𝐇𝐨𝐰 𝐈𝐧𝐟𝐨𝐬𝐞𝐜𝐓𝐫𝐚𝐢𝐧’𝐬 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐇𝐮𝐧𝐭𝐢𝐧𝐠 𝐚𝐧𝐝 𝐃𝐅𝐈𝐑 𝐜𝐨𝐮𝐫𝐬𝐞 𝐢𝐬 𝐃𝐢𝐟𝐟𝐞𝐫𝐞𝐧𝐭 𝐟𝐫𝐨𝐦 𝐎𝐭𝐡𝐞𝐫𝐬?
To stay ahead, organizations need professionals who can detect, investigate, and respond to sophisticated attacks. To stay ahead, organizations need professionals who can detect, investigate, and respond to sophisticated attacks. That’s where Infosec Train 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐇𝐮𝐧𝐭𝐢𝐧𝐠 & 𝐃𝐅𝐈𝐑 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 comes in a fully immersive learning experience designed for cybersecurity professionals who want to level up their operational capabilities.
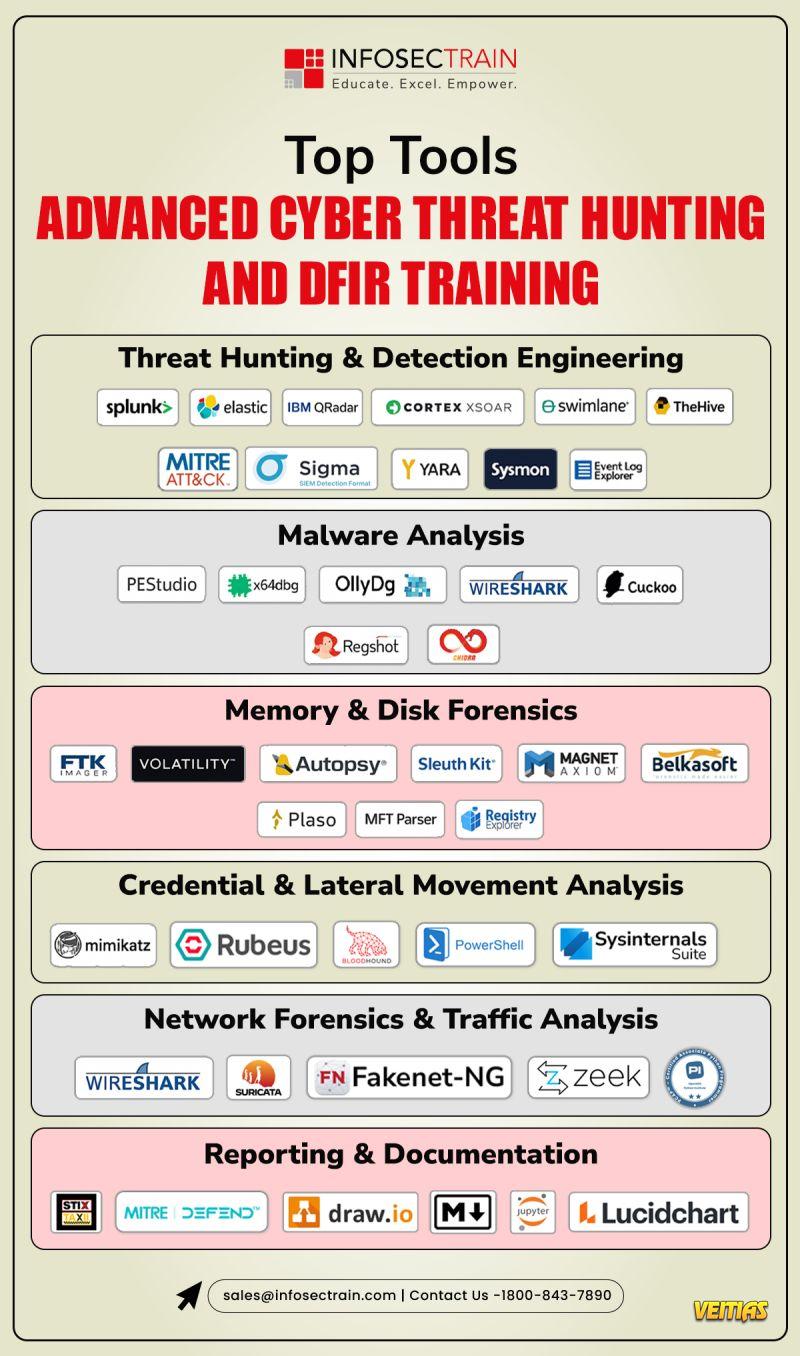
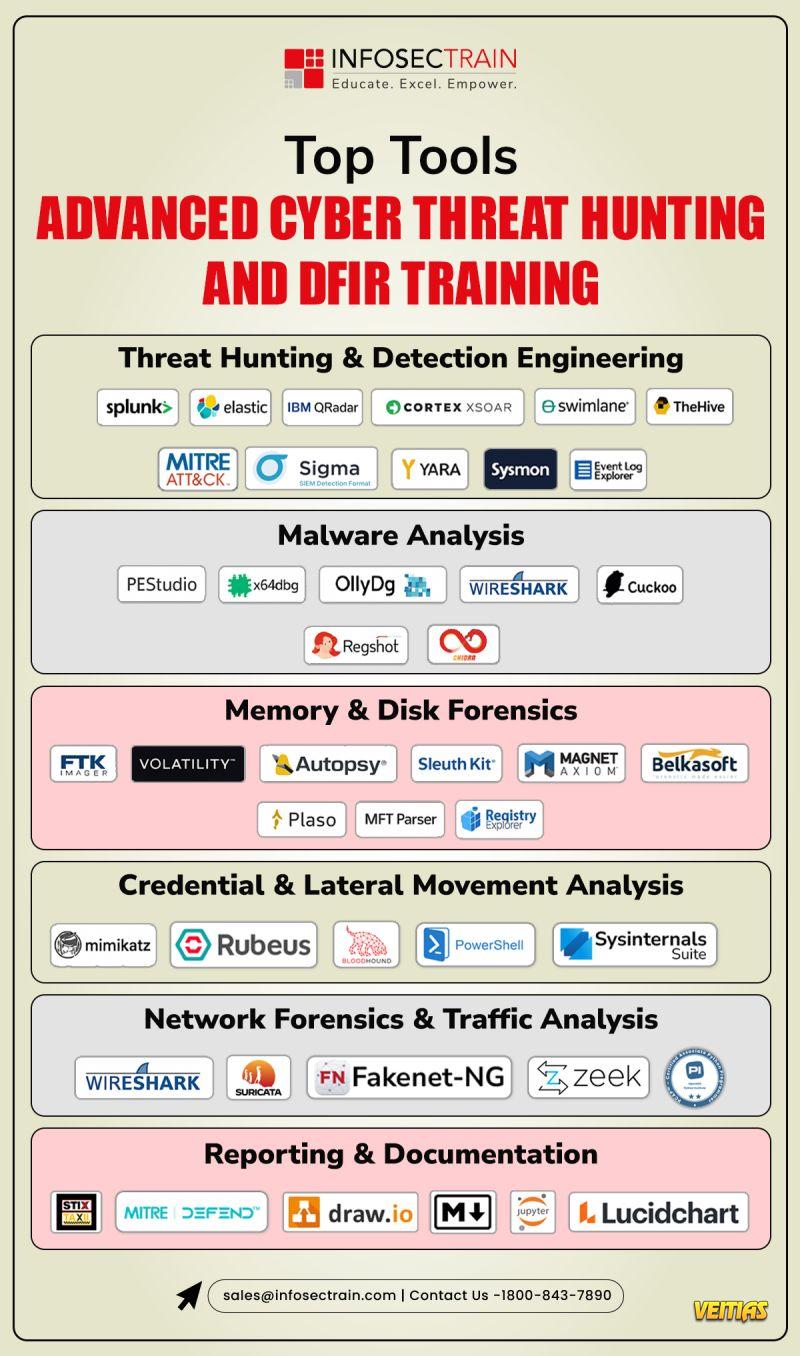
✔ 𝐈𝐧𝐝𝐮𝐬𝐭𝐫𝐲-𝐒𝐭𝐚𝐧𝐝𝐚𝐫𝐝 𝐓𝐨𝐨𝐥𝐬
