𝐄𝐯𝐞𝐫 𝐭𝐡𝐨𝐮𝐠𝐡𝐭 𝐚𝐛𝐨𝐮𝐭 𝐡𝐨𝐰 𝐞𝐭𝐡𝐢𝐜𝐚𝐥 𝐡𝐚𝐜𝐤𝐞𝐫𝐬 𝐝𝐢𝐬𝐜𝐨𝐯𝐞𝐫 𝐬𝐞𝐜𝐫𝐞𝐭 𝐚𝐝𝐦𝐢𝐧 𝐩𝐚𝐧𝐞𝐥𝐬 𝐚𝐧𝐝 𝐡𝐢𝐝𝐝𝐞𝐧 𝐟𝐢𝐥𝐞𝐬 𝐢𝐧 𝐰𝐞𝐛𝐬𝐢𝐭𝐞𝐬?
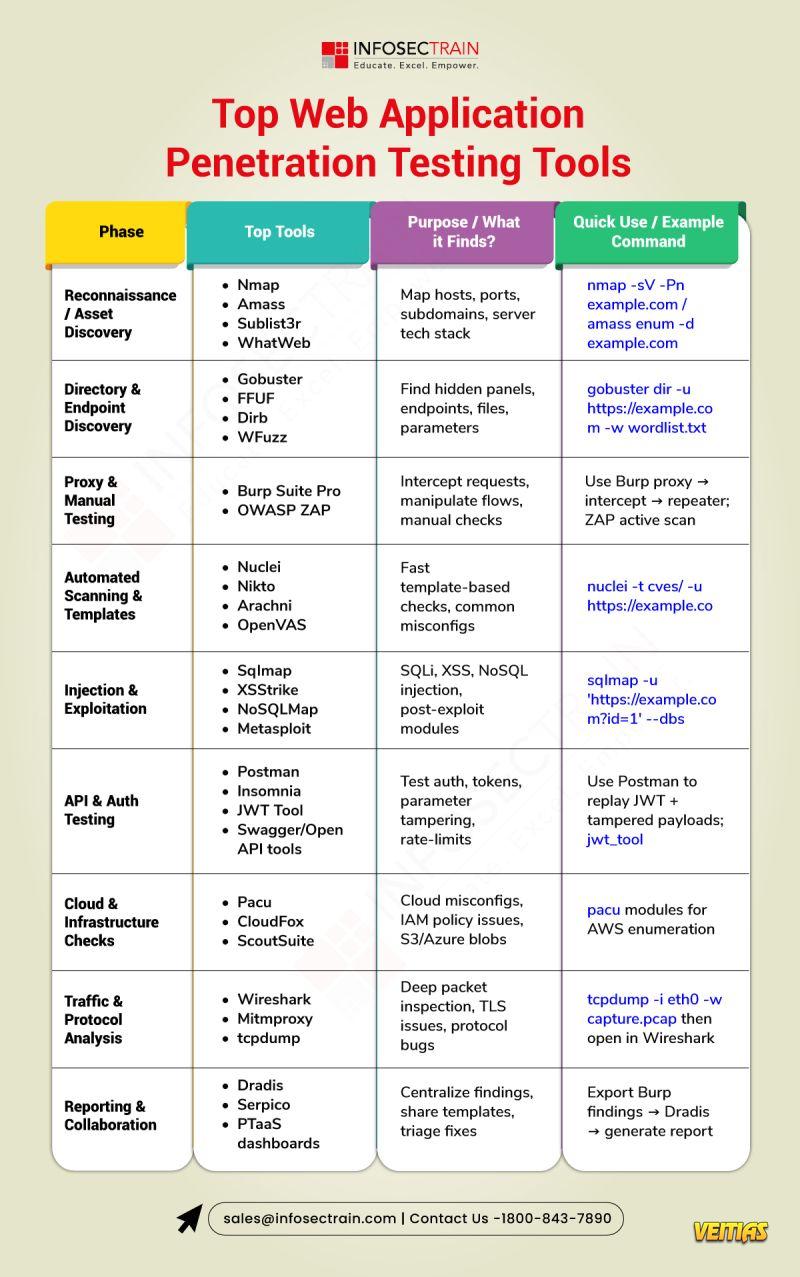
Looking for hidden doors in a website ethically and effectively? 𝐅𝐅𝐔𝐅 (𝐅𝐚𝐬𝐭 𝐖𝐞𝐛 𝐅𝐮𝐳𝐳𝐞𝐫) 𝐢𝐬 𝐚 𝐩𝐨𝐩𝐮𝐥𝐚𝐫 𝐭𝐨𝐨𝐥 𝐟𝐨𝐫 𝐩𝐞𝐧𝐞𝐭𝐫𝐚𝐭𝐢𝐨𝐧 𝐭𝐞𝐬𝐭𝐞𝐫𝐬 𝐚𝐧𝐝 𝐛𝐮𝐠 𝐡𝐮𝐧𝐭𝐞𝐫𝐬 that can be used to discover hidden directories, left behind files, and web vulnerabilities.
