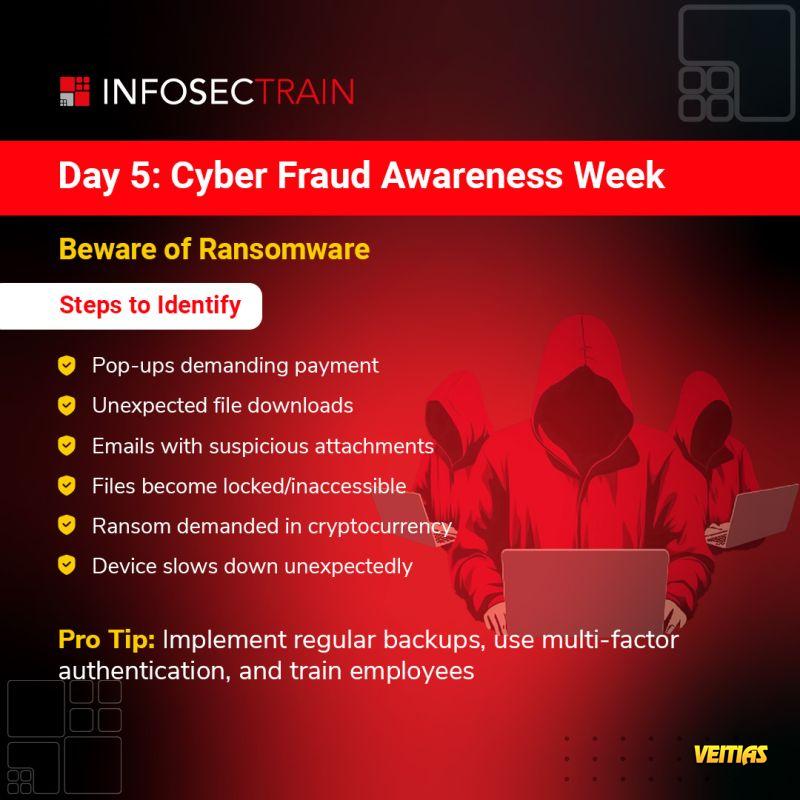
The Canvas of Cybersecurity represents a vast and dynamic landscape encompassing various strategies, technologies, and best practices aimed at protecting digital assets. It includes network security, endpoint protection, cloud security, data privacy, risk management, and compliance frameworks that organizations must implement to safeguard against cyber threats. With the rise of AI-driven cyberattacks, ransomware, and phishing schemes, cybersecurity professionals must continuously adapt by leveraging threat intelligence, security analytics, and incident response strategies. Cybersecurity is not just about deploying firewalls or antivirus solutions—it requires a holistic approach that integrates secure coding practices, zero-trust architecture, employee awareness training, and continuous monitoring.
The Canvas of Cybersecurity represents a vast and dynamic landscape encompassing various strategies, technologies, and best practices aimed at protecting digital assets. It includes network security, endpoint protection, cloud security, data privacy, risk management, and compliance frameworks that organizations must implement to safeguard against cyber threats. With the rise of AI-driven cyberattacks, ransomware, and phishing schemes, cybersecurity professionals must continuously adapt by leveraging threat intelligence, security analytics, and incident response strategies. Cybersecurity is not just about deploying firewalls or antivirus solutions—it requires a holistic approach that integrates secure coding practices, zero-trust architecture, employee awareness training, and continuous monitoring.
0 Comments
0 Shares
8105 Views
0 Reviews