Become proficient with tools trusted by global SOC teams:
• Volatility – Deep memory analysis
• YARA – Malware detection with custom rules
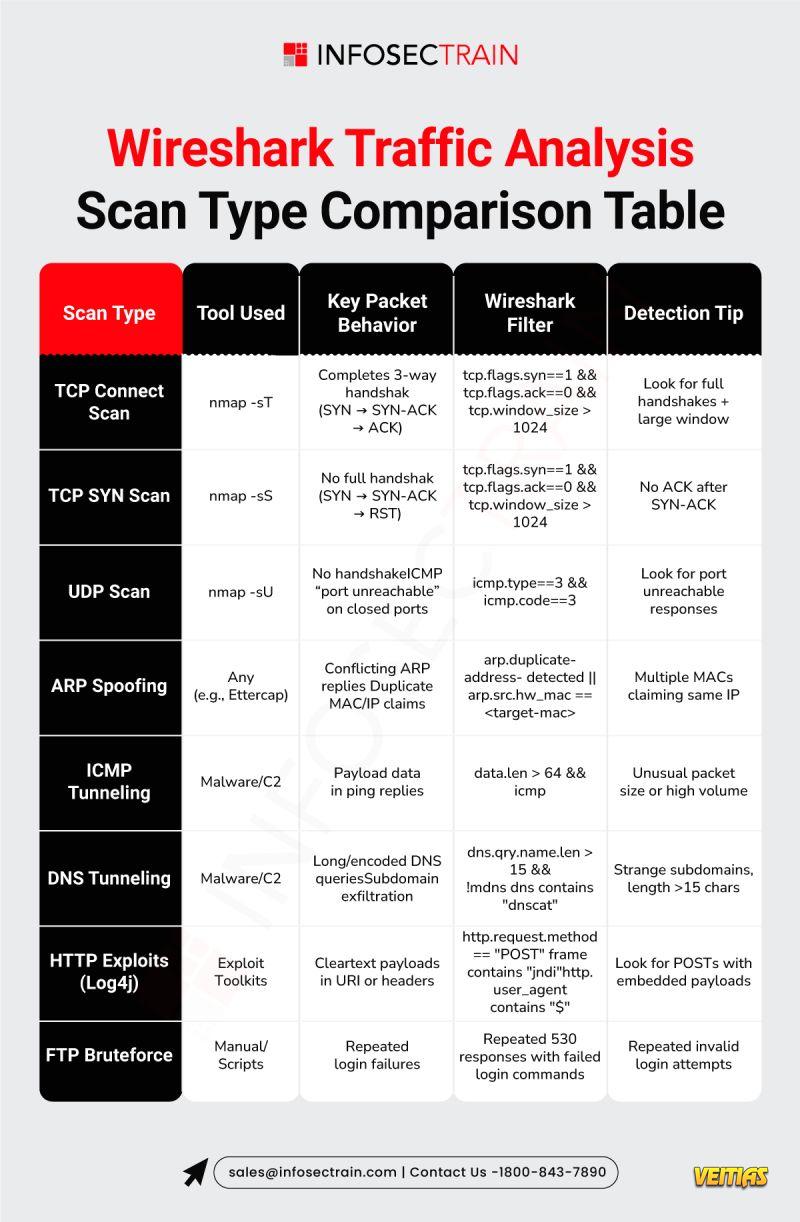
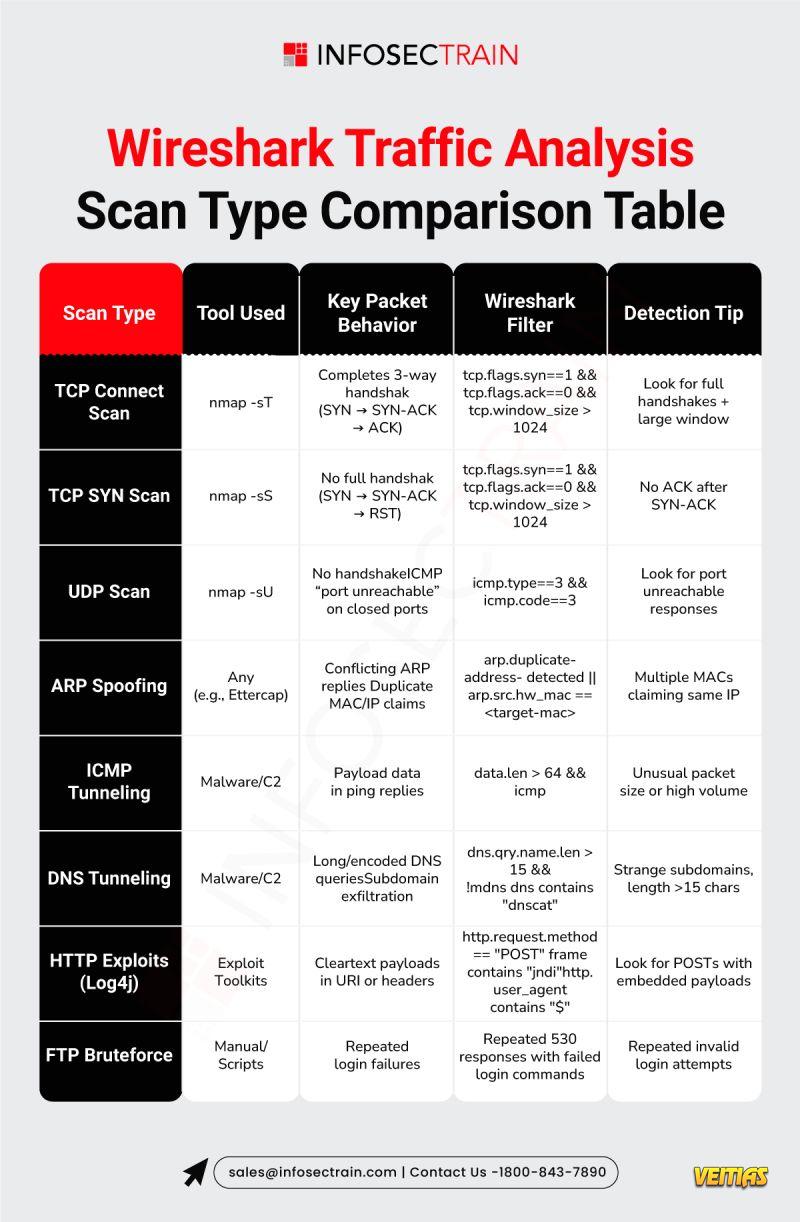
• Wireshark – Network traffic investigations
• MISP & STIX/TAXII – Threat intelligence sharing and automation
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞:https://www.infosectrain.com/blog/how-infosectrains-advanced-threat-hunting-and-dfir-course-is-different-from-others/
✔𝐖𝐡𝐲 𝐓𝐡𝐢𝐬 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 𝐌𝐚𝐭𝐭𝐞𝐫𝐬
Organizations today need cybersecurity professionals who don’t just respond they anticipate, detect, and neutralize threats proactively. This course equips you with the critical skills and operational confidence to do exactly that.
