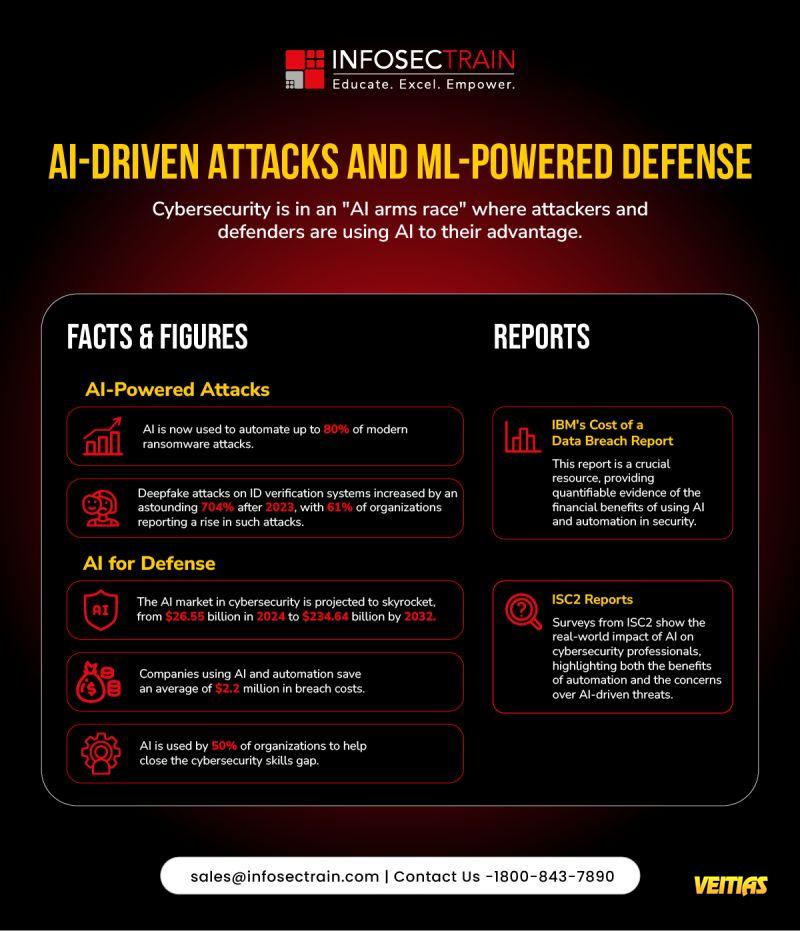
The AI Arms Race in Cybersecurity is Real - and It's Defining 2025.
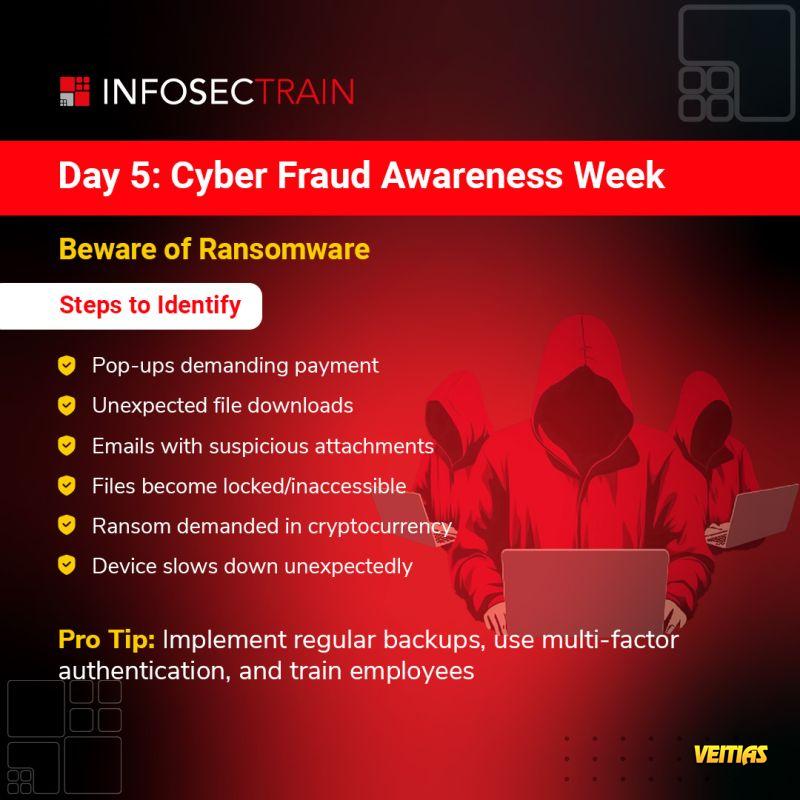
As we mark Cybersecurity Awareness Month 2025, it's clear: Al is transforming both attack and defense.
From automated ransomware to ML-powered detection, the future of cyber resilience depends on how we use Al - responsibly and strategically.
Learn More With AI-Powered Cybersecurity Training Course Online - https://www.infosectrain.com/courses/artificial-intelligence-ai-for-cyber-security-professionals-training/
#CyberSecurityAwarenessMonth #CyberSecurity #AI #MachineLearning #DataProtection #AlTech #Infosec #infosectrain #learntorise
As we mark Cybersecurity Awareness Month 2025, it's clear: Al is transforming both attack and defense.
From automated ransomware to ML-powered detection, the future of cyber resilience depends on how we use Al - responsibly and strategically.
Learn More With AI-Powered Cybersecurity Training Course Online - https://www.infosectrain.com/courses/artificial-intelligence-ai-for-cyber-security-professionals-training/
#CyberSecurityAwarenessMonth #CyberSecurity #AI #MachineLearning #DataProtection #AlTech #Infosec #infosectrain #learntorise
The AI Arms Race in Cybersecurity is Real - and It's Defining 2025.
As we mark Cybersecurity Awareness Month 2025, it's clear: Al is transforming both attack and defense.
From automated ransomware to ML-powered detection, the future of cyber resilience depends on how we use Al - responsibly and strategically.
Learn More With AI-Powered Cybersecurity Training Course Online - https://www.infosectrain.com/courses/artificial-intelligence-ai-for-cyber-security-professionals-training/
#CyberSecurityAwarenessMonth #CyberSecurity #AI #MachineLearning #DataProtection #AlTech #Infosec #infosectrain #learntorise
0 Yorumlar
0 hisse senetleri
5935 Views
0 önizleme