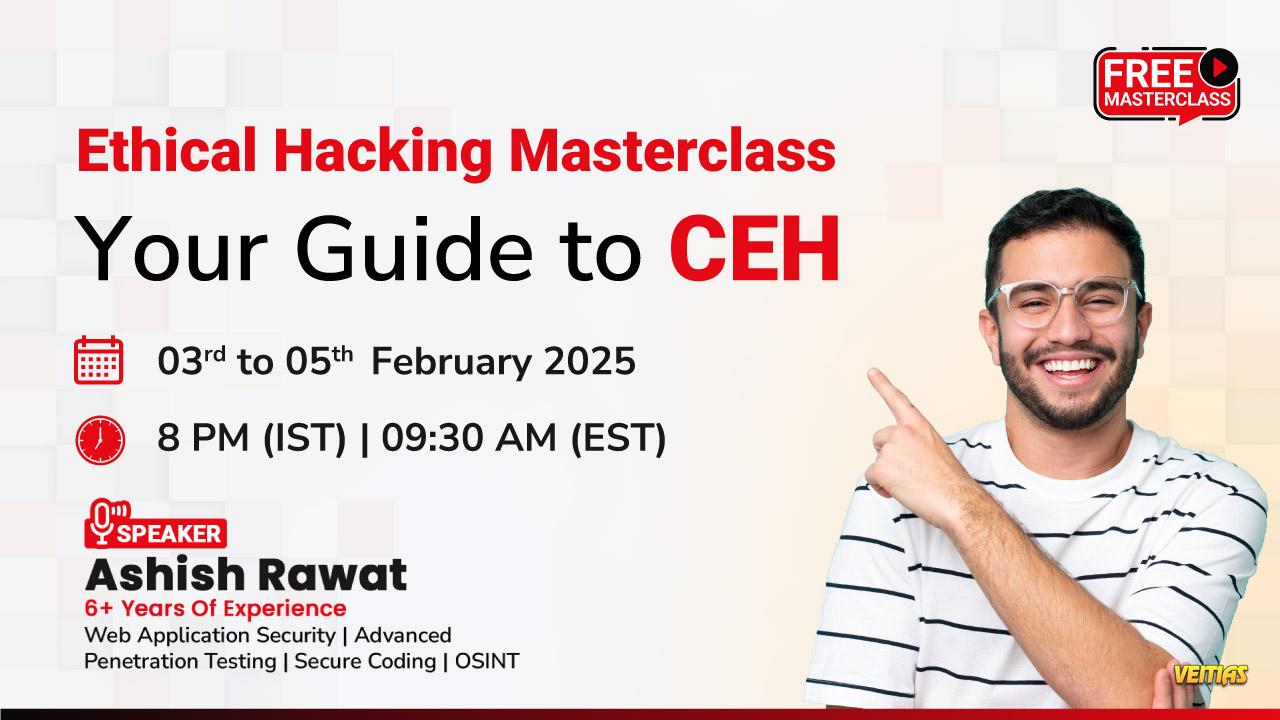
Free Masterclass on Ethical Hacking Masterclass: Your Guide to CEH
Date: 3 to 5 Feb (Mon -Wed)
Time: 08:00 – 10:00 PM (IST)
Speaker: Ashish Rawat
Free Register Now:
https://www.infosectrain.com/events/ethical-hacking-masterclass-your-guide-to-ceh/ Agenda for the Masterclass
DAY 1
Introduction to Ethical Hacking
• What is Security?
• Need for Security?
• Cybersecurity vs Information Security
• Understanding Pillars of Security
• Types of Threat Actors
• Security Teams
• Overview of Penetration Testing process
What is Penetration Testing?
• Strategies of Penetration Testing
• What can be tested? – Web, Mobile, Network, API, etc.
• Phases of ethical hacking
• Cyber Kill Chain
• Why AI-Driven Ethical Hacking?