#ThreatHunting #DFIR #CybersecurityTraining #IncidentResponse #DigitalForensics #MITREATTACK #Volatility #YARA #Wireshark #SecurityOperations #BlueTeam #InfoSecTrain
To stay ahead, organizations need professionals who can detect, investigate, and respond to sophisticated attacks. To stay ahead, organizations need professionals who can detect, investigate, and respond to sophisticated attacks. That’s where Infosec Train 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐇𝐮𝐧𝐭𝐢𝐧𝐠 & 𝐃𝐅𝐈𝐑 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 comes in a fully immersive learning experience designed for cybersecurity professionals who want to level up their operational capabilities.
✔ 𝐈𝐧𝐝𝐮𝐬𝐭𝐫𝐲-𝐒𝐭𝐚𝐧𝐝𝐚𝐫𝐝 𝐓𝐨𝐨𝐥𝐬
Become proficient with tools trusted by global SOC teams:
• Volatility – Deep memory analysis
• YARA – Malware detection with custom rules
• Wireshark – Network traffic investigations
• MISP & STIX/TAXII – Threat intelligence sharing and automation
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞:https://www.infosectrain.com/blog/how-infosectrains-advanced-threat-hunting-and-dfir-course-is-different-from-others/
✔𝐖𝐡𝐲 𝐓𝐡𝐢𝐬 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 𝐌𝐚𝐭𝐭𝐞𝐫𝐬
Organizations today need cybersecurity professionals who don’t just respond they anticipate, detect, and neutralize threats proactively. This course equips you with the critical skills and operational confidence to do exactly that.
#ThreatHunting #DFIR #CybersecurityTraining #IncidentResponse #DigitalForensics #MITREATTACK #Volatility #YARA #Wireshark #SecurityOperations #BlueTeam #InfoSecTrain
𝐇𝐨𝐰 𝐈𝐧𝐟𝐨𝐬𝐞𝐜𝐓𝐫𝐚𝐢𝐧’𝐬 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐇𝐮𝐧𝐭𝐢𝐧𝐠 𝐚𝐧𝐝 𝐃𝐅𝐈𝐑 𝐜𝐨𝐮𝐫𝐬𝐞 𝐢𝐬 𝐃𝐢𝐟𝐟𝐞𝐫𝐞𝐧𝐭 𝐟𝐫𝐨𝐦 𝐎𝐭𝐡𝐞𝐫𝐬?
To stay ahead, organizations need professionals who can detect, investigate, and respond to sophisticated attacks. To stay ahead, organizations need professionals who can detect, investigate, and respond to sophisticated attacks. That’s where Infosec Train 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐇𝐮𝐧𝐭𝐢𝐧𝐠 & 𝐃𝐅𝐈𝐑 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 comes in a fully immersive learning experience designed for cybersecurity professionals who want to level up their operational capabilities.
✔ 𝐈𝐧𝐝𝐮𝐬𝐭𝐫𝐲-𝐒𝐭𝐚𝐧𝐝𝐚𝐫𝐝 𝐓𝐨𝐨𝐥𝐬
Become proficient with tools trusted by global SOC teams:
• Volatility – Deep memory analysis
• YARA – Malware detection with custom rules
• Wireshark – Network traffic investigations
• MISP & STIX/TAXII – Threat intelligence sharing and automation
👉 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞:https://www.infosectrain.com/blog/how-infosectrains-advanced-threat-hunting-and-dfir-course-is-different-from-others/
✔𝐖𝐡𝐲 𝐓𝐡𝐢𝐬 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 𝐌𝐚𝐭𝐭𝐞𝐫𝐬
Organizations today need cybersecurity professionals who don’t just respond they anticipate, detect, and neutralize threats proactively. This course equips you with the critical skills and operational confidence to do exactly that.
#ThreatHunting #DFIR #CybersecurityTraining #IncidentResponse #DigitalForensics #MITREATTACK #Volatility #YARA #Wireshark #SecurityOperations #BlueTeam #InfoSecTrain
0 Comments
0 Shares
334 Views
0 Reviews