against 👇 🔸 Model Bias➡️Biased results by poorly trained models. 🔸Privacy Breaches➡️Data from users is gathered and abused without their consent. 🔸Cyber Threats Controlled by AI➡️Attacks on autopilot that are more intelligent than traditional defenses. 🔸Oppague➡️ “Black box” systems with limited accountability. 🔸Energy Consumption: Significant energy required for AI computation. 🔸Misinformation & Deepfakes➡️fabricate content that influence our opinions and politics. 🔸Ethical Abuse ➡️ The misuse of technology even if it is cutting ethical boundaries. ☑️ 𝐑𝐞𝐚𝐥-𝐰𝐨𝐫𝐥𝐝 𝐬𝐜𝐞𝐧𝐚𝐫𝐢𝐨𝐬 ➡️𝐢𝐧𝐜𝐥𝐮𝐝𝐢𝐧𝐠 𝐀𝐈-𝐩𝐨𝐰𝐞𝐫𝐞𝐝 𝐡𝐢𝐫𝐢𝐧𝐠 𝐝𝐢𝐬𝐜𝐫𝐢𝐦𝐢𝐧𝐚𝐭𝐢𝐨𝐧 𝐭𝐨 𝐝𝐞𝐞𝐩𝐟𝐚𝐤𝐞 𝐩𝐨𝐥𝐢𝐭𝐢𝐜𝐚𝐥 𝐜𝐚𝐦𝐩𝐚𝐢𝐠𝐧𝐬 ➡️𝐬𝐞𝐫𝐯𝐞 𝐚𝐬 𝐚 𝐫𝐞𝐦𝐢𝐧𝐝𝐞𝐫 𝐭𝐡𝐚𝐭 𝐡𝐮𝐦𝐚𝐧 𝐨𝐯𝐞𝐫𝐬𝐢𝐠𝐡𝐭 𝐚𝐧𝐝 𝐫𝐞𝐠𝐮𝐥𝐚𝐭𝐢𝐨𝐧 𝐚𝐫𝐞 𝐧𝐨 𝐥𝐨𝐧𝐠𝐞𝐫 𝐨𝐩𝐭𝐢𝐨𝐧𝐚𝐥; 𝐭𝐡𝐞𝐲 𝐚𝐫𝐞 𝐞𝐬𝐬𝐞𝐧𝐭𝐢𝐚𝐥. 👉 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/ai-associated-risks-and-how-to-mitigate-them/ 🎓 Infosec Train AI and Cybersecurity Course empowers individuals to better comprehend the threats, develop ethical AI guidelines, and combat emerging digital threats leading to a safe and responsible AI-empowered future. #ArtificialIntelligence #CyberSecurity #ResponsibleAI #AIethics #AIrisks #DataPrivacy #Deepfakes #TechResponsibility #EthicalAI #AIawareness #DigitalSafety #RiskManagement #Governance #AItraining #InfoSecTrainWWW.INFOSECTRAIN.COMAI Associated Risks and How to Mitigate Them?Learn the top AI-associated risks—bias, data leakage, attacks, drift, compliance gaps—and practical mitigation steps to deploy AI safely and responsibly.0 Comments 0 Shares 39 Views 0 Reviews - The 5 Stages of Pentesting | Complete Ethical Hacking Process
Ever wondered how ethical hackers break into systems—legally? Let’s walk through the 5 stages of a real pentest!
Penetration Testing is more than just hacking into systems—it's a structured, ethical approach to discovering vulnerabilities before attackers do. In this video, we dive into the 5 essential stages of a penetration test used by professionals across the globe.
Watch Here: https://youtu.be/_97JwrQopBc?si=4pJMO9vFSKvopbbC
#PenetrationTesting #EthicalHacking #PentestingStages #CyberSecurityTraining #CEH #OSCP #InfosecTrain #VulnerabilityAssessment #RedTeamOps #HackingProcessThe 5 Stages of Pentesting | Complete Ethical Hacking Process Ever wondered how ethical hackers break into systems—legally? Let’s walk through the 5 stages of a real pentest! 🔐 Penetration Testing is more than just hacking into systems—it's a structured, ethical approach to discovering vulnerabilities before attackers do. In this video, we dive into the 5 essential stages of a penetration test used by professionals across the globe. Watch Here: https://youtu.be/_97JwrQopBc?si=4pJMO9vFSKvopbbC #PenetrationTesting #EthicalHacking #PentestingStages #CyberSecurityTraining #CEH #OSCP #InfosecTrain #VulnerabilityAssessment #RedTeamOps #HackingProcess 0 Comments 0 Shares 173 Views 0 Reviews
