𝐓𝐡𝐢𝐧𝐤 𝐘𝐨𝐮'𝐫𝐞 𝐒𝐚𝐟𝐞 𝐎𝐧𝐥𝐢𝐧𝐞? 𝐓𝐡𝐢𝐧𝐤 𝐀𝐠𝐚𝐢𝐧.
Every minute, someone in India loses money, data, or access to their accounts not because they’re careless, but because cybercriminals are getting smarter.
It’s time YOU get smarter too.
𝐉𝐨𝐢𝐧 Infosec Train 𝐅𝐫𝐞𝐞 𝐌𝐚𝐬𝐭𝐞𝐫𝐜𝐥𝐚𝐬𝐬:
𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐀𝐰𝐚𝐫𝐞𝐧𝐞𝐬𝐬 𝐏𝐫𝐨𝐠𝐫𝐚𝐦: 𝐇𝐨𝐰 𝐭𝐨 𝐒𝐭𝐚𝐲 𝐒𝐚𝐟𝐞 𝐎𝐧𝐥𝐢𝐧𝐞
14 Dec 2025 (Sun)
9 AM – 1 PM IST
Speaker: SANYAM (Cybersecurity Expert)
𝐑𝐞𝐠𝐢𝐬𝐭𝐞𝐫 𝐅𝐫𝐞𝐞: https://www.infosectrain.com/events/cybersecurity-awareness-program-how-to-stay-safe-online/
Agenda for the Masterclass
Module 1: India’s Top Scams & Red Flags
Module 2: Responding to Financial Fraud in Minutes
Module 3: Securing Your Digital Accounts (Gmail & Facebook)
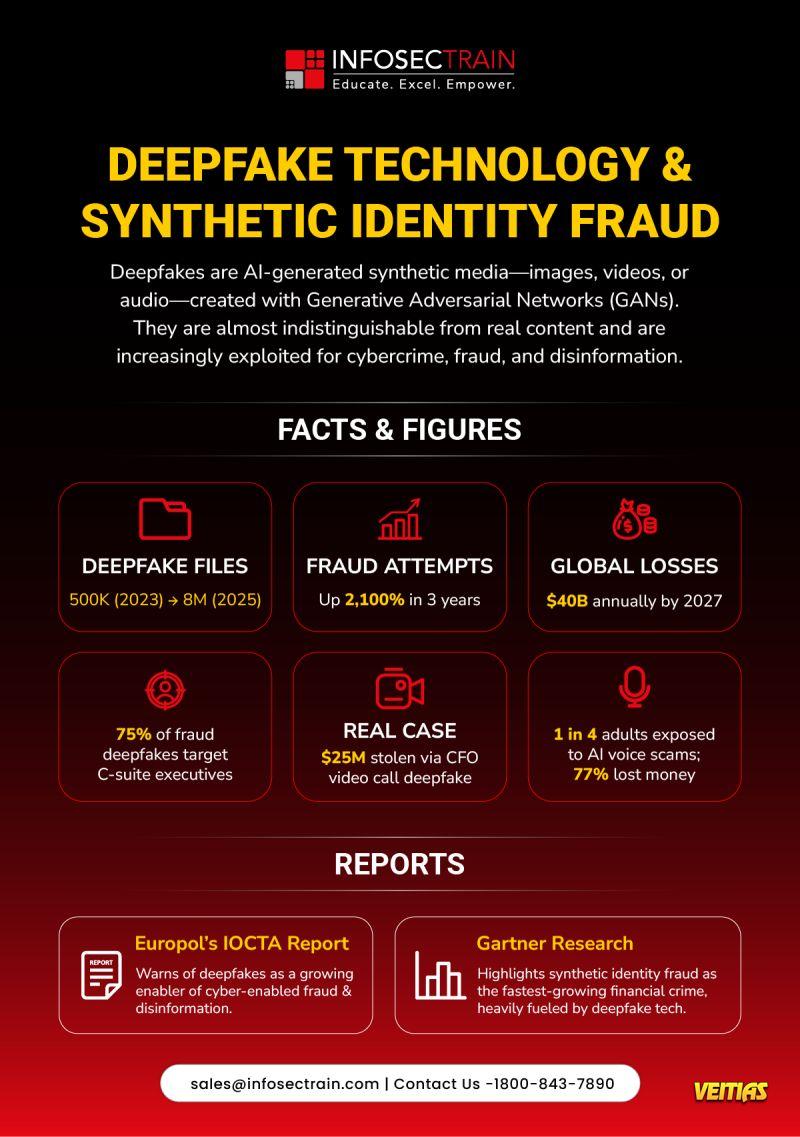
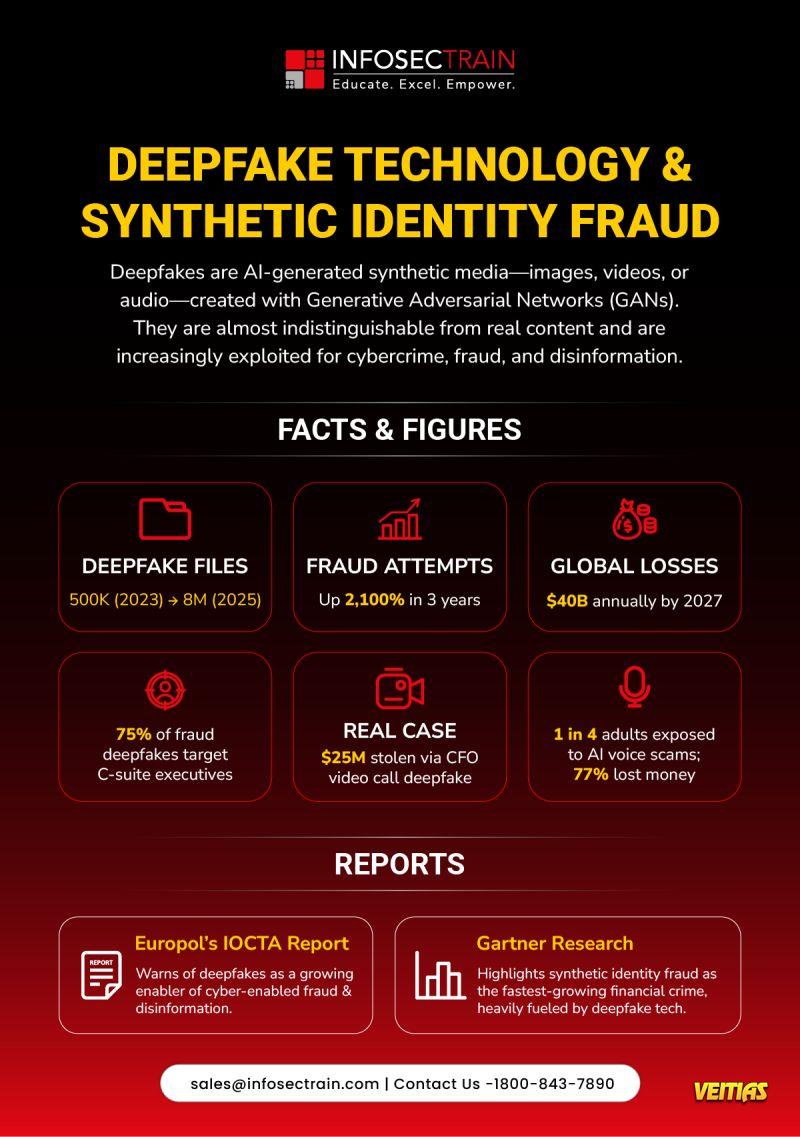
Module 4: Spotting Fakes (Emails, Domains, Deepfakes)
Module 5: Drill Hour — Simulations & Role Plays
Module 6: Wrap-Up & Action Plan
Why Attend This Masterclass
Get CPE Certificate
FREE Career Guidance & Mentorship
Learn from Industry Experts
This isn’t the typical “don’t click suspicious links” talk.
It’s a real-world, hands-on, eye-opening session that teaches you how cybercriminals actually operate and how you can beat them.
#CyberSecurityAwareness #StaySafeOnline #InfosecTrain #CyberSafety #OnlineFraudPrevention #DigitalSecurity #CyberCrimeAwareness #InfoSec #CyberHygiene
Every minute, someone in India loses money, data, or access to their accounts not because they’re careless, but because cybercriminals are getting smarter.
It’s time YOU get smarter too.
