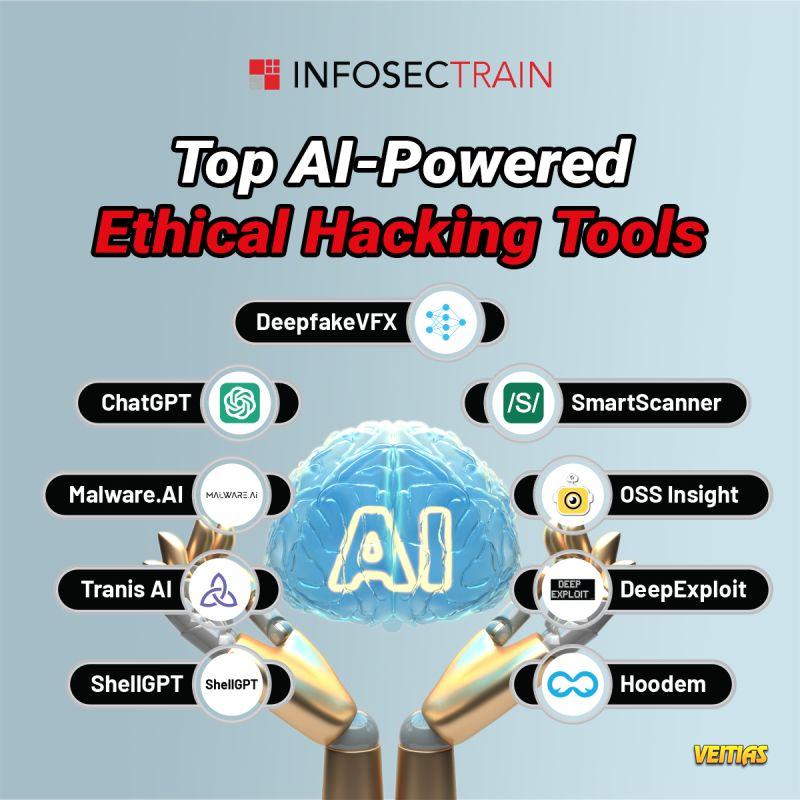
𝐓𝐨𝐩 𝐀𝐈-𝐏𝐨𝐰𝐞𝐫𝐞𝐝 𝐄𝐭𝐡𝐢𝐜𝐚𝐥 𝐇𝐚𝐜𝐤𝐢𝐧𝐠 𝐓𝐨𝐨𝐥𝐬
1. ShellGPT
- Automates shell commands for efficient task execution.
2. Tranis AI
- Analyzes traffic patterns for vulnerability detection.
3. Malware.AI
- Identifies and mitigates malware threats using AI algorithms.
4. ChatGPT
- Assists with scripting and generating security content.
5. DeepfakeVFX
- Detects and analyzes deepfake content for security assessments.
6. SmartScanner
- Performs comprehensive scans for security weaknesses.
7. OSS Insight
- Provides open-source intelligence for threat analysis.
8. DeepExploit
- Automates penetration testing and vulnerability exploitation.
9. Hoodem
- Facilitates threat hunting and analysis in real-time.
Explore these tools to enhance your ethical hacking efforts and stay ahead of cyber threats!
Explore these tools to enhance your ethical hacking efforts and stay ahead of cyber threats!
Check out: https://www.infosectrain.com/courses/certified-ethical-hacker-ceh-training/
#AIEthicalHacking #EthicalHackingTools #AIPoweredTools #CyberSecurity #PenetrationTesting #AIinCyberSecurity #ThreatDetection #CyberResilience #InfoSec #CyberRiskManagement #infosectrain #learntorise
1. ShellGPT
- Automates shell commands for efficient task execution.
2. Tranis AI
- Analyzes traffic patterns for vulnerability detection.
3. Malware.AI
- Identifies and mitigates malware threats using AI algorithms.
4. ChatGPT
- Assists with scripting and generating security content.
5. DeepfakeVFX
- Detects and analyzes deepfake content for security assessments.
6. SmartScanner
- Performs comprehensive scans for security weaknesses.
7. OSS Insight
- Provides open-source intelligence for threat analysis.
8. DeepExploit
- Automates penetration testing and vulnerability exploitation.
9. Hoodem
- Facilitates threat hunting and analysis in real-time.
Explore these tools to enhance your ethical hacking efforts and stay ahead of cyber threats!
Explore these tools to enhance your ethical hacking efforts and stay ahead of cyber threats!
Check out: https://www.infosectrain.com/courses/certified-ethical-hacker-ceh-training/
#AIEthicalHacking #EthicalHackingTools #AIPoweredTools #CyberSecurity #PenetrationTesting #AIinCyberSecurity #ThreatDetection #CyberResilience #InfoSec #CyberRiskManagement #infosectrain #learntorise
🛡️ 𝐓𝐨𝐩 𝐀𝐈-𝐏𝐨𝐰𝐞𝐫𝐞𝐝 𝐄𝐭𝐡𝐢𝐜𝐚𝐥 𝐇𝐚𝐜𝐤𝐢𝐧𝐠 𝐓𝐨𝐨𝐥𝐬 🛡️
1. ShellGPT
- Automates shell commands for efficient task execution.
2. Tranis AI
- Analyzes traffic patterns for vulnerability detection.
3. Malware.AI
- Identifies and mitigates malware threats using AI algorithms.
4. ChatGPT
- Assists with scripting and generating security content.
5. DeepfakeVFX
- Detects and analyzes deepfake content for security assessments.
6. SmartScanner
- Performs comprehensive scans for security weaknesses.
7. OSS Insight
- Provides open-source intelligence for threat analysis.
8. DeepExploit
- Automates penetration testing and vulnerability exploitation.
9. Hoodem
- Facilitates threat hunting and analysis in real-time.
Explore these tools to enhance your ethical hacking efforts and stay ahead of cyber threats! 🔐
Explore these tools to enhance your ethical hacking efforts and stay ahead of cyber threats! 🔐
Check out: https://www.infosectrain.com/courses/certified-ethical-hacker-ceh-training/
#AIEthicalHacking #EthicalHackingTools #AIPoweredTools #CyberSecurity #PenetrationTesting #AIinCyberSecurity #ThreatDetection #CyberResilience #InfoSec #CyberRiskManagement #infosectrain #learntorise
0 Commentarii
0 Distribuiri
13609 Views
0 previzualizare