0 Comments 0 Shares 173 Views 0 Reviews - Top AWS Interview Questions & Answers | Crack Your Cloud Job!
What we cover:
Topics for Interview Practice + Use Cases
AWS Infrastructure
AWS S3
VPC
AWS Organization
AWS IAM
Route 53
RDS
Watch here: https://youtu.be/5nhvKD-wFdg?si=79XLDvE67bptgTsr
#AWSInterviewQuestions #AWS2025 #CloudComputing #InfosecTrain #AWSJobs #CloudEngineerInterview #AWSCertification #DevOpsInterview #CloudCareer #AWSInterviewPrepTop AWS Interview Questions & Answers | Crack Your Cloud Job! 📌 What we cover: ✅ Topics for Interview Practice + Use Cases ✅ AWS Infrastructure ✅ AWS S3 ✅ VPC ✅ AWS Organization ✅ AWS IAM ✅ Route 53 ✅ RDS Watch here: https://youtu.be/5nhvKD-wFdg?si=79XLDvE67bptgTsr #AWSInterviewQuestions #AWS2025 #CloudComputing #InfosecTrain #AWSJobs #CloudEngineerInterview #AWSCertification #DevOpsInterview #CloudCareer #AWSInterviewPrep 0 Comments 0 Shares 513 Views 0 Reviews
0 Comments 0 Shares 513 Views 0 Reviews - 𝐇𝐚𝐯𝐞 𝐲𝐨𝐮 𝐞𝐯𝐞𝐫 𝐚𝐬𝐤𝐞𝐝 𝐲𝐨𝐮𝐫𝐬𝐞𝐥𝐟 𝐰𝐡𝐚𝐭 𝐢𝐭 𝐭𝐚𝐤𝐞𝐬 𝐭𝐨 𝐦𝐚𝐤𝐞 𝐚 𝐜𝐨𝐦𝐩𝐚𝐧𝐲 𝐞𝐭𝐡𝐢𝐜𝐚𝐥𝐥𝐲 𝐬𝐭𝐫𝐨𝐧𝐠 𝐚𝐧𝐝 𝐫𝐞𝐚𝐝𝐲 𝐟𝐨𝐫 𝐚𝐧 𝐚𝐮𝐝𝐢𝐭?
Meet the 𝐂𝐨𝐦𝐩𝐥𝐢𝐚𝐧𝐜𝐞 𝐎𝐟𝐟𝐢𝐜𝐞𝐫 — the guardian of integrity, ensuring every process aligns with legal and regulatory standards
They’re not just box checking – they are anticipating changing regulations, working with IT & HR, revising policies, and protecting the organization from risk. In an era of constant disruption, this role is the foundation for trust, transparency and resilience.
𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞: https://www.infosectrain.com/blog/a-day-in-the-life-of-a-compliance-officer/
#Compliance #RiskManagement #CGRC #Governance #CyberSecurity #CorporateIntegrity #Audit #RegulatoryCompliance #EthicalLeadership #CareerGrowth #InfoSecTrain #Learning #DataProtection #Training #GRC𝐇𝐚𝐯𝐞 𝐲𝐨𝐮 𝐞𝐯𝐞𝐫 𝐚𝐬𝐤𝐞𝐝 𝐲𝐨𝐮𝐫𝐬𝐞𝐥𝐟 𝐰𝐡𝐚𝐭 𝐢𝐭 𝐭𝐚𝐤𝐞𝐬 𝐭𝐨 𝐦𝐚𝐤𝐞 𝐚 𝐜𝐨𝐦𝐩𝐚𝐧𝐲 𝐞𝐭𝐡𝐢𝐜𝐚𝐥𝐥𝐲 𝐬𝐭𝐫𝐨𝐧𝐠 𝐚𝐧𝐝 𝐫𝐞𝐚𝐝𝐲 𝐟𝐨𝐫 𝐚𝐧 𝐚𝐮𝐝𝐢𝐭? Meet the 𝐂𝐨𝐦𝐩𝐥𝐢𝐚𝐧𝐜𝐞 𝐎𝐟𝐟𝐢𝐜𝐞𝐫 — the guardian of integrity, ensuring every process aligns with legal and regulatory standards They’re not just box checking – they are anticipating changing regulations, working with IT & HR, revising policies, and protecting the organization from risk. In an era of constant disruption, this role is the foundation for trust, transparency and resilience. 👉 𝐑𝐞𝐚𝐝 𝐦𝐨𝐫𝐞: https://www.infosectrain.com/blog/a-day-in-the-life-of-a-compliance-officer/ #Compliance #RiskManagement #CGRC #Governance #CyberSecurity #CorporateIntegrity #Audit #RegulatoryCompliance #EthicalLeadership #CareerGrowth #InfoSecTrain #Learning #DataProtection #Training #GRCWWW.INFOSECTRAIN.COMA Day in the Life of a Compliance OfficerA Compliance Officer’s day is packed with monitoring, training, policy writing, and communication tasks that keep the organization on the right side of the law.0 Comments 0 Shares 681 Views 0 Reviews - Free Webinar Alert!