𝐉𝐨𝐢𝐧 Infosec Train 𝐅𝐫𝐞𝐞 𝐌𝐚𝐬𝐭𝐞𝐫𝐜𝐥𝐚𝐬𝐬:
𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐀𝐰𝐚𝐫𝐞𝐧𝐞𝐬𝐬 𝐏𝐫𝐨𝐠𝐫𝐚𝐦: 𝐇𝐨𝐰 𝐭𝐨 𝐒𝐭𝐚𝐲 𝐒𝐚𝐟𝐞 𝐎𝐧𝐥𝐢𝐧𝐞
14 Dec 2025 (Sun)
9 AM – 1 PM IST
Speaker: SANYAM (Cybersecurity Expert)
𝐑𝐞𝐠𝐢𝐬𝐭𝐞𝐫 𝐅𝐫𝐞𝐞: https://www.infosectrain.com/events/cybersecurity-awareness-program-how-to-stay-safe-online/
Agenda for the Masterclass
Module 1: India’s Top Scams & Red Flags
Module 2: Responding to Financial Fraud in Minutes
Module 3: Securing Your Digital Accounts (Gmail & Facebook)
Module 4: Spotting Fakes (Emails, Domains, Deepfakes)
Module 5: Drill Hour — Simulations & Role Plays
Module 6: Wrap-Up & Action Plan
Why Attend This Masterclass
Get CPE Certificate
FREE Career Guidance & Mentorship
Learn from Industry Experts
This isn’t the typical “don’t click suspicious links” talk.
It’s a real-world, hands-on, eye-opening session that teaches you how cybercriminals actually operate and how you can beat them.
#CyberSecurityAwareness #StaySafeOnline #InfosecTrain #CyberSafety #OnlineFraudPrevention #DigitalSecurity #CyberCrimeAwareness #InfoSec #CyberHygiene
🔐 𝐓𝐡𝐢𝐧𝐤 𝐘𝐨𝐮'𝐫𝐞 𝐒𝐚𝐟𝐞 𝐎𝐧𝐥𝐢𝐧𝐞? 𝐓𝐡𝐢𝐧𝐤 𝐀𝐠𝐚𝐢𝐧.
Every minute, someone in India loses money, data, or access to their accounts not because they’re careless, but because cybercriminals are getting smarter.
It’s time YOU get smarter too.
👉 𝐉𝐨𝐢𝐧 Infosec Train 𝐅𝐫𝐞𝐞 𝐌𝐚𝐬𝐭𝐞𝐫𝐜𝐥𝐚𝐬𝐬:
𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐀𝐰𝐚𝐫𝐞𝐧𝐞𝐬𝐬 𝐏𝐫𝐨𝐠𝐫𝐚𝐦: 𝐇𝐨𝐰 𝐭𝐨 𝐒𝐭𝐚𝐲 𝐒𝐚𝐟𝐞 𝐎𝐧𝐥𝐢𝐧𝐞
📅 14 Dec 2025 (Sun)
⌚ 9 AM – 1 PM IST
🎤 Speaker: SANYAM (Cybersecurity Expert)
👉 𝐑𝐞𝐠𝐢𝐬𝐭𝐞𝐫 𝐅𝐫𝐞𝐞: https://www.infosectrain.com/events/cybersecurity-awareness-program-how-to-stay-safe-online/
➡️Agenda for the Masterclass
✅ Module 1: India’s Top Scams & Red Flags
✅ Module 2: Responding to Financial Fraud in Minutes
✅ Module 3: Securing Your Digital Accounts (Gmail & Facebook)
✅ Module 4: Spotting Fakes (Emails, Domains, Deepfakes)
✅ Module 5: Drill Hour — Simulations & Role Plays
✅ Module 6: Wrap-Up & Action Plan
➡️Why Attend This Masterclass
👉Get CPE Certificate
👉FREE Career Guidance & Mentorship
👉Learn from Industry Experts
✅ This isn’t the typical “don’t click suspicious links” talk.
It’s a real-world, hands-on, eye-opening session that teaches you how cybercriminals actually operate and how you can beat them.
#CyberSecurityAwareness #StaySafeOnline #InfosecTrain #CyberSafety #OnlineFraudPrevention #DigitalSecurity #CyberCrimeAwareness #InfoSec #CyberHygiene
0 Comments
0 Shares
4266 Views
0 Reviews