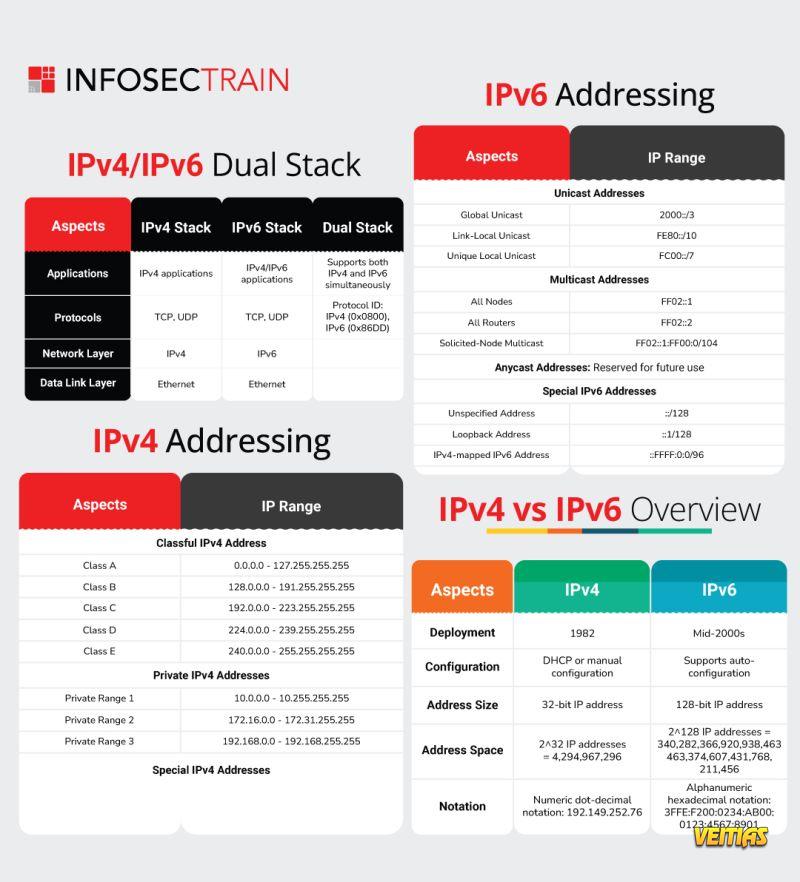
IPv4 vs. IPv6 represents the evolution of internet addressing. IPv4 (Internet Protocol version 4) uses a 32-bit address system, allowing around 4.3 billion unique addresses, which are now nearly exhausted due to the rapid growth of internet-connected devices. IPv6 (Internet Protocol version 6), on the other hand, uses a 128-bit address system, providing an almost limitless number of unique IP addresses. Besides expanded address space, IPv6 offers improved security, faster routing, and more efficient network management, making it the future standard for global internet communication.
IPv4 vs. IPv6 represents the evolution of internet addressing. IPv4 (Internet Protocol version 4) uses a 32-bit address system, allowing around 4.3 billion unique addresses, which are now nearly exhausted due to the rapid growth of internet-connected devices. IPv6 (Internet Protocol version 6), on the other hand, uses a 128-bit address system, providing an almost limitless number of unique IP addresses. Besides expanded address space, IPv6 offers improved security, faster routing, and more efficient network management, making it the future standard for global internet communication.
0 Комментарии
0 Поделились
624 Просмотры
0 предпросмотр