𝐇𝐨𝐰 𝐈𝐭 𝐖𝐨𝐫𝐤𝐬:
1⃣ FFUF takes words from a wordlist
2⃣ Injects them into URLs
3⃣Watches how the website responds
𝐅𝐅𝐔𝐅 𝐡𝐞𝐥𝐩𝐬 𝐞𝐭𝐡𝐢𝐜𝐚𝐥 𝐡𝐚𝐜𝐤𝐞𝐫𝐬:
Find admin panels
Discover exposed files
Identify misconfigurations
Strengthen website security before attackers strike
𝐅𝐅𝐔𝐅 𝐥𝐞𝐭𝐬 𝐲𝐨𝐮 𝐫𝐞𝐟𝐢𝐧𝐞 𝐲𝐨𝐮𝐫 𝐬𝐜𝐚𝐧 𝐰𝐢𝐭𝐡:
1⃣Filters for HTTP status codes
2⃣File extension targeting
3⃣Super-fast scanning for modern web apps
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/directory-brute-forcing-using-ffuf/
Want to get hands-on with FFUF and real-world penetration testing? Join Infosec Train 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐏𝐞𝐧𝐞𝐭𝐫𝐚𝐭𝐢𝐨𝐧 𝐓𝐞𝐬𝐭𝐢𝐧𝐠 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 . Learn how pros find vulnerabilities before attackers do.
#FFUF #PenTesting #CyberSecurity #EthicalHacking #InfoSecTrain #BugBounty #CyberAwareness
Looking for hidden doors in a website ethically and effectively? 𝐅𝐅𝐔𝐅 (𝐅𝐚𝐬𝐭 𝐖𝐞𝐛 𝐅𝐮𝐳𝐳𝐞𝐫) 𝐢𝐬 𝐚 𝐩𝐨𝐩𝐮𝐥𝐚𝐫 𝐭𝐨𝐨𝐥 𝐟𝐨𝐫 𝐩𝐞𝐧𝐞𝐭𝐫𝐚𝐭𝐢𝐨𝐧 𝐭𝐞𝐬𝐭𝐞𝐫𝐬 𝐚𝐧𝐝 𝐛𝐮𝐠 𝐡𝐮𝐧𝐭𝐞𝐫𝐬 that can be used to discover hidden directories, left behind files, and web vulnerabilities.
𝐇𝐨𝐰 𝐈𝐭 𝐖𝐨𝐫𝐤𝐬:
1⃣ FFUF takes words from a wordlist
2⃣ Injects them into URLs
3⃣Watches how the website responds
𝐅𝐅𝐔𝐅 𝐡𝐞𝐥𝐩𝐬 𝐞𝐭𝐡𝐢𝐜𝐚𝐥 𝐡𝐚𝐜𝐤𝐞𝐫𝐬:
Find admin panels
Discover exposed files
Identify misconfigurations
Strengthen website security before attackers strike
𝐅𝐅𝐔𝐅 𝐥𝐞𝐭𝐬 𝐲𝐨𝐮 𝐫𝐞𝐟𝐢𝐧𝐞 𝐲𝐨𝐮𝐫 𝐬𝐜𝐚𝐧 𝐰𝐢𝐭𝐡:
1⃣Filters for HTTP status codes
2⃣File extension targeting
3⃣Super-fast scanning for modern web apps
𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/directory-brute-forcing-using-ffuf/
Want to get hands-on with FFUF and real-world penetration testing? Join Infosec Train 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐏𝐞𝐧𝐞𝐭𝐫𝐚𝐭𝐢𝐨𝐧 𝐓𝐞𝐬𝐭𝐢𝐧𝐠 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 . Learn how pros find vulnerabilities before attackers do.