DAY 2
Introduction to Reconnaissance
• What is Footprinting?
• Types of Footprinting
• Information obtained in Footprinting
• Footprinting through search engines
Overview of Network Scanning
• Discovering live hosts
• Finding open ports
• Banner grabbing
Social Engineering
• What is Social Engineering?
• Types of Social Engineering
• Phishing – Practical
DAY 3
Introduction to Web Application Exploitation
• What is Application?
• Introduction to Web Application
• Website vs Web Application
• How Web Application works?
• HTTP Protocol
• HTTP Request and Response
• OWASP TOP 10
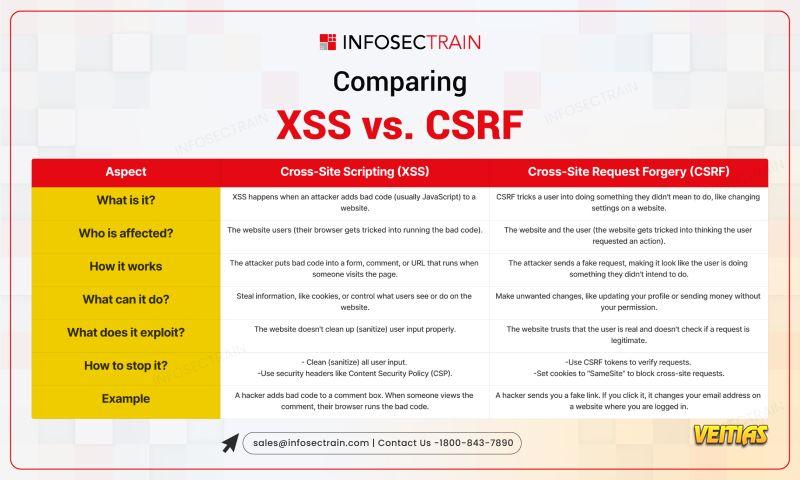
• Injection – SQL injection and XSS injection
• Cross Site Request Forgery (CSRF)
• Introduction to API
• OWASP TOP 10 API
Why Attend This Masterclass
Get CPE Certificate
Learn from Industry Experts
FREE Career Guidance & Mentorship See less
Free Masterclass on Ethical Hacking Masterclass: Your Guide to CEH
📅 Date: 3 to 5 Feb (Mon -Wed)
⌚ Time: 08:00 – 10:00 PM (IST)
Speaker: Ashish Rawat
Free Register Now: https://www.infosectrain.com/events/ethical-hacking-masterclass-your-guide-to-ceh/
➡️ Agenda for the Masterclass
DAY 1
Introduction to Ethical Hacking
• What is Security?
• Need for Security?
• Cybersecurity vs Information Security
• Understanding Pillars of Security
• Types of Threat Actors
• Security Teams
• Overview of Penetration Testing process
What is Penetration Testing?
• Strategies of Penetration Testing
• What can be tested? – Web, Mobile, Network, API, etc.
• Phases of ethical hacking
• Cyber Kill Chain
• Why AI-Driven Ethical Hacking?
DAY 2
Introduction to Reconnaissance
• What is Footprinting?
• Types of Footprinting
• Information obtained in Footprinting
• Footprinting through search engines
Overview of Network Scanning
• Discovering live hosts
• Finding open ports
• Banner grabbing
Social Engineering
• What is Social Engineering?
• Types of Social Engineering
• Phishing – Practical
DAY 3
Introduction to Web Application Exploitation
• What is Application?
• Introduction to Web Application
• Website vs Web Application
• How Web Application works?
• HTTP Protocol
• HTTP Request and Response
• OWASP TOP 10
• Injection – SQL injection and XSS injection
• Cross Site Request Forgery (CSRF)
• Introduction to API
• OWASP TOP 10 API
➡️ Why Attend This Masterclass
👉 Get CPE Certificate
👉 Learn from Industry Experts
👉 FREE Career Guidance & Mentorship See less