Building Business Resilience with BCMS: An ISO 22301 Implementation Guide
Date: 13 Nov (Thu)
Time: 8 PM – 9 PM (IST)
Speaker: Yasesveni
Format: Free Masterclass + Live Q&A
Register Now (Free): https://www.infosectrain.com/events/building-business-resilience-with-bcms-an-iso-22301-implementation-guide/
Key Takeaways:
• Understanding BCMS – The Foundation of Resilience
• Business Impact Analysis (BIA) in Action
• Building and Testing Continuity Plans
• Aligning BCMS with ISO 22301 and Other Frameworks
• Real-World Case Study & Lessons Learned
• Interactive Q&A Session
Why You Should Attend:
Earn a CPE Certificate
Get FREE Career Guidance & Mentorship
Learn Directly from Industry Experts
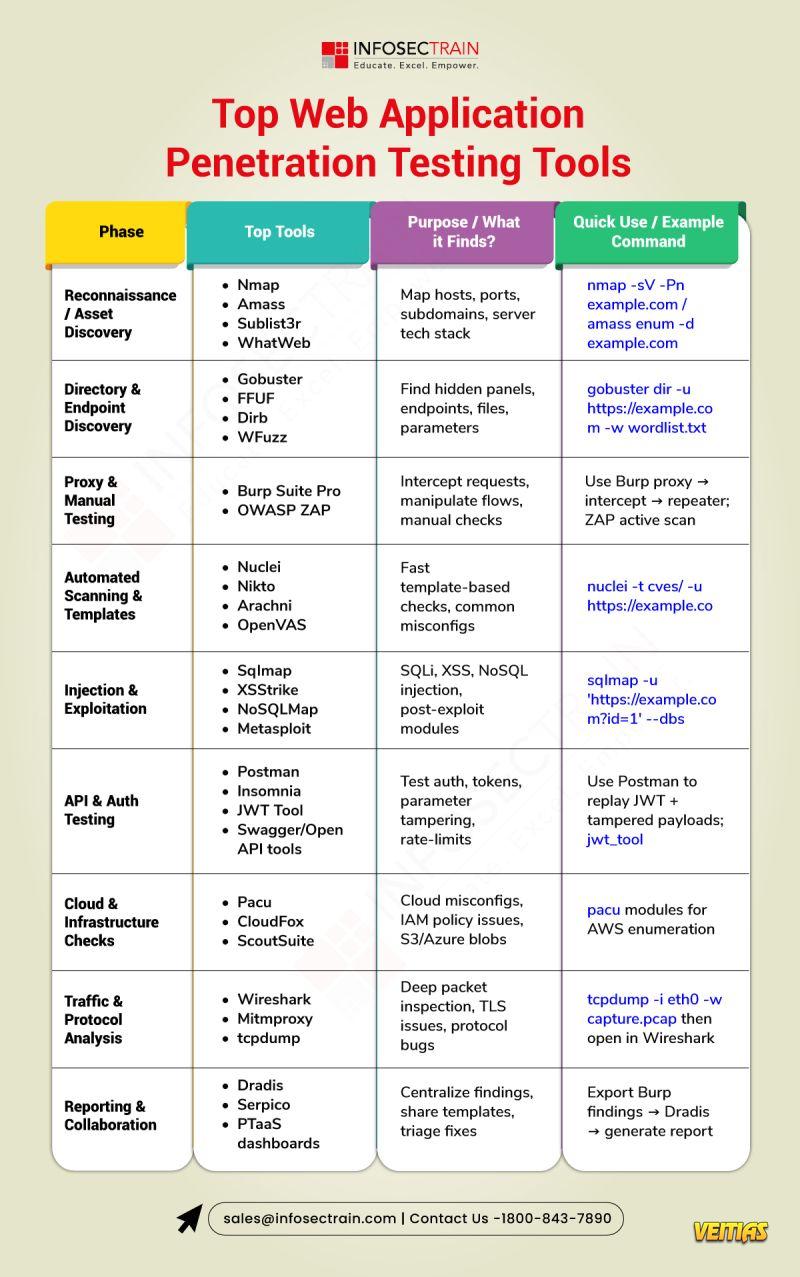
#ISO22301 #BusinessContinuity #BCMS #CyberResilience #RiskManagement #CPE #Webinar #BusinessContinuityManagement #CrisisManagement #InfoSecTrain #FreeMasterclass #BusinessResilience #Governance #ComplianceFree Webinar Alert! 💼 Building Business Resilience with BCMS: An ISO 22301 Implementation Guide 📅 Date: 13 Nov (Thu) 🕗 Time: 8 PM – 9 PM (IST) 🎤 Speaker: Yasesveni 🎓 Format: Free Masterclass + Live Q&A 👉 Register Now (Free): https://www.infosectrain.com/events/building-business-resilience-with-bcms-an-iso-22301-implementation-guide/ 💡 Key Takeaways: • Understanding BCMS – The Foundation of Resilience • Business Impact Analysis (BIA) in Action • Building and Testing Continuity Plans • Aligning BCMS with ISO 22301 and Other Frameworks • Real-World Case Study & Lessons Learned • Interactive Q&A Session ✨ Why You Should Attend: ✅ Earn a CPE Certificate ✅ Get FREE Career Guidance & Mentorship ✅ Learn Directly from Industry Experts #ISO22301 #BusinessContinuity #BCMS #CyberResilience #RiskManagement #CPE #Webinar #BusinessContinuityManagement #CrisisManagement #InfoSecTrain #FreeMasterclass #BusinessResilience #Governance #Compliance0 Comments 0 Shares 694 Views 0 Reviews - Top web application penetration