#FFUF #PenTesting #CyberSecurity #EthicalHacking #InfoSecTrain #BugBounty #CyberAwareness
𝐄𝐯𝐞𝐫 𝐭𝐡𝐨𝐮𝐠𝐡𝐭 𝐚𝐛𝐨𝐮𝐭 𝐡𝐨𝐰 𝐞𝐭𝐡𝐢𝐜𝐚𝐥 𝐡𝐚𝐜𝐤𝐞𝐫𝐬 𝐝𝐢𝐬𝐜𝐨𝐯𝐞𝐫 𝐬𝐞𝐜𝐫𝐞𝐭 𝐚𝐝𝐦𝐢𝐧 𝐩𝐚𝐧𝐞𝐥𝐬 𝐚𝐧𝐝 𝐡𝐢𝐝𝐝𝐞𝐧 𝐟𝐢𝐥𝐞𝐬 𝐢𝐧 𝐰𝐞𝐛𝐬𝐢𝐭𝐞𝐬?
Looking for hidden doors in a website ethically and effectively? 𝐅𝐅𝐔𝐅 (𝐅𝐚𝐬𝐭 𝐖𝐞𝐛 𝐅𝐮𝐳𝐳𝐞𝐫) 𝐢𝐬 𝐚 𝐩𝐨𝐩𝐮𝐥𝐚𝐫 𝐭𝐨𝐨𝐥 𝐟𝐨𝐫 𝐩𝐞𝐧𝐞𝐭𝐫𝐚𝐭𝐢𝐨𝐧 𝐭𝐞𝐬𝐭𝐞𝐫𝐬 𝐚𝐧𝐝 𝐛𝐮𝐠 𝐡𝐮𝐧𝐭𝐞𝐫𝐬 that can be used to discover hidden directories, left behind files, and web vulnerabilities.
𝐇𝐨𝐰 𝐈𝐭 𝐖𝐨𝐫𝐤𝐬:
1⃣ FFUF takes words from a wordlist
2⃣ Injects them into URLs
3⃣Watches how the website responds
𝐅𝐅𝐔𝐅 𝐡𝐞𝐥𝐩𝐬 𝐞𝐭𝐡𝐢𝐜𝐚𝐥 𝐡𝐚𝐜𝐤𝐞𝐫𝐬:
✅ Find admin panels
✅ Discover exposed files
✅ Identify misconfigurations
✅ Strengthen website security before attackers strike
𝐅𝐅𝐔𝐅 𝐥𝐞𝐭𝐬 𝐲𝐨𝐮 𝐫𝐞𝐟𝐢𝐧𝐞 𝐲𝐨𝐮𝐫 𝐬𝐜𝐚𝐧 𝐰𝐢𝐭𝐡:
1⃣Filters for HTTP status codes
2⃣File extension targeting
3⃣Super-fast scanning for modern web apps
👉 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐝𝐞𝐭𝐚𝐢𝐥𝐞𝐝 𝐚𝐫𝐭𝐢𝐜𝐥𝐞 𝐡𝐞𝐫𝐞: https://www.infosectrain.com/blog/directory-brute-forcing-using-ffuf/
Want to get hands-on with FFUF and real-world penetration testing? Join Infosec Train 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 𝐏𝐞𝐧𝐞𝐭𝐫𝐚𝐭𝐢𝐨𝐧 𝐓𝐞𝐬𝐭𝐢𝐧𝐠 𝐓𝐫𝐚𝐢𝐧𝐢𝐧𝐠 . Learn how pros find vulnerabilities before attackers do.
#FFUF #PenTesting #CyberSecurity #EthicalHacking #InfoSecTrain #BugBounty #CyberAwareness
0 Commentarii
0 Distribuiri
4642 Views
0 previzualizare