𝐅𝐫𝐞𝐞 𝐌𝐚𝐬𝐭𝐞𝐫𝐜𝐥𝐚𝐬𝐬: 𝐄𝐭𝐡𝐢𝐜𝐚𝐥 𝐇𝐚𝐜𝐤𝐞𝐫 𝐌𝐢𝐧𝐢 𝐁𝐨𝐨𝐭𝐜𝐚𝐦𝐩 – 𝐅𝐚𝐬𝐭-𝐓𝐫𝐚𝐜𝐤 𝐂𝐨𝐮𝐫𝐬𝐞!
Are you ready to dive into the world of ethical hacking and cyber security? Join for an Free Masterclass designed to fast-track your journey to becoming a skilled ethical hacker!
Date: 23-26Sep (Mon – Thu)
Time: 08:00 – 10:00 PM (IST)
Speaker: Yogender
𝐅𝐫𝐞𝐞 𝐑𝐞𝐠𝐢𝐬𝐭𝐞𝐫 𝐍𝐨𝐰:
https://www.infosectrain.com/events/ethical-hacker-mini-bootcamp-fast-track-course/ Agenda for the Masterclass
Day 1:
Module 1: Introduction to Ethical Hacking
Module 2: Foot Printing and Reconnaissance
Module 3: Scanning Networks
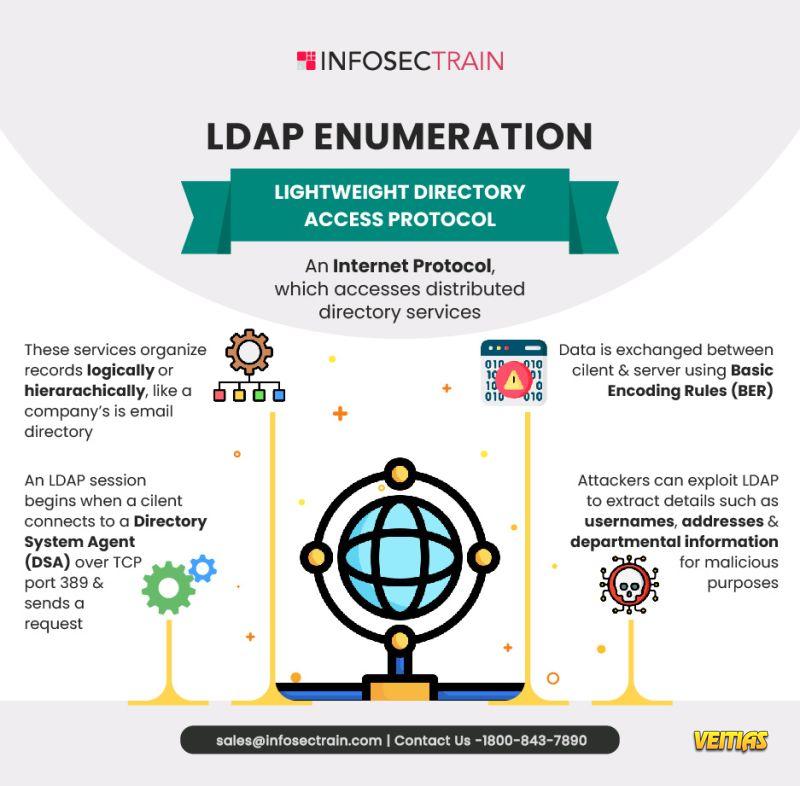
Module 4: Enumeration
Module 5: Vulnerability Analysis
Day 2:
Module 6: System Hacking
Module 7: Malware Threats
Module 8: Sniffing
Module 9: Social Engineering
Module 10: Denial of Service
Day 3:
Module 11: Session Hijacking
Module 12: Evading IDS, Firewalls, and Honeypots
Module 13: Hacking Web Servers
Module 14: Hacking Web Applications
Module 15: SQL Injections
Day 4:
Module 16: Hacking Wireless Networks
Module 17: Hacking Mobile Platforms
Module 18: IoT Hacking and OT Hacking
Module 19: Cloud Computing
Module 20: Cryptography
#EthicalHacking #CyberSecurity #InfoSec #HackerTraining #liveevent #FreeMasterclass #CyberSecurityTraining #ITCareer
#HackingBootcamp #TechSkills #SecureYourFuture #PenetrationTesting #EthicalHacker #CyberDefense #SecurityTraining #HackThePlanet #freewebinar #infosectrain #learntorise𝐅𝐫𝐞𝐞 𝐌𝐚𝐬𝐭𝐞𝐫𝐜𝐥𝐚𝐬𝐬: 𝐄𝐭𝐡𝐢𝐜𝐚𝐥 𝐇𝐚𝐜𝐤𝐞𝐫 𝐌𝐢𝐧𝐢 𝐁𝐨𝐨𝐭𝐜𝐚𝐦𝐩 – 𝐅𝐚𝐬𝐭-𝐓𝐫𝐚𝐜𝐤 𝐂𝐨𝐮𝐫𝐬𝐞!
Are you ready to dive into the world of ethical hacking and cyber security? Join for an Free Masterclass designed to fast-track your journey to becoming a skilled ethical hacker!
📅 Date: 23-26Sep (Mon – Thu) ⌚ Time: 08:00 – 10:00 PM (IST)
Speaker: Yogender
𝐅𝐫𝐞𝐞 𝐑𝐞𝐠𝐢𝐬𝐭𝐞𝐫 𝐍𝐨𝐰: https://www.infosectrain.com/events/ethical-hacker-mini-bootcamp-fast-track-course/
➡️ Agenda for the Masterclass
Day 1:
Module 1: Introduction to Ethical Hacking
Module 2: Foot Printing and Reconnaissance
Module 3: Scanning Networks
Module 4: Enumeration
Module 5: Vulnerability Analysis
Day 2:
Module 6: System Hacking
Module 7: Malware Threats
Module 8: Sniffing
Module 9: Social Engineering
Module 10: Denial of Service
Day 3:
Module 11: Session Hijacking
Module 12: Evading IDS, Firewalls, and Honeypots
Module 13: Hacking Web Servers
Module 14: Hacking Web Applications
Module 15: SQL Injections
Day 4:
Module 16: Hacking Wireless Networks
Module 17: Hacking Mobile Platforms
Module 18: IoT Hacking and OT Hacking
Module 19: Cloud Computing
Module 20: Cryptography
#EthicalHacking #CyberSecurity #InfoSec #HackerTraining #liveevent #FreeMasterclass #CyberSecurityTraining #ITCareer #HackingBootcamp #TechSkills #SecureYourFuture #PenetrationTesting #EthicalHacker #CyberDefense #SecurityTraining #HackThePlanet #freewebinar #infosectrain #learntorise