Free Masterclass on Offensive Security Masterclass – From Pen Testing to Red Teaming
Date: 14 to 16 Jan (Tue – Thu)
Time: 08:00 – 10:00 PM (IST)
Speaker: Ashish Dhyani
Free Register Now:
https://www.infosectrain.com/events/offensive-security-masterclass-from-pen-testing-to-red-teaming/ Agenda for the Masterclass
Introduction to Offensive Security
• What is Offensive Security?
• Path to Offensive Security
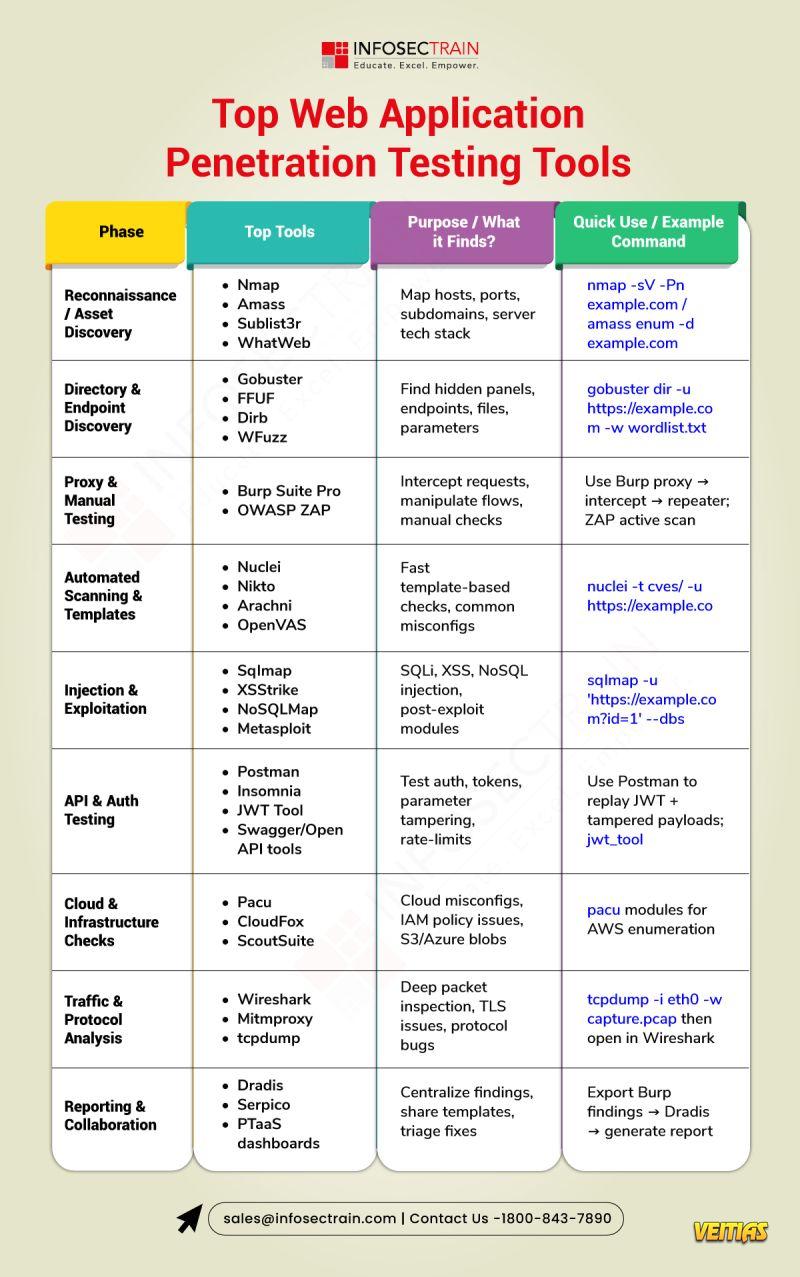
Overview of Penetration Testing Process
• What is Penetration Testing?
• Vulnerability Assessment vs Penetration Testing
• Strategies of Penetration Testing
• What can be tested? – Web, Mobile, Network, API, etc.
Introduction to Red Teaming
• What is Read Teaming?
• Why Organizations Need Red Teams?
• Red Team Attack Lifecycle (Phases)
• Red Team Infrastructure
Scanning and Exploitation
• Understanding Scanning
• Introduction to Metasploit Framework
• Understanding Scanning with tool – Practical
• Understanding Metasploit Framework – Practical
• Importance of Reporting in Red Teaming and Penetration Testing Processes
Why Attend This Masterclass
Get CPE Certificate
Learn from Industry Experts
FREE Career Guidance & Mentorship
#OffensiveSecurity #PenTesting #RedTeaming #CyberSecurity #EthicalHacking #FreeMasterclass #CyberTraining #InfoSec #RedTeamOps #SecurityMasterclass #CyberDefense #HackingTraining #EthicalHacker #CyberSecurityEducation #FreeCyberClass #EthicalHackingMasterclass
#infosectrainFree Masterclass on Offensive Security Masterclass – From Pen Testing to Red Teaming
📅 Date: 14 to 16 Jan (Tue – Thu)
⌚ Time: 08:00 – 10:00 PM (IST)
Speaker: Ashish Dhyani
Free Register Now: https://www.infosectrain.com/events/offensive-security-masterclass-from-pen-testing-to-red-teaming/
➡️ Agenda for the Masterclass
Introduction to Offensive Security
• What is Offensive Security?
• Path to Offensive Security
Overview of Penetration Testing Process
• What is Penetration Testing?
• Vulnerability Assessment vs Penetration Testing
• Strategies of Penetration Testing
• What can be tested? – Web, Mobile, Network, API, etc.
Introduction to Red Teaming
• What is Read Teaming?
• Why Organizations Need Red Teams?
• Red Team Attack Lifecycle (Phases)
• Red Team Infrastructure
Scanning and Exploitation
• Understanding Scanning
• Introduction to Metasploit Framework
• Understanding Scanning with tool – Practical
• Understanding Metasploit Framework – Practical
• Importance of Reporting in Red Teaming and Penetration Testing Processes
➡️ Why Attend This Masterclass
👉 Get CPE Certificate
👉 Learn from Industry Experts
👉 FREE Career Guidance & Mentorship
#OffensiveSecurity #PenTesting #RedTeaming #CyberSecurity #EthicalHacking #FreeMasterclass #CyberTraining #InfoSec #RedTeamOps #SecurityMasterclass #CyberDefense #HackingTraining #EthicalHacker #CyberSecurityEducation #FreeCyberClass #EthicalHackingMasterclass #infosectrain