testing tools help security pros find and exploit vulnerabilities quickly and reliably. Tools like Burp Suite, OWASP ZAP, sqlmap, Nmap, Metasploit, Nikto, and ffuf automate scanning, fuzzing, SQL injection discovery, and reconnaissance while providing manual testing support and powerful workflows for exploitation and verification. Using a mix of these tools—alongside careful manual analysis—lets testers simulate real attacks, prioritize findings, and provide actionable remediation for developers.Top web application penetration testing tools help security pros find and exploit vulnerabilities quickly and reliably. Tools like Burp Suite, OWASP ZAP, sqlmap, Nmap, Metasploit, Nikto, and ffuf automate scanning, fuzzing, SQL injection discovery, and reconnaissance while providing manual testing support and powerful workflows for exploitation and verification. Using a mix of these tools—alongside careful manual analysis—lets testers simulate real attacks, prioritize findings, and provide actionable remediation for developers.0 Comments 0 Shares 555 Views 0 Reviews
- Smart GIS Asset Tracking Company for Efficient Management
In today’s fast-paced world, accurate asset tracking is key to improving productivity and efficiency. Leadtech offers smart digital tracking solutions that simplify asset management and make operations more transparent. A GIS Asset Tracking Company helps organizations maintain better control by using GIS mapping and RFID technology to monitor assets in real time. This ensures that no resource goes missing or remains underused. Leadtech’s system provides live dashboards and detailed reports, allowing teams to make quick, data-based decisions. With this modern approach, organizations can easily manage assets, reduce losses, and improve accountability. It replaces manual tracking with a smarter, technology-driven method that enhances performance, saves time, and ensures smooth, efficient management across industries.
