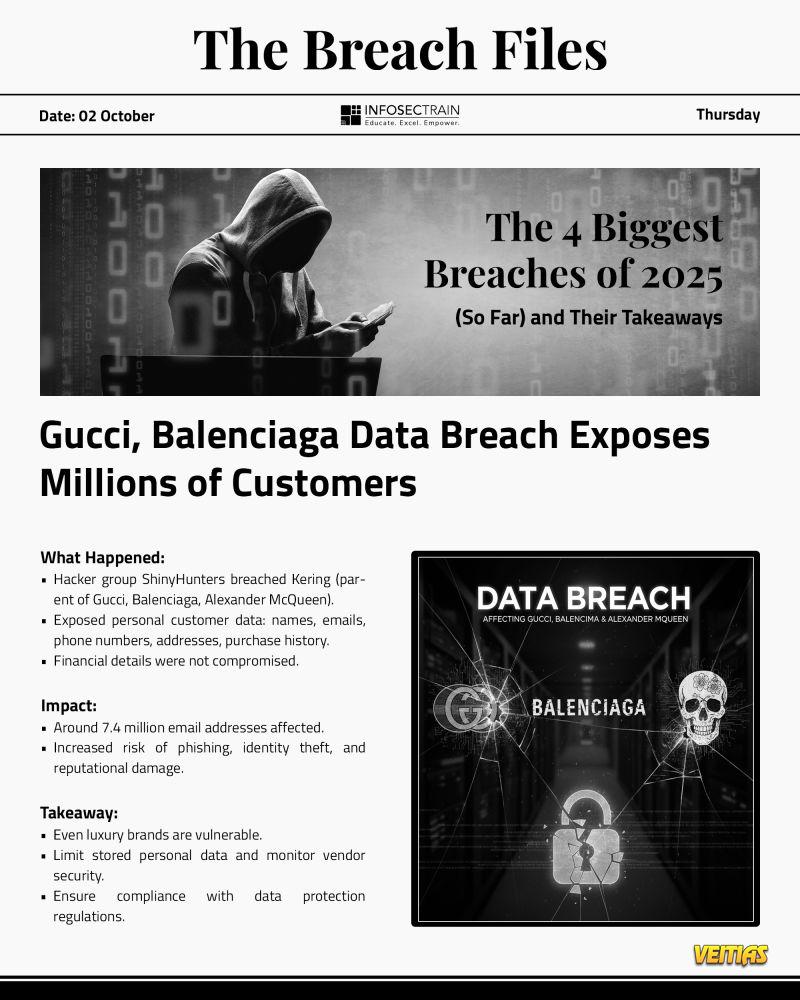
𝐓𝐡𝐞 𝐁𝐫𝐞𝐚𝐜𝐡 𝐅𝐢𝐥𝐞𝐬: 𝐇𝐢𝐠𝐡 𝐅𝐚𝐬𝐡𝐢𝐨𝐧, 𝐇𝐢𝐠𝐡𝐞𝐫 𝐑𝐢𝐬𝐤
Gucci & Balenciaga have joined the breach list of 2025.
Hacker group 𝐒𝐡𝐢𝐧𝐲𝐇𝐮𝐧𝐭𝐞𝐫𝐬 infiltrated Kering, leaking data of over 𝟕 𝐦𝐢𝐥𝐥𝐢𝐨𝐧
customers — from names to purchase history.
Luxury doesn’t mean invincible.
𝐈𝐦𝐩𝐚𝐜𝐭: More phishing. More identity theft. More reason to rethink data practices.
𝐓𝐚𝐤𝐞𝐚𝐰𝐚𝐲: Prestige needs protection. Audit your data. Strengthen vendor checks.
#InfosecTrain #TheBreachFiles #CyberAwareness #DataProtection #Gucci #Balenciaga #learntorise
Gucci & Balenciaga have joined the breach list of 2025.
Hacker group 𝐒𝐡𝐢𝐧𝐲𝐇𝐮𝐧𝐭𝐞𝐫𝐬 infiltrated Kering, leaking data of over 𝟕 𝐦𝐢𝐥𝐥𝐢𝐨𝐧
customers — from names to purchase history.
Luxury doesn’t mean invincible.
𝐈𝐦𝐩𝐚𝐜𝐭: More phishing. More identity theft. More reason to rethink data practices.
𝐓𝐚𝐤𝐞𝐚𝐰𝐚𝐲: Prestige needs protection. Audit your data. Strengthen vendor checks.
#InfosecTrain #TheBreachFiles #CyberAwareness #DataProtection #Gucci #Balenciaga #learntorise
🔥 𝐓𝐡𝐞 𝐁𝐫𝐞𝐚𝐜𝐡 𝐅𝐢𝐥𝐞𝐬: 𝐇𝐢𝐠𝐡 𝐅𝐚𝐬𝐡𝐢𝐨𝐧, 𝐇𝐢𝐠𝐡𝐞𝐫 𝐑𝐢𝐬𝐤
Gucci & Balenciaga have joined the breach list of 2025.
Hacker group 𝐒𝐡𝐢𝐧𝐲𝐇𝐮𝐧𝐭𝐞𝐫𝐬 infiltrated Kering, leaking data of over 𝟕 𝐦𝐢𝐥𝐥𝐢𝐨𝐧
customers — from names to purchase history.
Luxury doesn’t mean invincible.
⚠️ 𝐈𝐦𝐩𝐚𝐜𝐭: More phishing. More identity theft. More reason to rethink data practices.
💡 𝐓𝐚𝐤𝐞𝐚𝐰𝐚𝐲: Prestige needs protection. Audit your data. Strengthen vendor checks.
#InfosecTrain #TheBreachFiles #CyberAwareness #DataProtection #Gucci #Balenciaga #learntorise
0 Commenti
0 condivisioni
233 Views
0 Anteprima