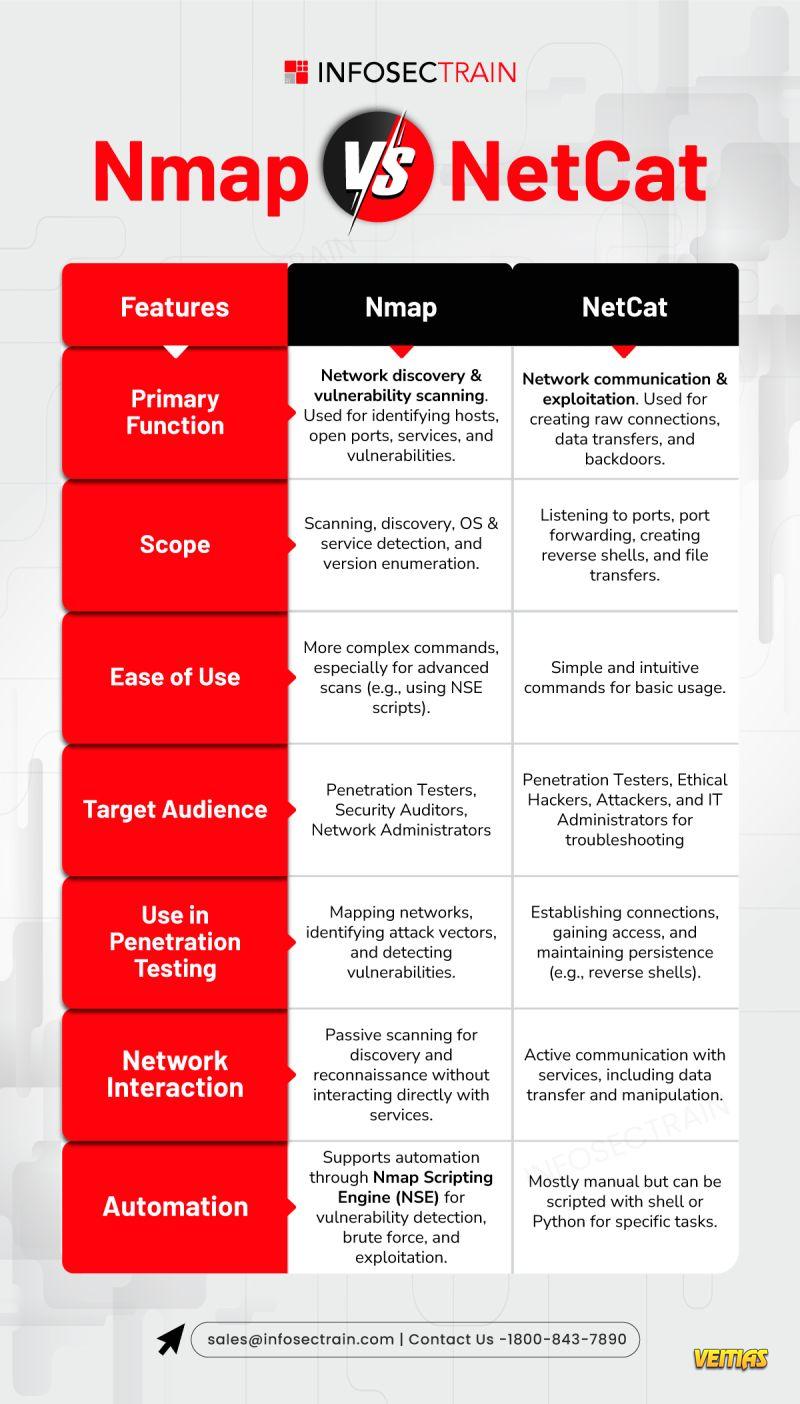
Nmap Vs NetCat
Nmap and
NetCat – two essential tools in the cybersecurity toolkit, but which one reigns supreme for your next penetration test or network audit? Let's break it down with this quick infographic comparison
Nmap 🕵♂
Primary Function: Network discovery & vulnerability scanning.
Scope: Identifying hosts, open ports, OS & service detection, version enumeration.
Target Audience: Pen Testers, Security Auditors, Admins.
Automation: Fully supports NSE scripts for automation.
Use: Discover vulnerabilities and attack vectors during network mapping.
Network Interaction: Passive, only scans without engaging services directly.
NetCat
Primary Function: Network communication & exploitation.
Scope: Port listening, creating reverse shells, file transfers, and port forwarding.