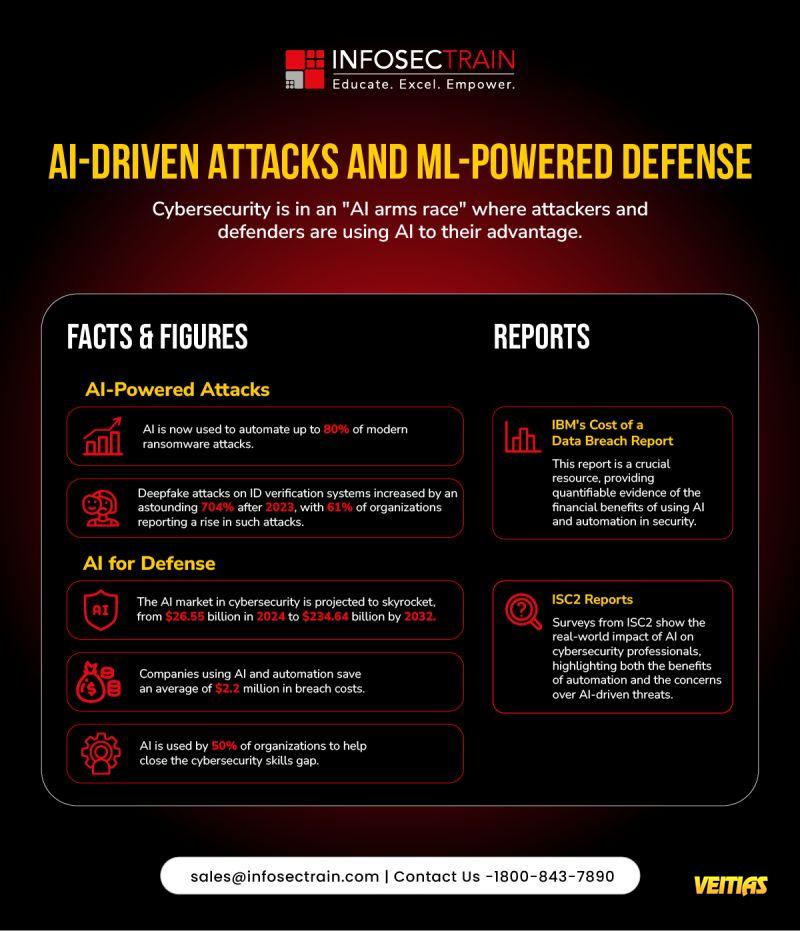
For more information, visit: https://leadtech.in/leadtech-building-intelligent-asset-tracking-systems-for-a-smarter-india/Smart GIS Asset Tracking Company for Efficient Management In today’s fast-paced world, accurate asset tracking is key to improving productivity and efficiency. Leadtech offers smart digital tracking solutions that simplify asset management and make operations more transparent. A GIS Asset Tracking Company helps organizations maintain better control by using GIS mapping and RFID technology to monitor assets in real time. This ensures that no resource goes missing or remains underused. Leadtech’s system provides live dashboards and detailed reports, allowing teams to make quick, data-based decisions. With this modern approach, organizations can easily manage assets, reduce losses, and improve accountability. It replaces manual tracking with a smarter, technology-driven method that enhances performance, saves time, and ensures smooth, efficient management across industries. For more information, visit: https://leadtech.in/leadtech-building-intelligent-asset-tracking-systems-for-a-smarter-india/LEADTECH.INBest RFID Asset Tracking Company in India – LeadtechLeadtech offers top RFID asset tracking and management solutions in India. Streamline operations with smart asset systems. Contact us today!0 Comments 0 Shares 686 Views 0 Reviews - The AI Arms Race in Cybersecurity is Real - and It's Defining 2025.
As we mark Cybersecurity Awareness Month 2025, it's clear: Al is transforming both attack and defense.
From automated ransomware to ML-powered detection, the future of cyber resilience depends on how we use Al - responsibly and strategically.
Learn More With AI-Powered Cybersecurity Training Course Online - https://www.infosectrain.com/courses/artificial-intelligence-ai-for-cyber-security-professionals-training/
#CyberSecurityAwarenessMonth #CyberSecurity #AI #MachineLearning #DataProtection #AlTech #Infosec #infosectrain #learntoriseThe AI Arms Race in Cybersecurity is Real - and It's Defining 2025. As we mark Cybersecurity Awareness Month 2025, it's clear: Al is transforming both attack and defense. From automated ransomware to ML-powered detection, the future of cyber resilience depends on how we use Al - responsibly and strategically. Learn More With AI-Powered Cybersecurity Training Course Online - https://www.infosectrain.com/courses/artificial-intelligence-ai-for-cyber-security-professionals-training/ #CyberSecurityAwarenessMonth #CyberSecurity #AI #MachineLearning #DataProtection #AlTech #Infosec #infosectrain #learntorise0 Comments 0 Shares 1380 Views 0 Reviews - Customized Power Starts Here.
At NCON Turbines, we believe that the best solutions are the ones made just for you. That’s why we offer industry-specific steam turbines designed to meet your unique energy challenges.
✔ Custom-built for your process
✔ Low maintenance, high reliability
✔ Backed by 30+ years of experience
Call us: +91 80231 51486
Visit us: http://www.nconturbines.com/Customized Power Starts Here. At NCON Turbines, we believe that the best solutions are the ones made just for you. That’s why we offer industry-specific steam turbines designed to meet your unique energy challenges. ✔ Custom-built for your process ✔ Low maintenance, high reliability ✔ Backed by 30+ years of experience ☎️ Call us: +91 80231 51486 🌐 Visit us: http://www.nconturbines.com/0 Comments 0 Shares 996 Views 0 Reviews
More Stories
Trending
Security Cameras