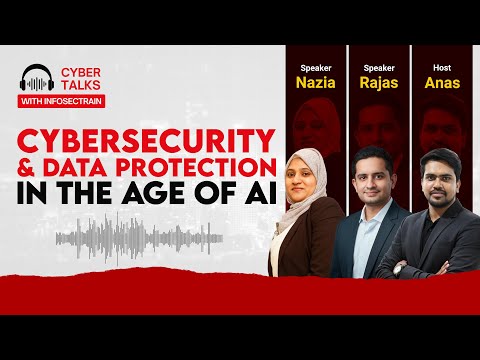
Cybersecurity & Data Protection in the Age of AI
Perfect for: CISOs tired of checkbox compliance | Legal teams drowning in AI jargon | Tech leaders balancing innovation with risk | Anyone who knows "we'll figure it out later" isn't a strategy
Watch Here: https://youtu.be/JKv6vHDn4Js?si=CGWnbwUClNE-uIj8
#CybersecurityAwarenessMonth #CyberTalks #InfosecTrain #AIRegulation #DataProtection #CyberSecurity #AICompliance #InfoSec #TechTalks #AIEthics #ZeroTrust #CISO #DataPrivacy #cyberthreats
Perfect for: CISOs tired of checkbox compliance | Legal teams drowning in AI jargon | Tech leaders balancing innovation with risk | Anyone who knows "we'll figure it out later" isn't a strategy
Watch Here: https://youtu.be/JKv6vHDn4Js?si=CGWnbwUClNE-uIj8
#CybersecurityAwarenessMonth #CyberTalks #InfosecTrain #AIRegulation #DataProtection #CyberSecurity #AICompliance #InfoSec #TechTalks #AIEthics #ZeroTrust #CISO #DataPrivacy #cyberthreats
Cybersecurity & Data Protection in the Age of AI
Perfect for: CISOs tired of checkbox compliance | Legal teams drowning in AI jargon | Tech leaders balancing innovation with risk | Anyone who knows "we'll figure it out later" isn't a strategy
Watch Here: https://youtu.be/JKv6vHDn4Js?si=CGWnbwUClNE-uIj8
#CybersecurityAwarenessMonth #CyberTalks #InfosecTrain #AIRegulation #DataProtection #CyberSecurity #AICompliance #InfoSec #TechTalks #AIEthics #ZeroTrust #CISO #DataPrivacy #cyberthreats
0 Comments
0 Shares
3358 Views
0 Reviews