Target Audience: Pen Testers, Ethical Hackers, IT Admins.
Automation: Scriptable with shell/Python but manual by design.
Use: Establishing connections, gaining access, maintaining persistence.
Network Interaction: Active – directly communicates and manipulates services.
Key Takeaway:
Nmap is your go-to for 𝐬𝐜𝐚𝐧𝐧𝐢𝐧𝐠 𝐚𝐧𝐝 𝐯𝐮𝐥𝐧𝐞𝐫𝐚𝐛𝐢𝐥𝐢𝐭𝐲 𝐝𝐢𝐬𝐜𝐨𝐯𝐞𝐫𝐲 . Perfect for mapping out a network’s attack surface.
NetCat is a 𝐧𝐞𝐭𝐰𝐨𝐫𝐤 𝐮𝐭𝐢𝐥𝐢𝐭𝐲 that's all about 𝐜𝐨𝐦𝐦𝐮𝐧𝐢𝐜𝐚𝐭𝐢𝐨𝐧𝐬 𝐚𝐧𝐝 𝐞𝐱𝐩𝐥𝐨𝐢𝐭𝐚𝐭𝐢𝐨𝐧. If you need to 𝐜𝐫𝐞𝐚𝐭𝐞 𝐛𝐚𝐜𝐤𝐝𝐨𝐨𝐫𝐬 or transfer data, this is the tool for you.
Whether you’re #mappingnetworks or #exploitingvulnerabilities , knowing when to use each tool is key to mastering cybersecurity.
#Nmap #NetCat #CyberSecurity #EthicalHacking #NetworkScanning #PenTesting #InfoSecTools #CyberDefense #NetworkSecurity #HackingTools #RedTeaming #OffensiveSecurity #PortScanning #NetworkMonitoring #ITSecurity #SecurityTools #infosectrainNmap Vs NetCat
Nmap and 🔗 NetCat – two essential tools in the cybersecurity toolkit, but which one reigns supreme for your next penetration test or network audit? Let's break it down with this quick infographic comparison
Nmap 🕵♂
➡️ Primary Function: Network discovery & vulnerability scanning.
➡️ Scope: Identifying hosts, open ports, OS & service detection, version enumeration.
➡️ Target Audience: Pen Testers, Security Auditors, Admins.
➡️ Automation: Fully supports NSE scripts for automation.
➡️ Use: Discover vulnerabilities and attack vectors during network mapping.
➡️ Network Interaction: Passive, only scans without engaging services directly.
NetCat ⚡
➡️ Primary Function: Network communication & exploitation.
➡️ Scope: Port listening, creating reverse shells, file transfers, and port forwarding.
➡️ Target Audience: Pen Testers, Ethical Hackers, IT Admins.
➡️ Automation: Scriptable with shell/Python but manual by design.
➡️ Use: Establishing connections, gaining access, maintaining persistence.
➡️ Network Interaction: Active – directly communicates and manipulates services.
🔑 Key Takeaway:
Nmap is your go-to for 𝐬𝐜𝐚𝐧𝐧𝐢𝐧𝐠 𝐚𝐧𝐝 𝐯𝐮𝐥𝐧𝐞𝐫𝐚𝐛𝐢𝐥𝐢𝐭𝐲 𝐝𝐢𝐬𝐜𝐨𝐯𝐞𝐫𝐲 . Perfect for mapping out a network’s attack surface.
NetCat is a 𝐧𝐞𝐭𝐰𝐨𝐫𝐤 𝐮𝐭𝐢𝐥𝐢𝐭𝐲 that's all about 𝐜𝐨𝐦𝐦𝐮𝐧𝐢𝐜𝐚𝐭𝐢𝐨𝐧𝐬 𝐚𝐧𝐝 𝐞𝐱𝐩𝐥𝐨𝐢𝐭𝐚𝐭𝐢𝐨𝐧. If you need to 𝐜𝐫𝐞𝐚𝐭𝐞 𝐛𝐚𝐜𝐤𝐝𝐨𝐨𝐫𝐬 or transfer data, this is the tool for you.
🔐 Whether you’re #mappingnetworks or #exploitingvulnerabilities , knowing when to use each tool is key to mastering cybersecurity. 💻🔒
#Nmap #NetCat #CyberSecurity #EthicalHacking #NetworkScanning #PenTesting #InfoSecTools #CyberDefense #NetworkSecurity #HackingTools #RedTeaming #OffensiveSecurity #PortScanning #NetworkMonitoring #ITSecurity #SecurityTools #infosectrain