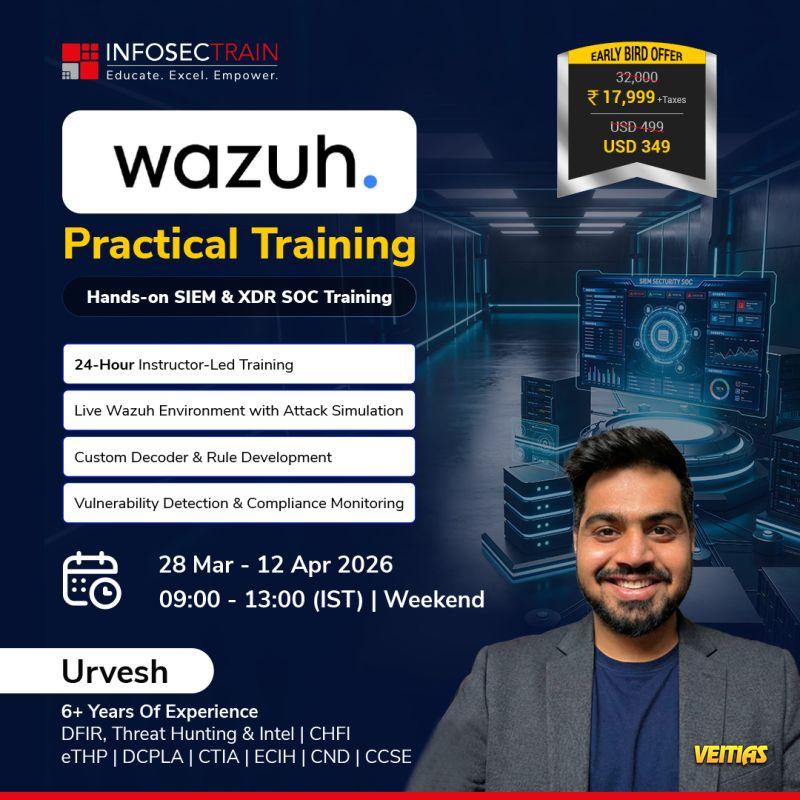
Move beyond dashboards and alerts. InfosecTrain’s 𝙒𝙖𝙯𝙪𝙝 𝙋𝙧𝙖𝙘𝙩𝙞𝙘𝙖𝙡 𝙏𝙧𝙖𝙞𝙣𝙞𝙣𝙜 is a hands-on, real SOC-focused program designed to help you build, detect, and respond to threats using a live Wazuh environment.
This training is built for professionals who want practical SOC experience, not just tool familiarity.
Led by Urvesh Thakkar (6+ years of experience in DFIR & Threat Hunting), the course focuses on real attack simulations, rule creation, and compliance monitoring - just like a production SOC.
𝟮𝟴 𝗠𝗮𝗿 – 𝟭𝟮 𝗔𝗽𝗿 𝟮𝟬𝟮𝟲
𝟬𝟵:𝟬𝟬 – 𝟭𝟯:𝟬𝟬 (𝗜𝗦𝗧) | 𝗪𝗲𝗲𝗸𝗲𝗻𝗱𝘀
𝗪𝗵𝗮𝘁 𝘆𝗼𝘂’𝗹𝗹 𝗴𝗮𝗶𝗻:
24-hour instructor-led, hands-on training
Live Wazuh lab with attack simulations
Custom decoder & rule development
Vulnerability detection & compliance monitoring
Practical exposure to 𝗦𝗜𝗘𝗠 & 𝗫𝗗𝗥 operations
This training is built for professionals who want practical SOC experience, not just tool familiarity.
Led by Urvesh Thakkar (6+ years of experience in DFIR & Threat Hunting), the course focuses on real attack simulations, rule creation, and compliance monitoring - just like a production SOC.
𝟮𝟴 𝗠𝗮𝗿 – 𝟭𝟮 𝗔𝗽𝗿 𝟮𝟬𝟮𝟲
𝟬𝟵:𝟬𝟬 – 𝟭𝟯:𝟬𝟬 (𝗜𝗦𝗧) | 𝗪𝗲𝗲𝗸𝗲𝗻𝗱𝘀
𝗪𝗵𝗮𝘁 𝘆𝗼𝘂’𝗹𝗹 𝗴𝗮𝗶𝗻:
24-hour instructor-led, hands-on training
Live Wazuh lab with attack simulations
Custom decoder & rule development
Vulnerability detection & compliance monitoring
Practical exposure to 𝗦𝗜𝗘𝗠 & 𝗫𝗗𝗥 operations
Move beyond dashboards and alerts. InfosecTrain’s 𝙒𝙖𝙯𝙪𝙝 𝙋𝙧𝙖𝙘𝙩𝙞𝙘𝙖𝙡 𝙏𝙧𝙖𝙞𝙣𝙞𝙣𝙜 is a hands-on, real SOC-focused program designed to help you build, detect, and respond to threats using a live Wazuh environment.
This training is built for professionals who want practical SOC experience, not just tool familiarity.
Led by Urvesh Thakkar (6+ years of experience in DFIR & Threat Hunting), the course focuses on real attack simulations, rule creation, and compliance monitoring - just like a production SOC.
📅 𝟮𝟴 𝗠𝗮𝗿 – 𝟭𝟮 𝗔𝗽𝗿 𝟮𝟬𝟮𝟲
🕘 𝟬𝟵:𝟬𝟬 – 𝟭𝟯:𝟬𝟬 (𝗜𝗦𝗧) | 𝗪𝗲𝗲𝗸𝗲𝗻𝗱𝘀
✨ 𝗪𝗵𝗮𝘁 𝘆𝗼𝘂’𝗹𝗹 𝗴𝗮𝗶𝗻:
👉 24-hour instructor-led, hands-on training
👉 Live Wazuh lab with attack simulations
👉 Custom decoder & rule development
👉 Vulnerability detection & compliance monitoring
👉 Practical exposure to 𝗦𝗜𝗘𝗠 & 𝗫𝗗𝗥 operations
0 Commentarios
0 Acciones
116 Views
0 Vista previa