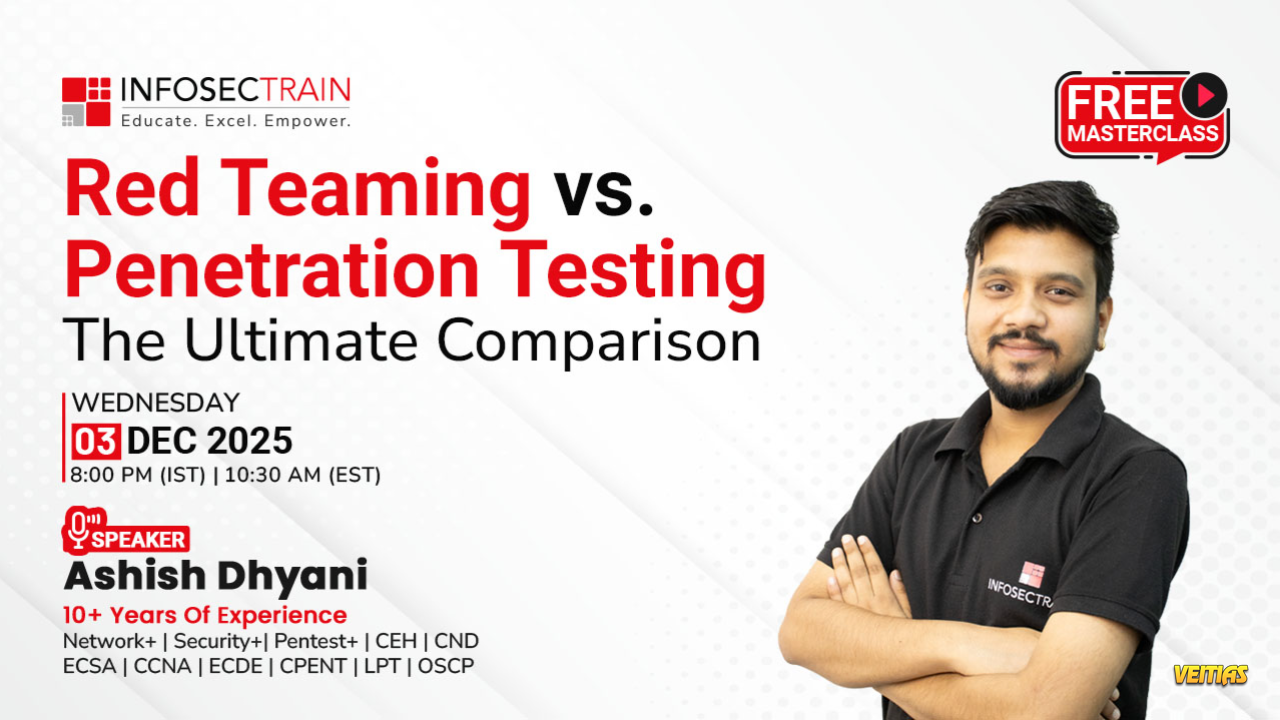
Free Masterclass Alert!
Red Teaming vs Penetration Testing: The Ultimate Comparison
Confused between red teaming and pen testing?
Join us for an eye-opening masterclass where you’ll uncover how each technique works, when to use which, and why both are critical for strengthening your cybersecurity posture!
Date: 03 Dec (Wed)
Time: 08:00 – 09:00 PM (IST)
🎟 Enroll Now: https://www.infosectrain.com/events/red-teaming-vs-penetration-testing-the-ultimate-comparison/
What’s Inside?
✔ Foundations of Offensive Security
✔ Deep Dive into Penetration Testing
✔ Types of Pen Testing
✔ Deep Dive into Red Teaming
✔ Role of the Blue Team
✔ Key Differences in Application
✔ When to Choose Which?
✔ Live Q&A Session
#CyberSecurity #RedTeam #PenTesting #EthicalHacking #DFIR #BlueTeam #ThreatHunting #CyberAttack #SecurityTraining #InfoSecTrain #Masterclass #CyberSkills #OffensiveSecurity
Red Teaming vs Penetration Testing: The Ultimate Comparison
Confused between red teaming and pen testing?
Join us for an eye-opening masterclass where you’ll uncover how each technique works, when to use which, and why both are critical for strengthening your cybersecurity posture!
Date: 03 Dec (Wed)
Time: 08:00 – 09:00 PM (IST)
🎟 Enroll Now: https://www.infosectrain.com/events/red-teaming-vs-penetration-testing-the-ultimate-comparison/
What’s Inside?
✔ Foundations of Offensive Security
✔ Deep Dive into Penetration Testing
✔ Types of Pen Testing
✔ Deep Dive into Red Teaming
✔ Role of the Blue Team
✔ Key Differences in Application
✔ When to Choose Which?
✔ Live Q&A Session
#CyberSecurity #RedTeam #PenTesting #EthicalHacking #DFIR #BlueTeam #ThreatHunting #CyberAttack #SecurityTraining #InfoSecTrain #Masterclass #CyberSkills #OffensiveSecurity
Free Masterclass Alert!
Red Teaming vs Penetration Testing: The Ultimate Comparison
Confused between red teaming and pen testing?
Join us for an eye-opening masterclass where you’ll uncover how each technique works, when to use which, and why both are critical for strengthening your cybersecurity posture!
📅 Date: 03 Dec (Wed)
⏰ Time: 08:00 – 09:00 PM (IST)
🎟 Enroll Now: https://www.infosectrain.com/events/red-teaming-vs-penetration-testing-the-ultimate-comparison/
🔥 What’s Inside?
✔ Foundations of Offensive Security
✔ Deep Dive into Penetration Testing
✔ Types of Pen Testing
✔ Deep Dive into Red Teaming
✔ Role of the Blue Team
✔ Key Differences in Application
✔ When to Choose Which?
✔ Live Q&A Session
#CyberSecurity #RedTeam #PenTesting #EthicalHacking #DFIR #BlueTeam #ThreatHunting #CyberAttack #SecurityTraining #InfoSecTrain #Masterclass #CyberSkills #OffensiveSecurity
0 Yorumlar
0 hisse senetleri
2352 Views
0 önizleme